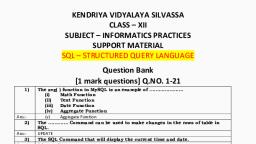
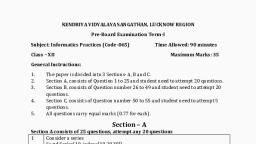
Notes of Grade12, IP IP_Final_XII.pdf - Study Material
Page 2 :
कें द्रीय विद्यालय सगं ठन क्षेत्रीय कायाालय रायपरु, Kendriya Vidyalaya Sangathan Regional Office Raipur, MESSAGE FROM DUPUTY COMMISSIONER, , It is a matter of great pleasure for me to publish study material for different, subjects of classes X and XII for Raipur Region. Getting acquainted and familiarized, with the recent changes in curriculum and assessment process made by CBSE vide, Circular No. 51 and 53 issued in the month of July 2021 will help students to, prepare themselves better for the examination. Sound and deeper knowledge of the, Units and Chapters is must for grasping the concepts, understanding the, questions. Study materials help in making suitable and effective notes for quick, revision just before the examination., Due to the unprecedented circumstances of COVID-19 pandemic the, students and the teachers are getting very limited opportunity to interact face to, face in the classes. In such a situation the supervised and especially prepared value, points will help the students to develop their understanding and analytical skills, together. The students will be benefitted immensely after going through the, question bank and practice papers. The study materials will build a special bond, and act as connecting link between the teachers and the students as both can, undertake a guided and experiential learning simultaneously. It will help the, students develop the habit of exploring and analyzing the Creative & Critical, Thinking Skills. The new concepts introduced in the question pattern related to, case study, reasoning and ascertain will empower the students to take independent, decision on different situational problems. The different study materials are, designed in such a manner to help the students in their self-learning pace. It, emphasizes the great pedagogical dictum that ‘everything can be learnt but nothing, can be taught’. The self-motivated learning as well as supervised classes will, together help them achieve the new academic heights., I would like to extend my sincere gratitude to all the principals and the teachers, who have relentlessly striven for completion of the project of preparing study, materials for all the subjects. Their enormous contribution in making this project, successful is praiseworthy., Happy learning and best of luck!, Vinod Kumar, (Deputy Commissioner), , 2|Page
Page 5 :
TABLE OF CONTENTS, , TERM - 1, , S., , TERM - 2, , No., , 1, , (Click the LINK to directly reach, the content), DISTRIBUTION OF MARKS, , Page, Number, 06, , (Click the LINK to directly reach the, content), DISTRIBUTION OF MARKS, , Page Number, , 2, , SYLLABUS, , 07-08, , SYLLABUS, , 09-10, , 3, , DATA HANDLING USING, , 11-46, , DATABASE QUERY USING SQL, , 92-119, , INTRODUCTION TO COMPUTER, NETWORKS, MODEL QUESTION PAPER, , 120-136, , 06, , PANDAS AND DATA, VISUALIZATION, 4, , SOCIETAL IMPACTS, , 47-68, , 5, , MODEL QUESTION PAPER, , 69-91, , SET 1, , SET 1, , SET 2, , SET 2, , SET 3, , SET 3, , 5|Page, , 137-156
Page 6 :
Informatics Practices CLASS XII, Code No. 065, , 2021-2022, , 1. Prerequisite: Informatics Practices – Class XI, 2. Learning Outcomes, At the end of this course, students will be able to:, ● Create Series, Data frames and apply various operations., ● Visualize data using relevant graphs., ● Design SQL queries using aggregate functions., ● Learn terminology related to networking and the internet., ● Identify internet security issues and configure browser settings, ● Understand the impact of technology on society including gender and disability issues., , 3. Distribution of Marks and Periods:, , Unit, No, , Unit Name, , Marks, , Periods, , Periods, , Total, , Theory, , Practical, , Period, , 1, , Data Handling using Pandas and Data, Visualization, , 25, , 25, , 25, , 50, , 2, , Database Query using SQL, , 25, , 20, , 17, , 37, , 3, , Introduction to Computer Networks, , 10, , 12, , 0, , 12, , 4, , Societal Impacts, , 10, , 14, , -, , 14, , Project, , -, , -, , 7, , 7, , Practical, , 30, , -, , -, , -, , Total, , 100, , 71, , 49, , 120, , 6|Page
Page 7 :
Syllabus for Term – 1, , Distribution of Theory Marks, , Unit No, , Unit Name, , Marks, , 1, , Data Handling using Pandas and, Data Visualization, , 25, , 4, , Societal Impacts, , 10, , Total, , 35, Unit 1:, , Data Handling using Pandas and Data Visualization Data, Handling using Pandas -I, ● Introduction to Python libraries- Pandas, Matplotlib., ● Data structures in Pandas - Series and data frames. Series: Creation of series from dictionary,, scalar value; mathematical operations; series attributes, head and tailfunctions; selection,, indexing and slicing., ● Data Frames: creation of data frames from dictionary of series, list of dictionaries, text/CSV files,, display, and iteration. Operations on rows and columns: add (insert /append), select, delete (drop, column and row), rename, Head and Tail functions, indexing using labels, Boolean indexing., Data Visualization, ● Data Visualization: Purpose of plotting, drawing and saving of plots using Matplotlib (line plot,, bar graph, histogram). Customizing plots: adding label, title, and legend in plots., Unit 4:, Societal Impacts, ● Digital footprint, net and communication etiquettes,, ● Data protection, intellectual property rights (IPR), plagiarism, licensing and copyright,, ● Free and open source software (FOSS),, ● Cybercrime and cyber laws, hacking, phishing, cyber bullying, overview of Indian IT Act., ● E-waste: hazards and management. Awareness about health concerns related to the usage of, technology., , 7|Page
Page 8 :
Distribution of Practical Marks, , Topic, , Marks, , Pandas program (pen and paper or Collab or any online idle or pyroid screen for mobile), , 8, , Practical File 15 Pandas Programs, , 3, , Project synopsis, , 2, , Viva, , 2, , Total, , 15, , Suggested Practical List, Data Handling, 1. Create a panda’s series from a dictionary of values and a ndarray, 2. Given a Series, print all the elements that are above the 75th percentile., 3. Create a Data Frame quarterly sales where each row contains the item category, item name,, and expenditure. Group the rows by the category and print the total expenditure per category., 4. Create a data frame for examination result and display row labels, column labels data types of, each column and the dimensions, 5. Filter out rows based on different criteria such as duplicate rows., 6. Importing and exporting data between pandas and CSV file, Visualization, 1. Given the school result data, analyses the performance of the students on different parameters,, E.g. subject wise or class wise., 2. For the Data frames created above, analyse, and plot appropriate charts with title and legend., 3. Take data of your interest from an open source (e.g. data.gov.in), aggregate and summarize it., Then plot it using different plotting functions of the Matplotlib library., Project Synopsis, The synopsis should cover the brief description about the project along with reasons for selection of the, dataset. The learner should write the source of the dataset whether created or taken from any reliable, source. The learner should write what analytics can be done on the project., ., Syllabus for Term – 2, 8|Page
Page 9 :
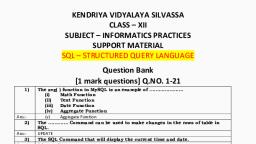
Distribution of Theory Marks, Unit No, , Unit Name, , Marks, , 2, , Database Query using SQL, , 25, , 3, , Introduction to Computer Networks, , 10, , Total, , 35, , Unit 2:, Database Query using SQL, , •, , Math functions: POWER (), ROUND (), MOD ()., • Text functions: UCASE ()/UPPER (), LCASE ()/LOWER (), MID ()/SUBSTRING ()/SUBSTR (), LENGTH, (), LEFT (), RIGHT (), INSTR (), LTRIM (), RTRIM (), TRIM ()., • Date Functions: NOW (), DATE (), MONTH (), MONTHNAME (), YEAR (), DAY (),, DAYNAME (). Aggregate Functions: MAX (), MIN (), AVG (), SUM (), COUNT (); using, COUNT (*)., • Querying and manipulating data using Group by, Having, Order by., Unit 3:, Introduction to Computer Networks, •, •, •, •, •, •, , Introduction to networks, Types of network: LAN, MAN, WAN., Network Devices: modem, hub, switch, repeater, router, and gateway., Network Topologies: Star, Bus, Tree, Mesh., Introduction to Internet, URL, WWW and its applications- Web, email, Chat, VoIP., Website: Introduction, difference between a website and webpage, static vs dynamic web, page, web server and hosting of a website., Web Browsers: Introduction, commonly used browsers, browser settings, add-ons and plugins, cookies., Distribution of Practical Marks, Topic, , Marks, , SQL queries (pen and paper), , 7, , Practical File – 12 SQL Queries, , 2, , Final Project Submission, , 3, , Viva, , 3, , Total, , 9|Page, , 15
Page 10 :
Suggested Practical List, Data Management, 1. Create a student table with the student id, name, and marks as attributes where the student id is the, primary key., 2. Insert the details of a new student in the above table., 3. Delete the details of a student in the above table., 4. Use the select command to get the details of the students with marks more than 80., 5. Find the min, max, sum, and average of the marks in a student marks table., 6. Find the total number of customers from each country in the table (customer ID, customer, Name, country) using group by., 7. Write a SQL query to order the (student ID, marks) table in descending order of the marks., Project Work, The aim of the class project is to create tangible and useful IT applications. The learner may, Identify a real-world problem by exploring the environment. E.g. Students can visit shops/business places,, communities or other organizations in their localities and enquire about the functioning of the organization,, and how data are generated, stored, and managed., The learner can take data stored in csv or database file and analyze using Python libraries and generate, appropriate charts to visualize. If an organization is maintaining data offline, then the, Learner should create a database using MySQL and store the data in tables., Data can be imported in Pandas for analysis and visualization. Learners can use Python libraries of their, choice to develop software for their school or any other social good. Learners should be sensitized to avoid, plagiarism and violation of copyright issues while working on projects. Teachers should take necessary, measures for this. Any resources (data, image etc.) used in the project, Must be suitably referenced., The project can be done individually or in groups of 2 to 3 students. The project should be started by, students at least 6 months before the submission deadline., , 10 | P a g e
Page 11 :
Term – 1, Data Handling using Pandas and Data Visualization, Unit No, , 1, , Unit Name, Data Handling using Pandas and Data Visualization, , Marks, 25, , Data Handling using Pandas -I, ● Introduction to Python libraries- Pandas, Matplotlib., , ● Data structures in Pandas - Series and data frames.Series: Creation of series from dictionary, scalar value;, mathematical operations; series attributes, head and tail functions; selection, indexing and slicing., ● Data Frames: creation of data frames from dictionary of series, list of dictionaries, text/CSV files, display,, iteration. Operations on rows and columns: add ( insert /append) , select, delete (drop column and row),, rename, Head and Tail functions, indexing using labels, Boolean indexing., , ● Data Visualization : Purpose of plotting, drawing and saving of plots using Matplotlib (line plot, bar, graph, histogram). Customizing plots:; adding label, title, and legend in plots., , TYPE A OBJECTIVE TYPE QUESTIONS, , [1 Mark], , 1. To create an empty Series object, you can use:, (a) pd.Series(empty), (c) pd.Series( ), (b) pd.Series(np.NaN), (d) all of these, , ANS:- (c) pd.Series( ), 2. To specify datatype int16 for a Series object, you can write :, (a) pd.Series(data = array, dtype = int16), (b) pd.Series(data = array, dtype = numpy.int16), (c) pd.Series(data = array.dtype pandas.int16), (d) all of the above, , ANS:- (b) pd.Series(data = array, dtype = numpy.int16), 11 | P a g e, , Multiple Choice Questions
Page 12 :
3. To get the number of dimensions of a Series object,, (a) index, (b) size attribute is displayed., (c) itemsize, (d) ndim, , ANS:- d) ndim, , 4. To get the size of the datatype of the items in Series object, you can display attribute., (a) index, (b) size, (c) itemsize, (d) ndim, ANS:- (c) itemsize, , 5. To get the number of elements in a Series object, attribute may be used., (a) index, (b) size, (c) itemsize, (d) ndim, ANS:- (b) size, , 6. To get the number of bytes of the Series data, attribute is displayed., (a) hasnans, (b) nbytes, (c) ndim, (d) dtype, , ANS:- b) nbytes, , 12 | P a g e
Page 13 :
7 .To check if the Series object contains NaN values, attribute is displayd., (a) hasnans, (b) nbytes, (c) ndim, (d) dtype, , ANS:- a) hasnans, , 8. To display third element of a Series object S, you will write, (a) S[:3], (b) S[2], (c) S[3], (d) S[:2], , ANS:- (b) S[2], , 9. To display first three elements of a Series object S, you may write, (a) S[:3], (b) S[3], (c) S[3rd], (d) all of these, , ANS:- (a) S[:3], , 10. To display last five rows of a Series object S, you may write, (a) head(), (b) head(5), (c) tail( ), (d) tail(5), , ANS:- (c) tail( ) and (d) tail(5), , 13 | P a g e
Page 14 :
11. Pandas object cannot grow in size., (a) Dataframe, , (b) Panel, , ( c) Series, , (d) None of these, , ANS. ( c) Series, , 12. Given a Pandas series called Sequences, the command which will display the first 4 rows is, (a) print(Sequences.head(4)), (b) print(Sequences.Head (4)), (c) print(Sequences.heads(4)), (d)print(Sequences.Heads (4)), , ANS:- (a) print(Sequences.head(4)), , 13. If a Dataframe is created using a 2D dictionary, then the indexes/row labels are formed from, (a) dictionary's values, (b) inner dictionary's keys, (c) outer dictionary's keys, (d) none of these, , ANS:- (b) inner dictionary's keys, , 14. If a dataframe is created using a 2D dictionary, then the column labels are formed from, (a) dictionary's values, (b) inner dictionary's keys, (c) outer dictionary's keys, (d) none of these, , ANS:- (c) outer dictionary's keys, , 14 | P a g e
Page 15 :
15. The axis 0 identifies a dataframe's, (a) rows, (b) columns, (c) values, (d) datatype, , ANS:- (a) rows, , 16. The axis 1 identifies a dataframe's, (a) row, , (b) columns (c) values (d) datatype, , ANS:- (b) columns, , 17. To get the number of elements in a dataframe,, (a) size, (b) shapeartribute may be used., (c) values, (d) ndim, ANS:- (a) size, , 18. To get a number representing number of axes in a dataframe, used. attribute may be, (a) size, (b) shape, (c) values, (d) ndim, , ANS:- d) ndim, , 19. To extract row/column from a dataframe,, (a) row( ), , (b) column( ), , ANS:- (a) row( ), 15 | P a g e, , (c) loc( ), , (d) all of these
Page 16 :
21.. To display the 3rd, 4th and 5th columns from the 6th to 9th rows of a dataframe you can write, (a) DF.loc[6:9, 3:5], (b) DF.loc[6:10, 3:6], (c) DF.iloc[6:10, 3:6], (d) DF.iloc[6:9, 3:5], , ANS:- c) DF.iloc[6:10, 3:6], , 22. To change the 5th column's value at 3rd row as 35 in dataframe DF, you can write, , (a) DF[4, 6] = 35, (b) DF.iat[4, 6] = 35, (c) DF[3, 5] = 35, (d) DF.iat[3, 5] = 35, , ANS:- d) DF.iat[3, 5] = 35, , 23. Which among the following options can be used to create a DataFrame in Pandas ?, (a) A scalar value, (b) An ndarray, (c) A python dict, (d) All of these, , ANS:- (d) All of these, , 24. Identify the correct statement:, (a) Data frames can change their size., (b) Series act in a way similar to that of an array., ( (c) Both (a) and b), (d) None of the above, , ANS:- ( (c) Both (a) and b), 16 | P a g e
Page 17 :
25. To delete a column from a DataFrame, you may use statement., (a) remove, (b) del, (c) drop, (d) cancel statement., , ANS:- (b) del, , 26. To delete a row from a DataFrame, you may use, (a) remove, (b) del, (c) drop, (d) cancel, , ANS:- (c) drop, , 27. To iterate over horizontal subsets of dataframe,, (a) iterate( ), (b) iterrows( ) function may be used., (c) itercols( ), (d) iteritems( ), , ANS:- (b) iterrows( ) function may be used., , 28. To iterate over vertical subsets of a dataframe, function may be used., (a) iterate( ), (b) iterrows( ), (c) itercols( ), (d) iteritems( ), , ANS:- (d) iteritems( ), 17 | P a g e
Page 18 :
29. To add two dataframes' values,, (a) plus function may be used., (b) rplus, (c) add, (d) radd, , ANS:- c) add ,(d) radd, , 30. To subtract the values of two dataframes,, (a) sub, (b) difference, (c) minus, (d) rsub, , ANS:- (a) sub, d) rsub, , 31. To divide the values of two dataframes, function may be used. function may be used., (a) divide, (b) div, (c) rdiv, (d) division, , ANS:- (b) div , c) rdiv, , 32. Which of the following two functions will produce the same result ?, (a) add, (b) radd, (c) sub, (d) rsub, , ANS:- (a) add, b) radd, 18 | P a g e
Page 19 :
33. To get the 3 bottommost rows from a dataframe, you may use, (a) bottom, (b) bottom, (3) function., (c) tail( ), , ANS:- b) radd, , 34. Which of the following arguments lets you specify index labels of dataframe through Dataframe( ) ?, (a) index, (b) columns, (c) label, (d) all of these function., , ANS:- (a) index, , 35. To get top 5 rows of a dataframe, you may use, (a) head( ), (b) head(5), (c) top( ), (d) top(5), , ANS:- (a) head( ) , b) head(5), , 36. Which of the following can be used to specify data for creating a Dataframe ?, (a) Series, (b) DataFrame, (c) Structured ndarray, (d) All of these, , ANS:- (d) All of these, 19 | P a g e
Page 20 :
37. All Pandas' data structures are mutable but not always mutable., (a) size, value, (b) semantic, size, (c) value, size, (d) none of these, ANS:- (c) value, size, 38. Which of the following statement will import Pandas library ?, (a) import pandas as pd, (b) import pandas as py, (c) import panda as py, (d) All of these, ANS:- (a) import pandas as pd ,(b) import pandas as py, 39. What will be the output for the following code ?, import pandas as pd, S = pd. Series([1,2,3,4,5],index = ['a', 'b', 'c', 'd', 'e']), print ( s[ 'a'] ), (a) 2, (b) 1, (c) 3, (d) 4, ANS:- (b) 1, 40. What will be the output for the following code ?, import pandas as pd, import numpy as np, S = pd.Series (np.random.randn(2)), print (s.size), (a) 0, (b) 1, (c) 2, (d) 3, , ANS:- (c) 2, , 20 | P a g e
Page 21 :
41. What will be the output for the following code ?, import pandas as pd i, mport numpy as np, S= pd.Series(np.random.randn(4)), print (s.ndim), (a) 0, (b) 1, (c) 2, (d) 3, ANS:- b) 1, 42. What is the purpose of using ndimattribute ?, (a) It returns the number of elements in the given data structure., (b) It returns the Series object in the form of an ndarray., (c) It returns a list of the indexes / labels., (d) It returns the number of dimensions of the given data structure., ANS:- (d) It returns the number of dimensions of the given data structure., 43. PyPlot is an interface of Python's., (a) seaborn, (b) plotly library., (c) ggplot, (d) matplotlih, ANS:- (d) matplotlih, , 44. For 2D plotting using a Python library, which library interface is often used ,, , (a) seaborn, (b) plotly, (c) matplotlib, (d) matplotlib.pyplot, , ANS:- d) matplotlib.pyplot, , 21 | P a g e
Page 22 :
45. Which of the following is not a valid chart type ?, (a) Statistical, (b) Box, (c) Pie, (d) plot( ), , ANS:- (a) Statistical , (b) Box, , 46. Which of the following is not a valid plotting function of pyplot ?, (a) pie( ), (b) plot( ), (c) bar( ), (d) line( ), , ANS:- d) line( ), , 47. Which of the following plotting functions does not plot multiple data series ?, (a) plot( ), (b) barh( ), (c) bar( ), (d) pie( ), , Ans:- (d) pie( ), , 48. The plot which tells the trend between two graphed variables is the, (a) scatter graph/chart., (b) pie, (c) bar, (d) line, , ANS:- (d) line, , 22 | P a g e
Page 23 :
49. Which of the following functions is used to create a line chart ?, (a) line( ), (b) plot( ), (c) chart(), (d) plotline( ), , ANS:- b) plot( ), , 50. Which of the following function will produce a bar chart ?, (a) plotbar( ), (b) plot( ), (c) bar( ), (d) barh( ), , ANS:- (c) bar( ), , 51. Which of the following function will create a vertical bar chart ?, (a) plot( ), (b) bar( ), (c) plotbar(), (d) barh( ), , ANS:- (b) bar( ), 52. Which of the following function will create a horizontal bar chart ?, (a) plot( ), (b) bar( ), (c) plotbar( ), (d) barh( ), , ANS:- (d) barh( ), 23 | P a g e
Page 24 :
53. The data points plotted on a graph are called, (a) points, (b) pointers, (c) marks graph is a type of chart which displays information as a series of data points, (d) markers, , ANS:- (d) markers, , 54. A connected by straight line segments., (a) line, (b) bar, (c) pie, (d) boxplot, , ANS:- a) line, , 55. Which argument of bar() lets you set the thickness of bar ?, (a) thick, (b) thickness, (c) width, (d) barwidth, , ANS:- (c) width, , 56. Which function lets you set the title of the plot ?, (a) title( ), (b) graphtitle()., (c) plottitle( ), (d) All of these, , ANS:- (a) title( ), 24 | P a g e
Page 25 :
57. The command used to give a heading to a graph is, (a) plt.show(), (b) plt.plot(), (c) plt.xlabel( ), (d) plt.title( ), ANS:- d) plt.title( ), 58. Which function would you use to set the limits for x-axis of the plot?, (a) limits( ), (b) xlimits( ), (c) xlim(), (d) lim( ), ANS:- c) xlim(), 59. Which function is used to show legends?, (a) display( ), (b) show( ), (c) legend( ), (d) legends( ), ANS.- c) legend( ), , 60. Which argument must be set with plotting functions for legend( ) to display the legends ?, (a) data, , (b) label, , (c) name, , ANS:- (b) label, , 61. Which function is used to create a histogram ?, (a) histogram( ), (b) histo( ), (c) hist(), (d) histtype, , ANS:- (c) hist(), , 25 | P a g e, , (d) sequence
Page 26 :
62. Which of the following is not a valid plotting function of pyplot ?, (a) plot( ), (b) bar( ), (c) line(), (d) pie( ), ANS:- (c) line(), 63. Which of the following plotting functions does not plot multiple data series ?, (a) plot( ), (b) bar( ), (c) pie(), (d) barh( ), ANS:- (c) pie(), 64. The plot which tells the trend between two graphed variables is the graph/chart., (a) line, (b) scatter, (c) bar, (d) pie, , ANS:- (a) line, , 65. A CSV file can take character as separator., (a), (b) -, , (c) I, , (d) \t, , (e) only (a), , (f) all of these, , ANS:- (f) all of these, , 66. In order to work with CSV files from Pandas, you need to import pandas. , other than, (a) csv, (b) pandas.io, (c) no extra package required, (d) newcsv, ANS:- (d) newcsv, , 26 | P a g e
Page 27 :
67. The correct statement to read from a CSV file in a dataframeis :, (a) <DF>.read_csv(<file>), (b) <File>. read_csv( )(<DF>), (c) <DF> = pandas.read(<file>), (d) <DF> = pandas.read_csv(<files>), ANS:- (d) <DF> = pandas.read_csv(<files>), , 68. Which argument do you specify with read_csv( ) to specify a separator character ?, (a) character, (b) char, (c) separator, (d) sep, , ANS:- (d) sep, , 69. To suppress first row as header, which of the following arguments is to be given in read_csv( ) ?, (a) noheader = True, (b) header = None, (c) skipheader = True, (d) header - Null, ANS:- (b) header = None, , 70. To read specific number of rows from a CSV file, which argument is to be given in read_csv( ) ?, (a) rows = <n>, (b) nrows = <n>, (c) n_rows - <n>, (d) number_rows = <n>, ANS:- (b) nrows = <n>, , 27 | P a g e
Page 28 :
71, To skip first 5 rows of CSV file, which argument will you give in read_csv( ) ?, (a) skip_rows = 5, (b) skiprows = 5, (c) skip - 5, (d) noread - 5, , ANS:- (a) skip_rows = 5, , 72. To skip 1st, 3rd and 5th rows of CSV file, which argument will you give in read_csv( ) ?, (a) skiprows = 11315, (b) skiprows - (1, 3, 5], (c) skiprows = [1, 5, 1], (d) Any of these, ANS:- (b) skiprows - (1, 3, 5], , 73. While reading from a CSV file, to use a column's values as index labels, argument, given in read_CSV( ) is :, , (a) index, (b) index_col, (c) index_values, (d) index_label, , ANS:- (b) skiprows - (1, 3, 5], , 74. While writing a dataframe onto a CSV file, which argument would you use in to sql() for NaN values', representation as NULL?, , (a) NaN = NULL, (b) na_rep = NULL, (c) na_value = NULL, (d) na = NULL, ANS:- b) na_rep = NULL, 28 | P a g e
Page 29 :
75. Which of the following command is used to install Pandas?, a) Pip install python-pandas, b) Pip install pandas, c) Python install python, d) Pip install pandas, ANS:- d) Pip install pandas, , 76. A two-dimension labelled array that is an ordered collection of columns to store heterogeneous, datatype is, i. Series, ii. Numpy array, iii. Dataframe, iv. Panel, ANS:- iii. Dataframe, 77. Which of the following statement is false:, i. DataFrame is size mutable, ii. DataFrame is value mutable, iii. DataFrame is immutable, iv. DataFrame is capable of holding multiple types of data, ANS:- iii. DataFrame is immutable, 78.CSV stands for:, i. Comma separated value, ii. Comma separated variables, iii. Column separated values, iv. Column separated variables, ANS:- i. Comma separated value, , 79.Which method is used to access vertical subset of a dataframe?, i. iterrows(), ii. iteritems(), iii. mod(), iv. median(), , ANS:- ii. iteritems(), , 29 | P a g e
Page 30 :
80. Which method is used to access horizontal subset of a dataframe?, i. iterrows(), ii. iteritems(), iii. mod(), iv. median(), , ANS:- i. iterrows(), 81. Which function is used to rename an existing column or index?, i, std(), ii, hist(), iii, groupby(), iv, rename(), ANS:- rename( ), , 82. To create an empty series object you can use:, i. pd.Series(empty), ii. pd.Series(np.NaN), iii. pd.series(), iv. All of these, , ANS:- iii. pd.series(), , 30 | P a g e
Page 31 :
TYPE B -( FILL IN THE BLANKS), , [1 Mark], , Multiple Choice Questions, , 83.To delete a column from a dataframe, you may use ______ statement., i. remove(), ii. del(), iii. drop(), iv. cancel(), , ANS:- iii. drop(), 84. To delete a row from dataframe, you may use _______ statement., i. remove(), ii. del(), iii. drop(), iv. cancel(), , ANS:- ii. del(), 85.To add two dataframes’ values, ______ function may be used., i. plus, ii. eplus, iii. add, iv. radd, , ANS:- iv. radd, , 86.To skip NaN values in a calculation you can specify ________ attribute, i. NaN, ii. Na, iii. skipna, iv. All of these, , ANS:- iv. All of these, , 31 | P a g e
Page 32 :
87. The function to create histograms for all numeric columns of a dataframe is ______, i. histogram(), ii. hist(numeric_only=True), iii. hist(), iv. All of these, , ANS:- ii. hist(numeric_only=True), 88. The plot which tells the correlation between two variables which may not be directly related is, _____ graph/chart., i. line, ii. scatter, iii. bar, iv. pie, , ANS:- ii. scatter, 89. Which of the following function is used to create a line chart?, i. line, ii. plot, iii. chart, iv. plotline, ANS:- ii. plot, 90. Which of the following produce a bar chart?, i. plot, ii. bar, iii. plotbar, iv. barh, , ANS:- ii. bar, 91. A _____ graph is a type of chart which displays information as a series of data points, connected by straight line segments., i. line, ii. bar, iii. pie, iv. boxplot, , ANS:- i. line, 32 | P a g e
Page 33 :
92. A CSV file can take ______ character as separator., i. ,, ii. _, iii. !, iv. \t, v. All of these, , ANS:- v. All of these, , 93. In order to work with CSV files from panda, we need to import, i. .csv, ii.pandas.io, iii. newcsv, iv. No extra module required, , ANS:- i. .csv, , 94. Best way to import pandas in our program is _____, a)import pandas, b) import pandas as p, c) from pandas import *, d) All of the above, ANS:- d) All of the above, , 95. In given code dataframe ‘D1’ has ________ rows and ______ columns., import pandas as pd, LoD = [{‘a’:10, ‘b’:20}, {‘a’:5, ‘b’:10, ‘c’:20}, {‘a’:7, ‘d’:10, ‘e’:20}], D1 = pd.DataFrame(LoD), a. 3, 3, b. 3, 4, c. 3, 5, d. None of the above, , ANS:- c. 3, 5, 33 | P a g e
Page 34 :
96.D1[ : ] = 77 , will set __________ values of a DataFrame ‘D1’ to 77., a. Only First Row, b. Only First Column, c. All, d. None of the above, , ANS:- c. All, , 97. The following statement will _________, df = df.drop(['Name', 'Class', 'Rollno'], axis = 1), #df is a DataFrame object, a. delete three columns having labels ‘Name’, ‘Class’ and ‘Rollno’, b. delete three rows having labels ‘Name’, ‘Class’ and ‘Rollno’, c. delete any three columns, d. return error, , ANS:- a. delete three columns having labels ‘Name’, ‘Class’ and ‘Rollno’, , 98. Which of the following are ways of indexing to access Data elements in a DataFrame?, a. Label based indexing, b. Boolean Indexing, c. All of the above, d. None of the above, , ANS:- c. All of the above, 99. The following statement will display ________ rows of DataFrame ‘DF’, print(df.loc[[True, False,True]]), a. 1 b. 2 c. 3, d. 4, , ANS:- b. 2, , 34 | P a g e
Page 35 :
100. NumPy stands for ____, a.Number Python, b. Numerical Python, c. Numbers in Python, d. None of the aboveS., ANS. b numerical python, 101. PANDAS stands for _____________, , a. Panel Data Analysis, , b. Panel Data analyst, c. Panel Data, d. Panel Dashboard, ANS. c panel data, 102. _________ is used when data is in Tabular Format, , a. NumPy, b. Pandas, c. Matplotlib, d. All of the above, ANS. b. Pandas, 103. When you print/display any series then the left most column is showing _________ value., a. Index, b. Data, c. Value, d. None of the above, , ANS:- a .index, 104. When we create a series from dictionary then the keys of dictionary become ________________, a. Index of the series, b. Value of the series, c. Caption of the series, d. None of the series, ANS;- a. Index of the series, , 35 | P a g e
Page 36 :
Case Study Based Question, Q-1, Mr. Ankit is working in an organization as data analyst. He uses Python Pandas and Matplotlib for, the same. He got a dataset of the passengers for the year 2010 to 2012 for January, March and, December. His manager wants certain information from him, but he is facing some problems. Help, him by answering few questions given below:, , Code to create the above data frame:, import pandasas ____________ #Statement 1, data={"Year":[2010,2010,2012,2010,2012],"Month":["Jan","Mar","Jan","Dec","Dec"], ,"Passengers":[25,50,35,55,65]}, df=pd.____________________(data) #Statement 2, print(df), 1. He wants to print the details of "January" month along with the number of passengers,, Identify the correct statement:, , i. .df.loc[['Month','Passengers']] [df['Month’] =='Jan’], ii. df[['Month','Passengers']][df['Month’] =='Jan'], iii. df. iloc[['Month','Passengers']][df['Month’] =='Jan'], iv. df(['Month','Passengers']][df['Month']=='Jan'), 2. Mr. Ankit wants to change the index of the Data Frame and the output for the same is given, below. Identify the correct statement to change the index, , 36 | P a g e
Page 38 :
UT4, a. print(df.max), b. print(df.max()), c. print(df.max(axis=1)), d. print(df.max, axis=1), , 2. The teacher needs to know the marks scored by the student with roll number.Help her to identify the, correct set of statement/s from the given options, a. df1=df[df[‘rollno’]==4], print(df1), b. df1=df[rollno==4], print(df1), c . df1=df[df.rollno=4], print(df1), d. df1=df[df.rollno==4], print(df1), 3. Which of the following statement/s will give the exact number of values ineach column of the, dataframe?, i), print(df.count()), ii), print(df.count(0)), iii), print(df.count), iv), print(df.count(axis=’index’)), Choose the correct option:, a. both (i) and (ii), b. only (ii), c. (i), (ii) and (iii), d. (i), (ii) and (iv), 4. Which of the following command will display the column labels of thedataframe?, i) print(df.columns()), ii) print(df.column()), iii) print(df.column), iv) print(df.columns), 5. Ms. Sharma, the class teacher wants to add a new column, the scores of Gradewith the values, ‘ A’,, ‘B’, ‘A’, ‘A’, ‘B’, ‘A’choose the command to do so:, a)df.column=[’A’,’B’,’A’,’A’,’B’,’A’], b)df [‘Grade’]=[’A’,’B’,’A’,’A’,’B’,’A’], c) df.loc[‘Grade’]= [’A’,’B’,’A’,’A’,’B’,’A’], d) Both (b) and (c) are correct, , ANS:- 1. b. print(df.max()), 2. a. df1=df[df[‘rollno’]==4], print(df1), d. df1=df[df.rollno==4], 38 | P a g e
Page 40 :
b.dfmks.sort_value(by=[‘A’]), c.dfmks.sortvalues(by=[‘A’]), d.dfmks.sort_values(by=[‘A’]), , 5.Which library is necessary to import for above DataFrame., a., b., c., d., , Import matplotlib, Import pandas, Import csv, Import dataframe, , ANS:- 1. c.dfmks.fillna(0), 2. b.dfmks.dropna(), 3. a.dfmks.isnull(), 4. d.dfmks.sort_values(by=[‘A’]), 5. b.import pandas, , Q-4.Consider the following DataFrame df and answer any four questions, Fruits, Pulses, Rice, Andhra p., 7830, 931.0, 7452.4, i), Gujarat, 11950, 818.0, 1930.0, Kerala, 113.1, 1.7, 2604.8, Punjab, 7152, 33., 11586.2, Tripura, 44.1, 23.2, 814.6, Uttar p., 140169.2, 2184.4, 13754.0, Write down the command to find minimum value along the columns for each row., , Wheat, NaN, 2737.0, NaN, 16440.5, 0.5, 30056.0, , a.df.min(), b.df.min(axis=1), c.df.min(axis=0), d.df.min(column), ii) Which argument is used with max() function for only numeric values are used for calculation., a.NaN=True, b.numerionly=True, c.skipna=True,numeric_value=True, d.skipNaN=True,number_value=True, iii) Select command to delete column wheat., 40 | P a g e
Page 42 :
c.df.at[‘banglore’,:]=1200, d.df.at.banglore=1200, , 2.The output:, 11950, , 818.0, , 113.1, , 1.7, , will be produced by:, a.df.show[1:3,0:2], b.df.at[1:3,0:2], c.df.loc[1:3,0:2], d.df.iloc[1:3,0:2], 3.Which among given option produce output, Andhra p, gujarata, kerala, Punjab, Tripura, uttar p, a.df.count(axis=1), , 3, 4, 3, 4, 4, 4, , b.df.count(axis=0), c.df.count(rows), d.df.count(columns), , ANS:- 1. c.df.at[‘banglore’,:]=1200, 2. d.df.iloc[1:3,0:2], 3. b.df.T, 4. c.median(), 5. df.count(axis=1), , Q-6. Mr.Javed is working in a game software development industry and he was comparing the given chart, on the basis of the rating of the various games available on the play store., , 42 | P a g e
Page 43 :
He is, graph., code and, , trying to write a code to plot the, Help him to fill in the blanks of the, get the desired output., , import__________________________ #Statement 1, Games=["Subway Surfer","Temple Run","Candy Crush","Bottle Shot","Runner Best"], Rating=[4.2,4.8,5.0,3.8,4.1] plt.______________(Games,Rating) #Statement 2, plt.xlabel("Games") plt.______________("Rating") #Statement 3, plt._______________ #Statement 4, , i. Choose the right code from the following for statement 1., i. matplotlib as plt, ii. pyplot as plt, iii. matplotlib.pyplot as plt, iv. matplotlib.plt as pyplot, ANS:- (iii) matplotlib.pyplot as plt, , ii. Identify the name of the function that should be used in statement 2 to plot the above graph., , i. line(), ii. bar(), iii. hist(), iv.barh(), , ANS:- (ii) bar(), 43 | P a g e
Page 44 :
iii. Choose the correct option for the statement 3., i., , ii., iii., iv., , title("Rating"), ytitle("Rating"), ylabel("Rating"), yaxis("Rating"), , ANS:- (iii) ylabel("Rating”), , iv) Choose the right function/method from the following for the statement 4., i., ii., iii., iv., , display(), print(), bar(), show(), Answer: (iv) show(), , v) In case Mr. Javed wants to change the above plot to the any other shape, which statement, should he, change., i., ii., iii., iv., , Statement 1, Statement 2, Statement 3, Statement 4, Answer: Statement 2, , Q-7 Khushi is the event incharge in a school. One of her students gave her a suggestion to use Python, Pandas and Matplotlib for analysing and visualising the data, respectively. She has created a Data frame, “SportsDay” to keep track of the number of First, Second and Third prizes won by different houses in, various events., , Write Python commands to do the following:, , 44 | P a g e
Page 45 :
i. Display the house names where the number of Second Prizes are in the range of 12 to 20., a. df['Name'][(df['Second']>=12) and (df['Second']<=20)], b. df[Name][(df['Second']>=12) & (df['Second']<=20)], c. df['Name'][(df['Second']>=12) & (df['Second']<=20)], d. df[(df['Second']>=12) & (df['Second']<=20)], ANS: c. df['Name'][(df['Second']>=12) & (df['Second']<=20)], , ii. Display all the records in the reverse order., a. print(df[::1]), b. print(df.iloc[::-1]), c. print(df[-1:]+df[:-1]), d. print(df.reverse()), , ANS: b. print(df.iloc[::-1]), , iii. Display the bottom 3 records., a. df.last(3), b. df.bottom(3), c. df.next(3), d. df.tail(3), , ANS: d. df.tail(3), , iv) Choose the correct output for the given statements:, x=df.columns[:1], print(x), 45 | P a g e
Page 46 :
a. 0, b. Name, c. First, d. Error, , ANS:- b. Name, , v. Which command will give the output 24:, , a. print(df.size), b. print(df.shape), c. print(df.index), d. print(df.axes), ANS:- a. df.size, , 46 | P a g e
Page 47 :
SOCIETAL IMPACTS, SECTION A- MULTIPLE CHOICE QUESTIONS, Q1. _______________ are the records and traces that we left behind as we use Internet., a. Digital Footprints, b. Data Protection, c. Plagiarism, d. Digital Data, , Q2. Digital footprints are stored _______, a. Temporarily (for few days), b. Permanently, c. for 7 days only, d. for 3 days, , Q3. Whenever we surf the Internet using smartphones we leave a trail of data reflecting the activities, performed by us online, which is our ___________, a. Digital footprint, b. Digital activities, c. Online handprint, d. Internet activities, , Q4. There are _________ kinds of Digital footprints., a. 1, b. 2, c. 3, d. 4, , Q5. Which of the following is type of Digital Footprints?, a. Active digital footprints, b. Passive digital footprints, c. Both of the above, d. None of the above, 47 | P a g e
Page 48 :
Q6. The digital data trail we leave online unintentionally is called _____, a. Active digital footprints, b. Passive digital footprints, c. Current digital footprints, d. None of the above, , Q7. The digital data trail we leave online intentionally is called _____, a. Active digital footprints, b. Passive digital footprints, c. Current digital footprints, d. None of the above, , Q8. Which of the following activity is an example of leaving Active digital footprints?, a. Surfing internet, b. Visiting a website, c. Sending an email to friend, d. None of the above, , Q9. Our digital footprint can be created by _______, a. visiting any website, b. sending email, c. posting online, d. All of the above, , Q10. Our digital footprints are stored in local web browser in the form of ________, a. browsing history, b. cookies, c. passwords, d. All of the above, , 48 | P a g e
Page 49 :
Q11. Our digital foot prints are stored in ________, a. Local web browser, b. Servers where the applications are hosted, c. Both of the above, d. None of the above, , Q12. Digital footprints can be used to ________, a. Trace the user’s location, b. Trace the user’s digital activity, c. know the digital personality of user., d. All of the above, , Q13. Anyone who uses digital technology along with Internet is a ____, a. Digital citizen, b. Netizen, c. Both of the above, d. None of the above, , Q14. In this era of digital society, we can do ______________, a. Online Shopping, b. Online Banking, c. Online Education, d. All of the above, , Q15. Which of the following are Net Etiquette?, a. Be Ethical, b. Be Respectful, c. Be Responsible, d. All of the above, , 49 | P a g e
Page 50 :
Q16. Being a responsible digital citizen, we should ______, a. not use copyrighted materials, b. avoid cyber bullying, c. respect privacy of others, d. All of the above, , Q17. Online posting of rumours, giving threats online, posting the victim’s personal information, comments, aimed to publicly ridicule a victim is termed as __________, a. Cyber bullying, b. Cyber crime, c. Cyber insult, d. All of the above, , Q18. _______ is a person who deliberately sows discord on the Internet by starting quarrels or upsetting, people, by posting inflammatory or off topic messages in an online community., a. Netizen, b. Digital Citizen, c. Internet troll, d. None of the above, , Q19. Digital communication includes ________, a. Email, b. Texting, c. Instant messaging, d. All of the above, , Q20. Which of the following is example of Social media?, a. Facebook, b. Twitter, c. Instagram, d. All of the above, , 50 | P a g e
Page 51 :
Q21. Which of the following is not an example of Social media platform?, a. Facebook, b. Pinterest, c. Google+, d. Social channel, , Q22. ________ are websites or applications that enable users to participate by creating and sharing content, with others in the community., a. Social media, b. Social channel, c. Social networking, d. None of the above, , Q23. A responsible netizen must abide by ____________, a. net etiquettes, b. communication etiquettes, c. social media etiquettes, d. All of the above, , Q24. In social media platform, we can share _____________, a. images, b. text, c. videos, d. All of the above, , Q25. To be a responsible netizen, we should ___________, a. Choose password wisely, b. think before upload anything online., c. change our password frequently., d. All of the above, , 51 | P a g e
Page 52 :
Q26. Data that can cause substantial harm, embarrassment, inconvenience and unfairness to an individual, if, breached or compromised, is called _______________, a. Sensitive data, b. Important data, c. security data, d. None of the above, , Q27. Example of sensitive data is ___________, a. Name of a person, b. Credit card detail of a person, c. Date of birth of a person, d. None of the above, , Q28. IPR stands for ______________, a. Indian Property Right, b. Intellectual Property Right, c. Intelligent Property Right, d. Intellectual Property Resource, , Q29. Code of the software will be protected by _____________, a. copyright, b. patent, c. registered trademark, d. None of the above, , Q30. Functional expression of the idea/invention will be protected by ________, a. copyright, b. patent, c. registered trademark, d. None of the above, , 52 | P a g e
Page 53 :
Q31. The name and logo of the software will be protected by ___________, a. copyright, b. patent, c. registered trademark, d. None of the above, , Q32. Intellectual Property is legally protected through ____, a. copyright, b. patent, c. registered trademark, d. All of the above, , Q33. The ____________ include right to copy (reproduce) a work, right to distribute copies of the work to, the public, and right to publicly display or perform the work., a. Copyright, b. Patent, c. Createright, d. None of the above, , Q34. A ______________ provide an exclusive right to prevent others from using, selling, or distributing the, protected invention, a. copyright, b. trademark, c. patent, d. All of the above, , Q35. A patent protects an invention for ___________ years, after which it can be freely used., a. 10, b. 20, c. 30, d. 40, 53 | P a g e
Page 54 :
Q36. _____________ includes any visual symbol, word, name, design, slogan, label, etc., that distinguishes, the brand from other brands., a. Trademark, b. Patent, c. Copyright, d. None of the above, , Q37. EULA stands for _____________, a. End User Leave Agreement, b. End User License Aim, c. End User License Agreement, d. None of the above, , Q38. _________________covers all clauses of software purchase, viz., how many copies can be installed,, whether source is available, whether it can be modified and redistributed and so on., a. EULA, b. EULE, c. AULA, d. AULI, , Q39. ___________ means using other’s work and not giving adequate citation for use., a. Plagiarism, b. Licensing, c. Copyright, d. None of the above, , Q40. Licensing and copyrights are same terms.(T/F), a. True, b. False, , 54 | P a g e
Page 55 :
Q41. A ____________ is a type of contract between the creator of an original work permitting someone to, use their work, generally for some price., a. Agreement, b. License, c. Patent, d. Copyright, , Q42. Presenting someone else’s idea or work as one’s own idea or work is called ________, a. Plagiarism, b. Copyright infringement, c. Patent infringement, d. None of the above, , Q43. Ravi copy some contents from Internet, but do not mention the source or the original creator. This is an, act of ______, a. Plagiarism, b. Copyright Infringement, c. Trademark Infringement, d. Licence Infringement, , Q44. _____________ means unauthorized use of other’s trademark on products and services., a. Copyright Infringement, b. Trademark Infringement, c. Plagiarism, d. Patent, , Q45. GPL stands for ___________, a. General Public License, b. GNU General Private License, c. GNU General Public License, d. GNU Public License, , 55 | P a g e
Page 56 :
Q46. Which of the following is popular category of public licenses?, a. GPL, b. CC, c. Both of the above, d. None of the above, , Q47. CC (in reference to public license) stands for _____, a. Creative Commons, b. Carbon copy, c. Creative Comments, d. Creative Culture, , Q48. GPL is primarily designed for providing public license to a ______, a. software, b. websites, c. literature, d. music, , Q49. FOSS stands for __________, a. For open source software, b. Free and open set software, c. Free and open source software, d. None of the above, , Q50. ____________ operating system come under FOSS., a. Ubuntu, b. Unix, c. Mac, d. Windows, , 56 | P a g e
Page 57 :
Q51. ____________ browser come under FOSS., a. Internet explorer, b. Chrome, c. Mozilla Firefox, d. None of the above, , Q52. _____________ is the unauthorized use or distribution of software., a. Software piracy, b. Piracy, c. Software copy, d. Pirated Software, , Q53. ___________ package come under FOSS., a. Libre Office, b. Open Office, c. Both of the above, d. None of the above, , Q54. The owner of a work can create _______ different types of CC licenses., a. 2, b. 4, c. 6, d. 8, , Q55. _______ is defined as a crime in which computer is the medium of crime., a. Computer crime, b. Cyber crime, c. Internet crime, d. Digital crime, , 57 | P a g e
Page 58 :
Q56. Which of the following is cybercrime?, a. Hacking, b. Phishing, c. Spamming, d. All of the above, , Q57. A ___________ is some lines of malicious code that can copy itself and can have detrimental effect on, the computers, by destroying data or corrupting the system., a. Cyber crime, b. Computer virus, c. Program, d. Software, , Q58. ____________ is the act of unauthorized access to a computer, computer network or any digital, system., a. Sign in, b. Hacking, c. Tracking, d. None of the above, , Q59. Hacking, when done with a positive intent, is called ______, a. Ethical hacking, b. Active hacking, c. Passive hacking, d. Ethics, , Q60. Which of the following is called black hat hacker?, a. Ethical hacker, b. Non Ethical hacker, c. Both of the above, d. None of the above, , 58 | P a g e
Page 59 :
Q61. Which of the following is white hat hacker?, a. Ethical hacker, b. Non Ethical hacker, c. Both of the above, d. None of the above, , Q62. Primary focus of ________ is on security cracking and data stealing., a. ethical hacker, b. non ethical hacker, c. white hat hacker, d. None of the above, , Q63. Hackers try to break security system ___________, a. for Identity theft, b. for monetary gain, c. to leak sensitive information, d. All of the above, , Q64. ______________ is an activity where fake websites or emails that look original or authentic are, presented to the user., a. Phishing, b. Hacking, c. Spamming, d. Identity theft, , Q65. ________ is a kind of cyber crime in which attacker blackmails the victim to pay for getting access to, the data., a. Phishing, b. Identity theft, c. Ransomware, d. None of the above, , 59 | P a g e
Page 60 :
Q66. Which of the following can be considered as safety measures to reduce the risk of cyber crime?, a. Use an antivirus software and keep it updated always., b. Avoid installing pirated software., c. Use strong password for web login, and change it periodically., d. All of the above, , Q67. E-waste stands for ______, a. Electrical waste, b. Electronic waste, c. Electricity waste, d. E-waste, , Q68. Which of the following constitute e-waste?, a. discarded computers, b. damaged printers, c. useless CDs, d. All of the above, , Q69. Which of the following are feasible methods of e-waste management?, a. Reduce, b. Reuse, c. Recycle, d. All of the above, , Q70. The process of re-selling old electronic goods at lower prices is called ____, a. refurbishing, b. recycle, c. reuse, d. reduce, , 60 | P a g e
Page 61 :
Q71. ____________ is a branch of science that deals with designing or arranging workplaces including the, furniture, equipment and systems so that it becomes safe and comfortable for the user., a. Ergonomics, b. Ergomics, c. Agonomics, d. All of the above, , Q72. Bad posture of using computer may cause _____, a. Backache, b. Neck Pain, c. Shoulder pain, d. All of the above, , Q73. What we have to ensures to maintain good health of a computer system?, a. Wipe monitor’s screen often using the regular microfiber soft cloth., b. Keep it away from direct heat, sunlight and put it in a room with enough ventilation for air circulation., c. Do not eat food or drink over the keyboard, d. All of the above, , Q74. Proprietary software is a software which is available _________, a. free of charge, b. on paying license fee, c. free for first year only, d. none of the above, , Q75. Which of the following is not a cyber crime?, a. Phishing, b. Ransomware, c. Hacking, d. Tracking, , 61 | P a g e
Page 62 :
ANSWERS, 1. a, , 2.b, , 3.a, , 4.b, , 5.c, , 6.b, , 7.a, , 8.c, , 9.d, , 10.d, , 11.c, , 12.d, , 13.c, , 14.d, , 15.d, , 16.d, , 17.a, , 18.c, , 19.d, , 20.d, , 21.d, , 22.a, , 23.d, , 24.d, , 25.d, , 26.a, , 27.b, , 28.b, , 29.a, , 30.b, , 31.c, , 32.d, , 33.a, , 34.a, , 35.b, , 36.a, , 37.c, , 38.a, , 39.a, , 40.b, , 41.b, , 42.a, , 43.a, , 44.b, , 45.a, , 46.c, , 47.a, , 48.a, , 49.c, , 50.a, , 51.c, , 52.a, , 53.c, , 54.c, , 55.b, , 56.d, , 57.b, , 58.b, , 59.a, , 60.b, , 61.a, , 62.b, , 63.d, , 64.a, , 65.c, , 66.d, , 67.b, , 68.d, , 69.d, , 70.a, , 71.a, , 72.d, , 73.d, , 74.b, , 75.d, , 62 | P a g e
Page 63 :
SECTION B- ADDITIONAL QUESTIONS, , Q.1. Gaining unauthorised access to a network or computer aur digital files with malicious intentions, is, called_________, a., b., c., d., , Cracking, Hacking, Banging, Phishing, , Q.2. Legal term to describe the rights of a creator of original creative or artistic work is called _____, a., b., c., d., , Copyright, Copyleft, GPL, None of these, , Q.3. OSS stands for, a., b., c., d., , Open system security, Open system source, Open software and security, Open source software, , Q.4.Any fraudulent business practice that extracts money e from an unsuspecting, ignorant person is, called_______, a., b., c., d., , Stealing, Scam, Violation of copyright, Digital footprint, , Q.5.________ means no price is to be paid for the software., a., b., c., d., , Free software, Freeware, shareware, Open source software, , Q.6.Any work / information that exist in digital form idea on internet or on an electronic device, is known, as________________ property., a., b., c., d., , Licence property, digital property, source code property, software property, , Q.7.Discarded electrical or or electronic devices are known as____________., a., b., c., d., , E waste, Software Waste, Hardware waste, Computer waste, , 63 | P a g e
Page 64 :
Q.8.The least restrictive open sourcelicence is________ licence., a., b., c., d., , Apache Licence, MIT licence, GNU licence, BSD licence, , Q.9. The original code written by programmers for a software is known as______________, a., b., c., d., , Object code, Source code, Python code, Language code, , Q.10. ____________ means freedom to use the software., a., b., c., d., , Plagiarism, Freeware, Open software, Free software, , Q.11. IAD means _________________, a., b., c., d., , Internet advanced data, Internet addiction disorder, Internet advanced digitalization, Internet aggregate data, , Q.12. The__________ is the Digital trail of your activity on the internet., a., b., c., d., , Copyleft, Digital footprint, Digital data, Internet property, , Q.13.The ________ the are the permissions given to use a product or someone's creator by the, copyright holder., a., b., c., d., , Source code, Licence, Software authority, Digital rights, , Q.14._____________ is a licence that gives right opposite to copyright., a., b., c., d., , Left copy, Digital copy, Copyleft, IPR, , Q.15. A software that can be freely accessed and modified is called, a., b., c., d., , synchronous software, package software, open source software, middleware., , 64 | P a g e
Page 65 :
Q.16.Which of the following is an advantage of open source software?, a., b., c., d., , You can edit the source code to customise it, you need to be an expert to edit code, you have to pay, can sometimes with two generic for specialist purposes., , Q.17.Which of the following is a disadvantage of open source software?, a., b., c., d., , high quality software with lots of features., not as customizable, may not have been tested as much as proprietary software so might have bugs., you can added the source code to customize it, , Q.18.Which of the following is an advantage of proprietary software?, a., b., c., d., , It is usually free, thoroughly tested because people are paying to use it., Not as customizable., Can sometimes be to generate for specialist purposes., , Q.19.Which of the following is a disadvantage of proprietary software?, a., b., c., d., , You need to be an expert to edit code., You have to pay for this type of software., It’s licensed., It is launched after proper testing., , Q.20.The generally recognized term for the government protection afforded to intellectual property written, and electronic is called _____________, a., b., c., d., , Computer security law., Aggregate information., Copyright law, Data security standards., , Q.21.Which of the following would be a creative work protected by copyright?, a., b., c., d., , A list of all Indian President names, A Portrait of your family, A song you wrote, The name of your pet dog, , Q.22.Which of the following is not done by cyber criminals?, a., b., c., d., , Unauthorised account access, Mass Attack using trojans as botnets, Email spoofing and spamming, report vulnerabilty in any system, , Q.23.What is the name of the IT law that India is having in the Indian legislature?, a., b., c., d., , India's Technology IT Act 2000, India's Digital information technology DIT Act, 2000, India's Information Technology IT Act, 2000, The technology act, 2008., , 65 | P a g e
Page 66 :
Q.24.What is meant by the term cybercrime?, a., b., c., d., , Any crime that uses computers to jeopardize or attempt to jeoparadise in national security, The use of computer networks to commit financial or identity fraud, The theft of Digital information, Any crime that involves computers and networks, , Q.25.Every activity you perform on the internet is safe for how long?, a., b., c., d., , 1 month, 1 year, As per my setting, Forever, , Q.26.A _____________ is an injury or disorder of muscles, nerves, tendons, ligaments and joints., a., b., c., d., e., , Repetitive Strain injury, Muscle injury, Nervous breakdown, Joint pain, , Q.27.________________ is a technology related health condition affecting eyesight., a., b., c., d., , Computer vision strain, Computer vision syndrome, Eyesight syndrome, Vision imbalance, , ANSWERS, 1.b, , 2.a, , 3.d, , 4.b, , 5.b, , 6.b, , 7.a, , 8.b, , 9.b, , 10.d, , 11.b, , 12.b, , 13.b, , 14.c, , 15.c, , 16.a, , 17.c, , 18.b, , 19.b, , 20.c, , 21.c, , 22.d, , 23.c, , 24.d, , 25.d, , 26.a, , 27.b, , 66 | P a g e
Page 67 :
SECTION C- CASE STUDY BASED QUESTIONS, , 1. After practicals, Atharv left the computer laboratory but forgot to sign off from his email account. Later,, his classmate Revaan started using the same computer. He is now logged in as Atharv. He sends inflammatory, email messages to few of his classmates using Atharv’s email account. Revaan’s activity is an example of, which of the following cyber crime?, a) Hacking, b) Identity theft, c) Cyber bullying, d) Plagiarism, , 2. Rishika found a crumpled paper under her desk. She picked it up and opened it. It contained some text, which was struck off thrice. But she could still figure out easily that the struck off text was the email ID and, password of Garvit, her classmate. What is ethically correct for Rishika to do?, a) Inform Garvit so that he may change his password., b) Give the password of Garvit’s email ID to all other classmates., c) Use Garvit’s password to access his account., , 3. Suhana is down with fever. So, she decided not to go to school tomorrow. Next day, in the evening she, called up her classmate, Shaurya and enquired about the computer class. She also requested him to explain, the concept. Shaurya said, “Mam taught us how to use tuples in python”. Further, he generously said, “Give, me some time, I will email you the material which will help you to understand tuples in python”. Shaurya, quickly downloaded a 2-minute clip from the Internet explaining the concept of tuples in python. Using video, editor, he added the text “Prepared by Shaurya” in the downloaded video clip. Then, he emailed the modified, video clip to Suhana. This act of Shaurya is an example of —, a) Fair use, b) Hacking, c) Copyright infringement, d) Cyber crime, , 4. After a fight with your friend, you did the following activities. Which of these activities is not an example, of cyber bullying?, a) You sent an email to your friend with a message saying that “I am sorry”., b) You sent a threatening message to your friend saying “Do not try to call or talk to me”., c) You created an embarrassing picture of your friend and uploaded on your account on a social networking, site., , 67 | P a g e
Page 68 :
5. Sourabh has to prepare a project on “Digital India Initiatives”. He decides to get information from the, Internet. He downloads three web pages (webpage 1, webpage 2,webpage 3) containing information on Digital, India Initiatives. Which of the following steps taken by Sourabh is an example of plagiarism or copyright, infringement?, , a) He read a paragraph on “Digital India Initiatives” from webpage 1 and rephrased it in his own, words. He finally pasted the rephrased paragraph in his project., b) He downloaded three images of “Digital India Initiatives” from webpage 2. He made a collage for his, project using these images., c) He downloaded “Digital India Initiative” icon from web page 3 and pasted it on the front page of his project, report., , 6. Neerja is a student of Class XI. She has opted for Computer Science. Neerja prepared the project assigned, to her. She mailed it to her teacher. The snapshot of that email is shown below., , Find out which of the following email etiquettes are missing in it., , a) Subject of the mail, b) Formal greeting, c) Self-explanatory terms, d) Identity of the sender, e) Regards, , ANSWERS, 1. b, , 2. a, , 68 | P a g e, , 3. c, , 4. a, , 5. b, , 6. A
Page 69 :
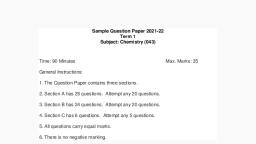
Sample Question Paper SET - 1 (Term-1), 2021, Informatics Practices (065), Class 12, Time: 02:00 Hrs, , Marks: 35, , Instructions:, 1., 2., 3., 4., , Do not open the question booklet until you are asked to do so., There are 35 questions in the question booklet., Each question is compulsory., Each question has four possible answers - A, B, C and D. Students are required to, choose the most appropriate answer out of the four alternatives., , 69 | P a g e
Page 70 :
QNo., 1, , 2, , 3, , 4, , 5, , 6, , 7, , Question, , Marks, , Data which has no restriction of usage and is freely available to everyone, under Intellectual Property Rights is categorised as:, (a) Open source, , (b) Open data, , (c) Open content, , (d) Open education, , Which of the following is not a valid line style in matplotlib?, (a) ‘-’, , (b) ‘--’, , (c) ‘-.’, , (d) ‘<’, , The best type of graph to represent distribution of elements is, (a) bar, , (b) histogram, , (c) pie, , (d) basemap, , Which of the following pandas attributes gives output in the form of tuple?, (a) nbytes, , (b) ndim, , (c) shape, , (d) size, , A student copies his final year project from a random internet source. This, act is termed as, (a) Phishing, , (b) Spamming, , (c) Plagiarism, , (d) Identity Theft, , A series contains a total of 10 elements including a missing value. The, output of count and len functions when applied to this Series respectively, will be, (a) 10,10, , (b) 9,10, , (c) 9,9, , (d) 10,9, , Which of the following parameters of the read_csv function is used to make, one of the columns of the data in the csv file as index of the data frame., , 70 | P a g e, , (a) skiprows, , (b) index_row, , (c) nrows, , (c) index_col, , 1, , 1, , 1, , 1, , 1, , 1, , 1
Page 71 :
8, , 9, , 10, , A mail or message sent to a large number of people without their consent is, called, , (a) Cyberstalking, , (b) Eavesdropping, , (c) Phishing, , (d) Spamming, , A trademark is valid for ____ years and can be renewed after that., , (a) 6, , (b) 10, , (c) 5, , (d) 4, , Which of the following is not the correct method of E-waste management?, , (a) Regrow, , (b) Reduce, , (c) Recycle, , (d) Reuse, , 1, , 1, , 1, , Directions (Q No. 11-15) In the questions given below there are two, statements marked as Assertion (A) and Reason (R) . Read the statements, and choose the correct option., a. Both (A) and (R) are True, and (R) is the correct explanation of (A)., b. Both (A) and (R) are True, but (R) is not the correct explanation of, (A)., c. (A) is true, but (R) is false., d. (A) is false, but (R) is true., 11, , Assertion (A): To display the first four elements of a Series object, you may, write S[:4]., Reason (R): To display the first five rows of a Series object S, you may use, tail() function., , 1, , 12, , Assertion (A): The rename function of Data Frame does not rename the, columns of the original data frame, but instead returns a dataframe with, updated column names., Reason (R): Default value of inplace parameter in rename function is False., , 1, , 13, , Assertion (A): A series object is size mutable., Reason (R): A data frame is value mutable., , 1, , 14, , Assertion (A): loc is used to extract a subset of a data frame., Reason (R): Transpose of a dataframe df can be obtained using df.T., , 1, , 15, , Assertion (A): Given a Series S, output of print(len(S.shape) will be 1., Reason (R): A series is one dimensional in nature., , 1, , Directions (Q No. 16-20) Read the extract given below and answer the, questions on the basis of the same., , 71 | P a g e
Page 73 :
20, , He wants to obtain the sum of marks for each student as given below., Choose the correct statement to obtain the same., , (a) print(df.sum(axis=0)), (b) print(df.sum()), (c) print(df.sum(0)), (d) print(df.sum(1)), Directions (Q No. 21-25) Read the extract given below and answer the, questions on the basis of the same., Ms. Ankita wants to plot the below given graph of y=x*2 vs y=x*3 for x in the, range 1 to 10. However, she is facing some problems. Help her by answering, a few questions related to the code written by her., , Code:, , 73 | P a g e, , 1
Page 74 :
21, , 22, , 23, , 24, , 25, , 26, , 27, , What color code should be used to assign black color to the plot of y=x*2 in, the line marked as statement 1?, (a) bl, , (b) c, , (c) bk, , (d) k, , What x axis should be chosen for y=x*3 plot in statement 2 so that the bars, do not overlap., (a) x, , (b) 0.4, , (c) x+0.4, , (d) x*0.4, , Fill in the blank in statement 3 to print all the points on the x axis., (a) xticks, , (b) xtick, , (c) xlabel, , (d) xlabels, , Fill in the blank in statement 4 to display the legends as shown in the plot., (a) legends, , (b) displaylegends, , (c) displaylegend, , (d) legend, , Fill in the blank in statement 5 to display the plot., (a) plt.display(), , (b) plt.show(), , (c) plt.showplot(), , (d) plt.displayplot(), , A Data Frame is having True and False as its boolean indexes. The, command that can be used to access all the rows corresponding to True, boolean index is, (a) print(df.loc(True), , (b) print(df.loc[:,True]), , (c) print(df.loc[True]), , (d) print(df.loc(True,:), , Consider the following Data Frame df containing missing values, , The command df.dropna(how='all') will, (a) return Data Frame containing row(s) I3., (b) return Data Frame containing row(s) I1 and I2., (c) return Data Frame containing row(s) I1., (d) return Data Frame containing row(s) I2., , 74 | P a g e, , 1, , 1, , 1, , 1, , 1, , 1, , 1
Page 75 :
28, , Consider a Data Frame containing three columns C1, C2 and C3, which of, the below given commands can be used to delete the column C3?, (a) del, (b) del, (c) del, (d) del, , 29, , 1, , df.C3, df.loc[:,'C3'], df.iloc[:,2], df['C3'], , Consider a Data Frame containing three rows R1, R2 and R3, which of the, below given commands to delete the rows R1 and R2 is incorrect?, , 1, , (a) df=df.drop(['R1','R2'],1), (b) df=df.drop(['R1','R2']), (c) df=df.drop(['R1','R2'],0), (d) df=df.drop(['R1','R2'],axis='index'), 30, , Consider the below given Data Frame df, , 1, , The output of the following command will be, print(df[df.C2>10].max()['C1']), (a) 22, (b) 10, (c) 12, (d) 11, Directions (Q No. 31-35) In the questions given below there are two, statements marked as Assertion (A) and Reason (R) . Read the statements, and choose the correct option., a. Both (A) and (R) are True, and (R) is the correct explanation of (A)., b. Both (A) and (R) are True, but (R) is not the correct explanation of, (A)., c. (A) is true, but (R) is false., d. (A) is false, but (R) is true., 31, , Assertion (A): The electronic records available on DigiLocker are, considered legitimate., Reason (R): The electronic records available on DigiLocker or mParivahan, are deemed to be legally recognised at par with the original documents as, per the provisions of the Information Technology Act, 2000, , 1, , 32, , Assertion (A): Someone has created a fake social media profile in the name, of Saket. Saket is a victim of cyberstalking., Reason (R): Cyberstalking is a form of cybercrime., , 1, , 33, , Assertion (A): Stealing money from someone’s wallet is a type of, cybercrime., Reason (R): Cybercrime is a crime that involves a computer and a network., , 1, , 34, , Assertion (A): Amit has stolen the content of a research paper and, published it online. Amit has performed cybercrime., Reason (R): Plagiarism is the act of stealing someone’s work and presenting, it as one’s own work., , 1, , 75 | P a g e
Page 76 :
35, , Assertion (A): The source code of weka software can be modified and, shared as it’s an open source data mining software., Reason (R): Open-source software is computer software that is released, under a license in which the copyright holder grants users the rights to use,, study, change, and distribute the software and its source code, , 1, , MARKING SCHEME – SET 1 ( Term -1), , 1, , b, , 2, , d, , 3, , b, , 4, , c, , 5, , c, , 6, , b, , 7, , c, , 8, , d, , 9, , b, , 10, , a, , 11, , c, , 12, , a, , 13, , d, , 14, , b, , 15, , a, , 16, , c, , 17, , b, , 18, , b, , 19, , a, , 20, , d, , 21, , d, , 22, , c, , 23, , a, , 24, , d, , 25, , b, , 26, , c, , 27, , b, , 28, , d, , 29, , a, , 30, , c, , 31, , a, , 32, , b, , 33, , d, , 34, , d, , 35, , a, , 76 | P a g e
Page 77 :
Sample Question Paper Set 2 (Term 1), , Session 2021-22, Subject: Informatics Practices (065), Class XII, Max Time: 02:00 Hours, , 1., , Max Marks: 35, , Smridh has recently changed his school so he is not aware of the people, but someone is posting negative, demeaning comments on his social media profile. He is also getting repeated mails from unknown, people.Everytime he goes online, he finds someone chasing him online. (5), i. Smridh is a victim of ............. :, a. Eavesdropping, b. Stolen identity, c. Phishing, d. Cyber stalking, ii. The action that Smridh should take :, a. He should ONLY share with his friends, b. He should NOT share with anyone as it can cause serious problem, c. He should immediately report to the police, d. He should bring to the notice of his parents and school authorities., iii. .......................... is a set of moral principles that governs the behaviour of a group or individual, andregulates the use of computers., a. Copyright, b. Computer ethics, c. Property rights, d. Privacy law, iv. Smridh needs to protect his personal information or data from unintentional and intentional attacks, anddisclosure which is termed as ............, a. Digital right, b. Copyright, c. Privacy, d. Intellectual property, v. The act of fraudulently acquiring someone’s personal and private information, such as online, accountnames, login information and passwords is called as ..............., a. Phishing, b. Fraud, c. Scam, d. Plagiarism, , 1. Which of the following is NOT an intellectual property?, a. A poem written by a poet, b. An original painting made by a painter, c. Trademark of a Company, d. A remixed song, 77 | P a g e, , 1
Page 78 :
2. An act of stealing others Intellectual Property without their consent of without citing the, source is called., a. Plagiarism, b. Hacking, c. Phishing, d. Bullying, 3. Name the cyber law enforced in India to provide legal recognition to electronic commerce and to facilitate, filing of electronic records with the Government ______1, a. IT(Information Technology) Act 2000, b. DIT(Digital Information technology) Act 2000, c. IIT (Indian Information Technology) Act 2000, d. EnC (Electronic and Commerce) Act 2000, 4. A software that can be freely accessed and modified is called:, a., b., c., d., , 1, , Synchronous software, Package software, Open source software, Middleware, , 5. Data which has no restriction on usage and is freely available to everyone under intellectual property, rights is categorized as:, 1, e., f., g., h., , Open source, Open data, Open content, Open education, , 6. To change the width of bars in bar chart, which of the following argument with a float value is used?, 1, a. thick, b. thickness, c. width, d. barwidth, 7. Which of the following is/are correct statement for plot method?, a. pl.plot(x,y,color,others), b. pl.plot(x,y), c. pl.plot(x,y,color), d. all of these, , 1, , 8. To give a title to x-axis, which of the following method is useful?, a. pl.xtitle(“title”), b. pl.xlabel(“title”), c. pl.xheader(“title”), d. pl.xlabel.show(“title”), , 1, , 78 | P a g e
Page 79 :
9. Which of the following correct statement to import pyplot module?, a. import matplotlib.pyplot, b. import MatPlotLib.PyPlot, c. import PyPlot as pl, d. import pyplot.plot, 5. Consider the following program and answer the questions from a to e, , import matplotlib.pyplot as pl, a., b., c., d., , l1=[1,4,6,8], l2=[2,8,9,10], l3=[1,5,7,9], l4=[5,2,6,1], , ________________________#Line 1, pl.plot(l3,l4,label="Australia"), pl.legend(loc="upper left"), ________________________#Line 2, pl.ylabel("Goals"), ________________________#Line 3, ________________________#Line 4, ________________________# Line 5, a. What will be the line to be written in #Line 1 to plot a line chart:, i., pl.plt(l1,l2,label="India"), ii., pl.show(l1,l2,label="India"), iii., pl.plot(l1,l2,label="India"), iv., pl.line(l1,l2,label="India"), b. What will be the line to be written in #Line 2 to set label on x axis:, i., pl.xlabels("Time"), ii., pl.labelx("Time"), iii., pl.xlabel("Time"), iv., pl.xaxislabel("Time"), c. What will be the line to be written in #Line 3 to set title of the chart:, i., pl.titles("Chart of Score in game"), ii., pl.settitle("Chart of Score in game"), iii., chart.title("Chart of Score in game"), iv., pl.title("Chart of Score in game"), d. What will be the line to be written in #Line 4 to show the chart made:, i., pl.showchart(), ii., pl.chartshow(), iii., pl.show(), iv., pl.fullchartshow(), e. What will be the line to be written in #Line 5 to save the chart made:, i., pl.savefigure("abc.jpg"), ii., pl.savechart("abc.jpg"), iii., pl.chartsavefig("abc.jpg"), iv., pl.savefig("abc.jpg"), , 79 | P a g e, , 1, , 5
Page 80 :
6. Consider the following Python code and write the output for statement., , 1, , import pandas as pd, values=[“India”, “Canada”], code=[“IND”, “CAN”], df=pd.DataFrame(values,Index=Code,columns=[‘Country’]), a. Code Country, IND India, CAN Canada, b. Code Country, CAN Canada, IND India, c. Code, IND India, CAN Canada, d. Code Country, CAN Canada, , 7. The teacher needs to know the marks scored by the student with roll number 4. Help her toidentify the, , correct set of statement/s from the given options :, , 1, , a. df1=df[df[‘rollno’]==4], print(df1), b. df1=df[rollno==4], print(df1), c. df1=df[df.rollno=4], print(df1), d. df1=df[df.rollno==4], print(df1), , 15. In Pandas the function used to delete a column in a DataFrame is, , 1, , a. remove, b. del, c. drop, d. cancel, , 16. function applies the passed function on each individual data element of thedataframe., 1, a. apply() b. applymap() c. pivot() d. pivot_table(), , 80 | P a g e
Page 81 :
17. Which of the following statement/s will give the exact number of values ineach column of the, dataframe?, 1, i. print(df.count()), ii. print(df.count(0)), iii. print(df.count), iv. print(df.count(axis=’index’)), Choose the correct option:, a. both (i) and (ii), b. only (ii), c. (i), (ii) and (iii), d. (i), (ii) and (iv), , 18. Which of the following command will display the column labels of the DataFrame? 1, a. print(df.columns()) b. print(df.column()) c. print(df.column) d. print(df.columns), , 19. Which method is used to access vertical subset of a dataframe.?, , 1, , (i) iterrows(), (ii) iteritems(), (iii) itertuples(), (iv) itercols(), , 20. To iterate over horizontal subset of dataframe, _____ function may be used:, a. iterate(), b. iterrows(), c. itercols(), d. iteritems(), , 1, , 21. To iterate over vertical subset of dataset of a dataframe, ________ function may be used:, 1, a. iterate(), b. iterrows(), c. itercols(), d. iteritems(), 22. The technique that divides total distribution of data into a given number of equal portion is called a:, 1, a. Quartile, b. Tercile, c. Median, d. Quantile, 23. To divide total distribution of data into four equal parts, _______ function is used: 1, a. Median, b. Quantile, 81 | P a g e
Page 83 :
MARKING SCHEME – SET 2 (TERM -1), 1. a. d, b. d, c. b, d. c, e. a, 2. d, 3. a, 4. a, 5. c, 6. b, 7. c, 8. d, 9. b, 10. a, 11. a. iii, b. iii, c. iv, d. iii, e. iv, 12. a, 13. a. df1=df[df[‘rollno’]==4], print(df1), d. df1=df[df.rollno==4], print(df1), 14. (b) del, 15. a. apply(), 16. a. both (i) and (ii), 17. a. print(df.columns()) or d. print(df.columns), 18. (ii) Iteritems( ), 19. b, 20. d, 21. d, 22. c, 23. (i) a. Df1[‘fee’]=([100,200,300]), (ii) c. Df1=Df1.T, (iii) b. del Df1[‘fee’], (iv) d. Df2=Df2.append(Df1), (v) a. data.iloc[1:4], , 83 | P a g e
Page 84 :
Sample Question Paper Set - 3 (Term 1), , Session 2021-22, Subject : Informatics Practices (065), Class XII, Max Time: 02:00 Hours, , Max Marks: 35, , 1. What is meant by term cyber crime:, a. Any crime that use computer to jeopardise or attempt to jeopardise national security, b. The use of computer network to commit financial or identity fraud, c. The theft of digital information, d. Any crime that involves computers and networks, , 1, , 2. Jhilmalini has stolen a credit card. She used that credit card to purchase a laptop. What type of offence has, she committed?, 1, e. Cyber Fraud, f. Identity Theft, g. Hacking, h. Stealing of Card, 3. Identify the type of cyber crime/activity from the following Situations:, , 5, , (a) A person who starts quarrels or upsets people on the internet to distract and sow discord by, posting inflammatory and digressive, extraneous or off-topic messages to an online community., This person will be referred as _____________ in cyber world., i.cyber troll, ii. cyber stalker, iii. Spyware, iv. Hacker, (b) The activity of making false accusations or statements of fact, monitoring , making threats,, identity theft ,damage to data or gathering information that may be used to harass someone by, using internet or other electronic means. This may be referred as__________., i. Cyber stalking, ii. cyber bullying, iii digital footprinting, iv. Fishing, (c)________________is the attempt to acquire sensitive information such as usernames,, passwords and credit card details by masquerading as a trustworthy entity in an electronic, communication., i. Pharming, ii. Phishing, iii. Attack, iv. Malware, (d) _______________is an attack in which a hacker attempts to redirect a website‟s traffic to, another fake or bogus website., i. Pharming, ii. Phishing, iii. Addware, iv. Malware, , 84 | P a g e
Page 85 :
(e) ______________refers to a type of malware that displays unwanted advertisement on your computer or, device., i. Pharming, ii. spyware, iii. Addware, iv. Malware, 4. Which of the following is an advantage of open source software:, , 1, , a. You can edit the source code to customize it, b. You need to be an expert to edit code, c. You have to pay, d. You sometimes can be too generic for specialist purposes, 5. Which of the following is an disadvantage of open source software:, , 1, , a. High quality software with lots of features, b. Not as customizable, c. May not have been tested as much as proprietary software, s might have bugs, d. You can edit the source code to customize it, 6. Which of the following is an advantage of proprietary software:, , 1, , a. It is usually free, b. Thoroughly tested because people are paying to use it, c. Not as customizable, d. Can sometimes be too generic for specialist purpose, 7. Which of the following are (is) not the valid plotting functions in python?, a. plot(), b. bar(), c. line(), d. pie(), , 1, , 8. Which of the following correct statement to import pyplot module?, 1. import matplotlib.pyplot, 2. import MatPlotLib.PyPlot, 3. import PyPlot as pl, 4. import pyplot.plot, , 1, , 9. Data visualization helps to, a. Understand data easily, b. Take a decisions, c. Improve the past performance, d. All of these, , 1, , 85 | P a g e
Page 86 :
10. Which method is used to display or show the legends?, a. pl.show(), b. pl.display(), c. pl.legend(), d. pl.values(), , 1, , 11. To change the width of bars in bar chart, which of the following argument with a float value is used?, 1, a. thick, b. thickness, c. width, d. barwidth, , 12. Consider the following program and answer the questions from a to e, import matplotlib.pyplot as pl, import numpy as np, l1=[2,4,6,7], l2=[5,7,9,2], l3=[2,5,9,12], l=np.array(l3), l4=[5,8,9,12], ________________________# Line 1, pl.bar(l+0.50,l4,width=0.50,label="australia"), ________________________# Line 2, ________________________# Line 3, pl.ylabel("goals"), pl.title("chart of score in game"), ________________________# Line 4, ________________________# Line 5, a. What will be the line to be written in #Line 1 to plot a bar chart:, i. pl.hbar(l1,l2,width=0.50,label="india"), ii. pl.barh(l1,l2,width=0.50,label="india"), iii. pl.bar(l1,l2,width=0.50,label="india"), iv. pl.plotbar(l1,l2,width=0.50,label="india"), f., , What will be the line to be written in #Line 2 to set legend:, i. pl.legends(loc="upper left"), ii. pl.setlegend(loc="upper left"), iii. pl.plotlegend(loc="upper left"), iv. pl.legend(loc="upper left"), , 86 | P a g e, , 5
Page 87 :
g. What will be the line to be written in #Line 3 to set label on x axis:, i., pl.xlabels("Time"), ii., pl.labelx("Time"), iii., pl.xlabel("Time"), iv., pl.xaxislabel("Time"), h. What will be the line to be written in #Line 4 to show the chart made:, i., , pl.showchart(), , ii., , pl.chartshow(), , iii., , pl.show(), , iv, , pl.fullchartshow(), , i., , What will be the line to be written in #Line 5 to save the chart made:, i. pl.savefigure("abc.jpg"), ii. pl.savechart("abc.jpg"), iii. pl.chartsavefig("abc.jpg"), iv. pl.savefig("abc.jpg"), , 13. Consider the following DataFrame emp and answer the any four questions from (i) to (v) 5, Experience, (in years), , Empno, , Name, , Dept, , Salary, , 1, , Ram Singh, , IT, , 15000, , 2.5, , 2, , Shyam Singh, , HR, , 18000, , 3, , 3, , Nidhi Gupta, , IT, , 9000, , 2, , 4, , Pooja Sharma, , EXE, , 24000, , 8, , 5, , Rohan Malik, , HR, , 20000, , 6, , (i) Write down the command that will give the following output., Empno 5, Name Rohan Malik, Dept HR, Salary 20000, Experience 6, dtype: object, a. print(emp.max), b. print(emp.max()), c. print(emp.max(axis=1)), d. print(emp.max,axis=1), , 87 | P a g e
Page 88 :
(ii) CEO needs to know the salary of the employee with empno 4. Help him to, identify the correct set of statement/s from the given options:, , a. emp1=emp[emp[‘empno’]==4], print(emp1), b. emp1=emp[emp], print(emp1), c. emp1=emp[emp.empno=4], print(emp1), d. emp1=emp[emp.empno==4], print(emp1), , (iii) Which of the following statement/s will give the exact number of values in each, column of the dataframe?, , i., print(emp.count()), ii., print(emp.count(0)), iii., print(emp.count), iv., print(emp.count(axis=’index’)), Choose the correct option:, a. both (i) and(ii), b. only(ii), c. (i), (ii) and(iii), d. (i), (ii) and(iv), (iv) Which of the following command will display the column labels of the, DataFrame?, a. print(emp.columns()), b. print(emp.column()), c. print(emp.column), d. print(emp.columns), (v) Mr. Satvik Ahuja, the CEO wants to add a new column, the rating of the, performance of employees with the values, ‘A’, ‘A’, ‘B’, ‘A’, ‘B’, to the DataFrame. Help, him choose the command to do so:, a. emp.column=[’A’,’A’,’B’,’A’,’B’], b. emp[‘Performance’]=[ ’A’,’A’,’B’,’A’,’B’], c. emp.loc[‘Performance’]= [’A’,’A’,’B’,’A’,’B’], d. Both (b) and (c) are correct, 88 | P a g e
Page 89 :
8. To calculative cumulative sum of a column of a dataframe, you may use ____ function:, , a., b., c., d., , 9. Function _______ can be used to drop missing values:, , a., b., c., d., , 1, , max(0, index(), idmax(), maxidx(), , 13. Consider the given program and answer the questions from a to e, , ___________________# Line 1, import numpy as np, data = np.array([1,2,3,4,5,6]), __________________# Line 2, __________________# Line 3, __________________# Line 4, a. Write the code to import pandas module, i., import pandas as pd, ii., importing pandas as pds, iii., import panda as pd, iv., include pandas as pd, b. Write the code to create a series from the given data:, i., ser = pd.CreateSeries(data), ii., ser = pd.Series(data), iii., ser = pd.SeriesCreate(data), iv., ser = pd.Serie(data), , 89 | P a g e, , 1, , tail(), bottom(3), bottom(3), tail(3), , 12. To get index of maximum value in a column of dataframe is:, , a., b., c., d., , 1, , concat(), merge(), join(), none of the above(), , 11. To get bottom three rows of a data frame, you may use _________ function:, , a., b., c., d., , 1, , fillna(), isNull(), delna(), dropna(), , 10. Which of the following methods of combining two data frame is a patching method:, , a., b., c., d., , 1, , sum(), sum(cumulative=True), cumsum(), None of the above, , 5
Page 90 :
c. Write the code to retrieve the first 5 element of the series:, i., print(ser[:6]), ii., print(ser[4:5]), iii., print(ser[1:5]), iv., print(ser[:5]), d. Write the code to sort the values of series:, i. ser.sort(), ii. ser.sortvalues(), iii. ser.values(), iv. ser.sort_values(), e. Write the code to rename the index of the series:, i. ser.index=['g','e','e','k','s','f'], ii. ser.setindex=['g','e','e','k','s','f'], iii. ser.renameindex=['g','e','e','k','s','f'], iv. ser.changeindex=['g','e','e','k','s','f'], , 90 | P a g e
Page 91 :
MARKING SCHEME SET – 3 (TERM -1), 1., 2., 3., , d, a, a. ii, b.ii, c.ii, d.i, e.iii, , 4., 5., 6., 7., 8., 9., 10., 11., 12., , a, c, b, c, a, a, c, c, a. iii, b.iv, c.iii, d.iii, e.iv, 13. (i) b. print(emp.max()), (ii) a. emp1=emp[emp[‘empno’]==4], print(emp1), d.emp1=emp[emp.empno==4], print(emp1), (iii) a. both (i) and (ii), (iv) d. print(emp.columns), (v) b. emp[‘Performance’]=[ ’A’,’A’,’B’,’A’,’B’], 14., 15., 16., 17., 18., 19., , C, D, C, B, C, a., b., c., d., e., , 91 | P a g e, , i, ii, iv, iv, i
Page 92 :
Term – 2, Database Query using SQL, , Glimpses, Candidate, Key, , All the attributes combinations inside a relation that can serve as primary key., , Constraint, , Rule and conditions set for data being stored in a database., , DDL, , Data Definition Language. SQL part-language that facilitates defining creation/, modification etc. of database objects such as tables, indexes, sequences etc., , DML, , Data Manipulation Language. SQL part-language that facilitates manipulation (addition/, deletion/ modification) of data residing in database object., , Equi Join, , A Join formed by equality of common field of two or more tables and where common, fields from all the tables appear in the final result., , Foreign Key, , A non key attribute whose values are derived from the primary key of some other tables., , Join, , A way to combine records coming from multiple tables having common fields., , Natural Join, , A type of equi-join where common column from the joining tables appears once only., , Primary Key A set of one or more attributes that can uniquely identify tuples within the relation., Relation, , A table having non-empty atomic values with unordered rows and columns is relation., , SQL, , Structured Query Language. A non-procedural UGL used for querying upon relational, database., , Tuple, , A row in a relation is called tuple., , View, , A virtual table that does not really exist in its own right but is instead derived from one or, more underlying base tables in called a view., , 92 | P a g e
Page 93 :
OBJECTIVE TYPE QUESTIONS, Multiple Choice Questions, 1., , A ____ is a property of the entire relation, which ensures through its value that each tuple, is unique in a relation., (a) Rows, (b) Key, (c) Attributes, (d) Fields, , 1, , 2., , A relational database can have how many type of keys in a table ?, (a) Candidate Key (b) Primary Key, (c) Foreign Key (d) All of these, , 1, , 3., , Which one of the following uniquely identifies the tuples / rows in a relation., (a) Secondary Key (b) Primary Key, (c) Composite Key (d) Foreign Key, , 1, , 4., , The Primary key is selected from the set of __________., (a) Composite Key, (b) Determinants (c) Candidates Key (d) Foreign Key, , 1, , 5., , Which of the following is a group of one or more attributes that uniquely identifies a row?, (a) Key (b) Determinant, (c) Tuple(d) Relation, , 1, , 6., , Which of the following attributes cannot be considered as a choice for Primary Key ?, (a) Id(b) License number, (c) Dept_Id, (d) Street, , 1, , 7., , An attribute in a relation is a foreign key if it is the ______ key in any other relation., (a) Candidate, (b) Primary, (c) Super, (d) Sub, , 1, , 8., , Consider the table with structure as :, Student(ID, name, dept_name, tot_cred), In the above table, which attribute will form the primary key?, (a) name (b) dept_name(c) Total_credits, (d) ID, , 1, , 9., , Which of the following is not a legal sub-language of SQL ?, (a) DDL (b) QAL(c) DML, (d) TCL, , 1, , 10., , Which of the following is a DDL command?, (a) SELECT (b) ALTER, (c) INSERT, , 1, (d) UPDATE, , 11., , In SQL, which of the following will select only one copy of each set of duplicate rows, from a table., (a) SELECT UNIQUE, (b) SELECT DISTINCT, (c) SELECT DIFFERENT, (d) All of these., , 12., , Which of the following keywords will you use in the following query to display the unique, values of the column dept_name?, SELECT________ dept_name FROM COMPANY;, (a) All (b) From(c) Distinct, (d) Name, , 1, , 13., , The___ clause of SELECT query allows us to select only those rows in the result that, satisfy a specified condition., (a) where (b) from, (c) having, (d) like, , 1, , 93 | P a g e
Page 94 :
14., , Which operator can take wild card characters for query condition?, (a) BETWEN (b) LIKE, (c) IN, (d) NOT, , 1, , 15., , Which operator checks a value against a range of values?, (a) BETWEEN, (b) LIKE, (c) IN, (d) NOT, , 1, , 16., , Which of the following SQL commands retrives data from table(s) ?, (a) UPDATE (b) SELECT, (c) Union, (d) All of these, , 1, , 17., , Which of the following queries contains an error ?, (a) Select * from emp where empid=10003;, (b) Select empid from emp where empid=10006;, (c) Select empid from emp;, (d) Select empid where empid=10009 and lastname= ‘GUPTA’;, , 1, , 18., , Consider the following table namely Employee :, , 1, , Employee_id Name, Salary, 1001, Misha 6000, 1009, Khushi 4500, 1018, Japneet 7000, Which of the names will not be displayed by the below given query ?, SELECT name from Employee WHERE employee_id>1009;, (a) Misha, Khushi (b) Khushi, Japneet, 19., , (c) Japneet, , Which operator perform pattern matching ?, (a) BETWEN, (b) LIKE, (c) IN, , (d)Misha, Japneet, 1, , (d) NOT, , 20., , Consider the following query, 1, SELECT name FROM class WHERE Subject LIKE ‘___ Informatics Practices’;, Which one of the following has to be added into the blank space to select the subject which, has informatics practices as its ending string?, (a) $(b) _, (c) ||(d) %, , 21., , Which operator tests a column for the absence of data(i.e. NULL value) ?, (a) Exist Operator (b) NOT Operator (c) IS Operator (d) None of these, , 1, , 22., , Which clause is used to sort the query result ?, (a) Order By (b) Sort By, (c) Group By, , 1, (d) Arrange By, , 23., , By default ORDER BY clause list the result in ________ order., (a) Descending (b) Any(c) Same, (d) Ascending, , 1, , 24., , Consider the following query, SELECT * FROM employee ORDER BY salary ________, name ______;, To display the salary from greater to smaller and name in alphabetical order which of the, following options should be used ?, , 1, , (a), (b), (c), (d), 94 | P a g e, , Ascending, Descending, Asc, Desc, Desc, Asc, Descending, Ascending
Page 95 :
What is the meaning of Remark LIKE “%5%5%”;, (a) Column Remark begin with two 5s, (b) Column Remark ends with two 5s, (c) Column Remark has more than two 5s, (d) Column Remark has two 5s in it, at any position, , 1, , 26., , In SQL, which command(s) is/are used to change a table’s structure/characteristics?, (a) ALTER TABLE (b) MODIFY TABLE (c) CHANGE TABLE (d) All of these, , 1, , 27., , Which of the following is/are the DDL Statement ?, (a) Create, (b) Drop, (c) Alter, , 1, , 25., , (d) All of these, , 28., , A Table can have __________, (a) Many primary keys and many unique keys., (b) One primary key and one unique key, (c) One primary key and many unique keys., (d) Many primary keys and one unique key., , 1, , 29., , Which of the following types of table constraints will prevent the entry of duplicate rows?, (a) Unique, (b) Distinct, (c) Primary Key (d) Null, , 1, , 30., , Consider the following SQL Statement. What type of statement is this ?, INSERT INTO instructor VALUES (10211, ‘SHREYA’ , ‘BIOLOGY’, 69000);, (a) Procedure, (b) DML, (c) DCL, (d) DDL, , 1, , 31., , Which of the following statements will delete all rows in a table namely mytablewithout, deleting the table’s structure., (a) DELETE FROM mytable;’, (b) DELETE TABLE mytable;, (c) DROP TABLE mytable;, (d) None of these., , 1, , 32., , Which of the following query will drop a column from a table ?, (a) DELETE COLUMN column_name;, (b) DROP COLUMN column_name;, (c) ALTER TABLE table_name DROP COLUMN column_name;, (d) None of these, , 1, , 33., , Logical operator used in SQL are:, (a) AND, OR, NOT, (b) &&, ||, !, , 1, , 34., , (c) $,|,!, , (d) None of these, , Which of the following requirement can be implemented using a CHECK constraint?, (a) Student must be greater than 18 years old., (b) Student must be form a BRICS Country (Brazil, Russia, India, China, South, Africa), (c) Student’s roll number must exist in another table(say, namely Eligible), (d) None of these, , 95 | P a g e, , 1
Page 96 :
35., , An attribute in a relation is termed as a foreign key when it reference the _____ of another, relation., (a) Foreign Key (b) Primary Key, (c) Unique Key, (d) Check Constraint, , 1, , 36., , Data integrity constraints are used to :, (a) Control the access and rights for the table data., (b) Ensure the entry of unique records in a table., (c) Ensure the correctness of the data entered in the table as per some rule or condition, etc., (d) Make data safe from accidental changes., , 1, , 37., , A relationship is formed via _______ that relates two tables where one table references, other table’s key., (a) Candidate Key (b) Primary Key (c) Foreign Key, (d) Check Constraint, , 1, , 38., , What is the maximum value that can be stored in NUMBERIC(4,2)?, (a) 9999.99 (b) 99.9999, (c) 99.99, (d) 9.99, , 1, , 39., , What should be the data type for the column Pricestoring values less than Rs.1000 e.g., 200.21, (a) VARCHAR(50) (b) NUMBER, (c) NUMBER(5,2) (d) NUMBER(6), , 1, , 40., , What is anamein the following SQL Statement ?, SELECT aname FROM table1 UNION SELECT aname FROM table2;, (a) row name, (b) column Name (c) table name (d) database name, , 1, , 41., , Data manipulation language (DML) includes statements that modify the_____ of the, tables of database., (a) Structure, (b) Data, (c) User, (d) Size, , 1, , 42., , All aggregate functions ignore NULLs except for the __________ function., (a) Distinct, (b) Count(*), (c) Average() (d) None of these, , 1, , 43., , Which of the following are correct aggregate functions in SQL, (a) AVERAGE(), (b) MAX(), (c) COUNT(), , 1, (d) TOTAL(), , 44., , Identify the correct INSERT queries from the following :, (a) INSERT INTO Persons(‘xxx1’, ‘yyy1’);, (b) INSERT INTO Persons(LastName, FirstName), Values (‘xxx’, ‘yyy’);, (c) INSERT INTO Persons Values(‘xxx1’ , ‘yyy1’);, (d) INSERT INTO Persons Value(‘xxx1’ , ‘yyy1’);, , 45., , Aggregate functions can be used in the select list or the ____ clause of the select statement. 1, They cannot be used in a _______ clause., (a) Where, having, (b) Having, where (c) Group by, having (d) Group by where, , 46., , What is the meaning of “HAVING” clause in SELECT query., (a) To filter out the summary groups., (b) To filter out the column groups., (c) To filter out the row and column values., , 96 | P a g e, , 1, , 1
Page 97 :
(d) None of the mentioned., 47., , 48., , Which of the following is not a text function?, (a) TRIM (), (b) TRUNCATE(), (c) LEFT(), , What will be returned by the given query ?, SELECT INSTR(‘INDIA’, ‘DI’);, (a) 2, (b) 3, (c) -2, , 1, (d) MID (), , 1, (d) -3, , 49., , What will be returned by the given query ?, SELECT ROUND(153.669,2);, (a) 153.6 (b) 153.66, (c) 153.67, (d) 153.7, , 1, , 50., , What will be returned by the given query?, SELECT month(‘2020-05-11’);, (a) 5 (b) 11, (c) May, (d) November, , 1, , 97 | P a g e
Page 98 :
Fill in the Blanks, 1., , The SQL keyword _______ is used to specify the table(s) that contains the data to be 1, retrieved., , 2., , The ________ command of SQL lets you make queries to fetch data from tables., , 1, , 3., , To remove duplicate rows from the result of a query, specify the SQL qualifier_____ in select, list., , 1, , 4., , To obtain all columns, use a(n) _______ instead of listing all the column names in the select, list., , 1, , 5., , The SQL _______ clause contains the condition that specifies which rows are to be selected., , 1, , 6., , The SQL keyword _______ is used in SQL expressions to select records based on patterns., , 1, , 7., , The ________ operator is used for making range checks in SELECT queries., , 1, , 8., , The null values in a column can be searched for in a table using _____ ______ in the WHERE, clause of SELECT query., , 1, , 9., , To sort the rows of the result table, the _____ _____ clause is specified., , 10., , Columns can be sorted in descending sequence by using the SQL keyword ________., , 1, , 11., , By default, ORDER BY clause lists the records in _______ order., , 1, , 12., , A database can be opened with _________ <database> command., , 1, , 13., , _______ _______ command is used to create new relations in a database, , 1, , 14., , A ______ is a condition or check applicable on a field or set of fields., , 1, , 15., , The _________ constraint creates a foreign key., , 1, , 16., , To define a column as a primary key, _______ ________ constraint is used in CREATE, TABLE., , 1, , 17., , _______ ________ is used to insert data in an existing table., , 1, , 18., , Rows of a table can be deleted using ________ command., , 1, , 19., , To increase the size of a column in an existing table, use commond _________., , 1, , 20., , _______ _______ command removes a table from a database permanently., , 1, , 21., , _______ _______ command is used to alter the definition of already created table., , 1, , 98 | P a g e
Page 99 :
22., , To remove table data as well table structure, use command ______ ________, , 1, , 23., , Use _____ _______ command to add new columns in an existing table., , 1, , 24., , A column added via ALTER TABLE command initially contains _____ value for all rows., , 1, , 25., , Issue ______ command to make changes to table permanent., , 1, , 26., , The ______ _______ clause is used to divide result of SELECT query in groups., , 1, , 27., , To specify condition with a GROUP BY clause, _______ clause is used., , 1, , 28., , Only _______ functions are used with GROUP BY clause., , 1, , 29., , Nested grouping can be done by providing ________ ______ in the GROUP BY expression. 1, , 30., , The _________ clause is used in SELECT queries to specify filtering condition for groups., , 1, , 31., , Aggregate Functions cannot be used in __________clause of the Select query., , 1, , 32., , The SQL built-in function ____ total values in numeric columns., , 1, , 33., , The SQL built-in function ____ computes the average of values in numeric columns., , 1, , 34., , The SQL built-in function ____ obtains the largest value in a in numeric columns., , 1, , 35., , The SQL built-in function ____ obtains the smallest value in a in numeric columns., , 1, , 36., , The SQL built-in function ____ computes the number of rows in a table., , 1, , 37., , The functions that work with one row at a time are _____ _____ functions., , 1, , 38., , To compare an aggregate value in a condition, _______ clause is used., , 1, , 39., , In equi-join, the join condition joins the two tables using _______ operator, , 1, , 40., , To get a substring of a string other than Substr() function ______ is also used., , 1, , 41., , To get the day part of a date___ function is used., , 1, , 42., , To get day name from a date ____ function is used., , 1, , 43., , To remove a character from the right side of a string, _____ function is used, , 1, , 44., , To get the current date, _______ ________ function is used., , 1, , 45., , An SQL _________ clause combines records from two or more tables in database., , 1, , 46., , An _______ is specific type of join that uses only equality comparisons in the join-condition. 1, , 99 | P a g e
Page 100 :
47., , _____ join select all data starting from the left table and matching rows in the right table., , 1, , 48., , _____ join is a reversed version of left join., , 1, , 49., , _____ join produces a data set that includes only those rows from the left table which have, matching rows from the right table., , 1, , 50., , The avg() function in MySQL is an example of _______ function., , 1, , True and False Questions, 1., , A primary key can store empty values in it., , 1, , 2., , Common attribute of two tables is called a foreign key., , 1, , 3., , A common attribute of two tables is called a foreign key it is the primary key in one table and, the other table reference it., , 1, , 4., , Part of SQL which creates and defines tables and other database objects, is called DDL, , 1, , 5., , Part of SQL which manipulates data in tables, is called TCL, , 1, , 6., , Part of SQL which access and manipulates data in tables is called DML, , 1, , 7., , Part of SQL which controls transactions, is called TCL., , 1, , 8., , MySQL is name of customized query language used by Oracle., , 1, , 9., , SQL is a case sensitive., , 10., , The condition in a WHERE clause in a SELECT query can refer to only one value., , 1, , 11., , SQL provides the AS keyword, which can be used to assign meaningful column name to the, results of queries using the SQL built-in functions., , 1, , 12., , SQL is a programing language., , 1, , 13., , SELECT DISTINCT is used if a user wishes to see duplicate columns in a query., , 1, , 14., , ORDER BY can be combined with SELECT statement., , 1, , 15., , DELETE FROM <table> command is same as DROM TABLE <table> command., , 1, , 16., , The unique constraint can only be defined once in the CREATE TABLE command., , 1, , 17., , Unique and Primary Key constraints are the same., , 1, , 18., , Tuple based constraints can use multiple columns of the table., , 1, , 100 | P a g e
Page 101 :
19., , The table based constraints can use multiple column of the table., , 20., , You can add a column with a NOT NULL constraint using ALTER TABLE, only to a table 1, that contains no rows., , 21., , You can use the INSERT statement only to add one new row and not multiple new rows to, an existing table., , 1, , 22., , The HAVING and WHERE clause are interchangeable., , 1, , 23., , The HAVING clauses can take any valid SQL function in its condition., , 1, , 24., , Truncate() is a text function., , 1, , 25., , Length() is a numeric function., , 1, , 26., , Functions MID() and SUBSTR() do the same thing., , 1, , 27., , INSTR() and SUBSTR() work identically., , 1, , 28., , Natural Join contains the duplicate columns, , 1, , 29., , Equi Join contains the duplicate columns, , 1, , 30., , Non- Equi Join is the name of Natural Join, , 1, , 101 | P a g e, , 1
Page 102 :
Very Short Answer Questions, 1., , What is a primary key?, , 1, , 2., , What is a unique key ? It is a Primary key?, , 1, , 3., , How many primary key and unique keys can be there in a table?, , 1, , 4., , What is a foreign key?, , 1, , 5., , What is a composite primary key?, , 1, , 6., , What is a tuple, , 1, , 7., , Give some examples of DDL commands., , 1, , 8., , What is DML ?, , 1, , 9., , Give some examples of DML commands. Or Write the name of any two DML Commands of, SQL ?, , 10., , In SQL,write the query to display the list of tables stroe in database., , 1, , 11., , What are constraints?, , 1, , 12., , Give some examples of integrity constraints., , 1, , 13., , What is the role of NOT NULL constraint?, , 1, , 14., , What is the role of UNIQUE constraints ?, , 1, , 15., , What is the role of FOREIGN KEY constraints?, , 1, , 16., , An NULL values are same as a zero or a blank space?, , 1, , 17., , What will the SELECT ALL command do?, , 1, , 18., , What is wrong with following statement ?, SELECT * FROM Employee, WHERE grade = NULL;, Write the corrected form of the above SQL Statement., , 1, , 19., , Which SQL aggregate function is used to count all records of a table?, , 1, , 20., , Write a query to create a string from the ASCII values 70,65,67,69, , 1, , 21., , Write a query to concatenate the two strings : “Hello” and “World”, , 1, , 22., , Display 4 characters extracted from 5th right character onwards from the string ‘ABCDEFG’ 1, , 23., , Convert and display string ‘Large’ into uppercase, , 102 | P a g e, , 1
Page 103 :
24., , Write a query to remove leading space of the string ‘, , RDBMS MySQL’., , 25., , Display the position of occurrence of string ‘OR’ in the string ‘CORPORATE FLOOR’, , 1, , 26., , How many characters are there in the string ‘CANDIDE’, , 1, , 27., , Write a query to extract 2 digit year from a string ‘USS/23/67/09’. The last two character tell, the year., , 1, , 28., , Write a query to extract institute code from a string ‘USS/23/67/09’. The first three characters, tell the institute code., , 1, , 29., , Write a query to find out the remainder of 11 divide by 4., , 1, , 30., , Write a query to round off value 15.193 to one decimal place., , 1, , 31., , Write a query to find out the square root of value 26., , 1, , 32., , Write a query to truncate value 15.79 to 1 decimal place., , 1, , 33., , Write a query to display current date on your system., , 1, , 34., , Write a query to extract month part from date 3rd Feb 2021, , 1, , 35., , Write a query to display name of weekday for date 03rd Feb 2021, , 1, , 1, , ANSWER, Multiple Choice Questions, 1, 5, 9, , (b) Key, (a) Key, (b) QAL, , 2 (d) All of these, 6 (d) Street, 10 (b) ALTER, , 13, 17, 21, 25, , (a) where, (d), (c) IS Operator, (d), , 14, 18, 22, 26, , (a) Unique, (a), (b)Foreign Key, (b) Data, (c) Group by,, having, 49 (c) 153.67, , 30, 34, 38, 42, 46, , 29, 33, 37, 41, 45, , 103 | P a g e, , (b) LIKE, (a) Misha, Khushi, (a) Order By, (a) ALTER, TABLE, (b) DML, (a) and (c), (c)99.99, (b)Count(*), (a), , 50 (a) 5, , 3 (b) Primary Key, 7 (b) Primary, 11 (b) SELECT, DISTINCT, 15 (a) BETWEEN, 19 (b) LIKE, 23 (d) Ascending, 27 (d) All of these, , 4 (c) Candidate Key, 8 (d) ID, 12 (c) Distinct, 16, 20, 24, 28, , (b) SELECT, (d) %, (c) Desc, Asc, (c), , 31, 35, 39, 43, 47, , 32, 36, 40, 44, 48, , (c), (c), (b) column Name, (b)And (c), (b) 3, , (a), (b) Primary Key, (c) NUMBER(5,2), (b)And (c), (b) TRUNCATE()
Page 104 :
Fill in the Blanks, 1, 5, 9, 13, 17, 21, 25, 29, 33, 37, 41, 45, 49, , FROM, WHERE, ORDER BY, CREATE TABLE, INSERT INTO, ALTER TABLE, COMMIT, MULTIPLE, FIELDS, AVG(), SINGLE ROW, DAY(), JOIN, INNER, , 2, 6, 10, 14, 18, 22, 26, 30, , SELECT, LIKE, DESC, CONSTRAINT, DELETE, DROP TABLE, GROUP BY, HAVING, , 3, 7, 11, 15, 19, 23, 27, 31, , DISTINCT, BETWEEN, ASCENDING, REFERENCES, ALTER TABLE, ALTER TABLE, HAVING, WHERE, , 4, 8, 12, 16, 20, 24, 28, 32, , ASTRIK(*), IS NULL, USE, PRIMARY KEY, DROP TABLE, NULL, AGGREGATE, SUM(), , 34, 38, 42, 46, 50, , MAX(), HAVING, DAYNAME(), EQUI-JOIN, AGGREGATE, FUNCTION, , 35, 39, 43, 47, , MIN(), =, RTRIM(), LEFT JOIN, , 36, 40, 44, 48, , COUNT(), MID(), CURDATE(), RIGHT JOIN, , 2, 6, 10, 14, 18, 22, 26, 30, , False, True, False, True, False, False, True, False, , 3, 7, 11, 15, 19, 23, 27, , True, True, True, False, True, False, False, , 4, 8, 12, 16, 20, 24, 28, , True, False, False, False, True, False, False, , True / False, 1, 5, 9, 13, 17, 21, 25, 29, , False, False, False, False, False, False, False, True, , Very Short Answer Questions, 1., , A Primary key is a field or a combination of fields that can uniquely identify a row/tuple in a 1, table/relation., , 2., , A Unique key in table/relation is any non-primary key field which also stores unique values 1, for each row just like a primary-key does. But only one key is designated as primary key. So, unique refers to a unique non-key field of a table., , 3., , There can be multiple unique keys in a table but there can be only primary key in a table., , 1, , 4., , A foreign key is a field of a table which is the primary key of another table through a foreign, key a relationship is established between two tables., , 1, , 5., , If a table / relation has a primary key which is a combination of multiple columns of a table,, it is known as a composite primary key., , 1, , 6., , A tuple refers to a row of relation., , 1, , 7., , CREATE, ALTER, DROP, , 1, , 8., , DML refers to the Data Manipulation Language component of SQL. The DML commands, are used to manipulate and query upon the data stored in various tables of a database., , 1, , 104 | P a g e
Page 105 :
9., , INSERT, UPDATE, SELECT and DELETE, , 1, , 10., , SHOW TABLES;, , 1, , 11., , Constraints are the rules or conditions imposed on various attributes of a table in a database, so that only the data that satisfy these rules and conditions can get stored in the data table., , 1, , 12., , NOT NULL, PRIMARY KEY, UNIQUE, CHECK, , 1, , 13, , It indicates that in the data being inserted, the column must have some value and can not be, left NULL., , 1, , 14, , This constraint ensures that for an attribute there will be unique value for each row and no, value is being repeated in any other row for that attribute., , 15, , This constraint is used to ensure the referential integrity of data in the table. It matches the, value of the column designated as the foreign key in one table with another table’s Primary, key., , 1, , 16, , No, A Null value is not the same aa zero or a blank space. A zero is a legal numeric value, and blank space is legal character value, whereas NULL is a legal empty value that cannot, be accessed or compared with other values., , 1, , 17, , The SELECT ALL command will fetch all the rows from a table as per the defined commands., , 1, , 18, , A relation operator ‘=’ is not used with the NULL clause., The Corrected form is :, SELECT * FROM Employee, WHERE grade is NULL;, , 1, , 19., , COUNT(*), , 20., , SELECT CHAR(70,65,67,69);, ----------------------------------FACE, , 1, , 21, , SELECT CONCAT(‘Hello’, ‘World’);, ----------------------------------------HelloWorld, , 1, , 22, , SELECT SUBSTR(‘ÁBCDEFG’,-5,4) ‘SUBS’;, ----------------------------------------------------CDEF, , 1, , 23, , SELECT UPPER(‘Large’) ‘uppercase’;, ----------------------------------------------- LARGE, , 1, , 24, , SELECT LTRIM(‘, , 1, , 105 | P a g e, , RDBMS MySQL’);
Page 106 :
------------------------------------------------RDBMS MySQL, 25, , SELECT INSTR(‘CORPORATE FLOOR’, ‘OR’);, ---------------------------------------------------------2, , 1, , 26, , SELECT LENGTH(‘CANDIDE’), --------------------------------------7, , 1, , 27, , SELECT RIGTH(‘ÚSS/23/67/09’,2);, ------------------------------------09, , 1, , 28, , SELECT LEFT(‘ÚSS/23/67/09’,3);, ------------------------------------USS, , 1, , 29., , SELECT MOD(11,4);, -----------------------3, , 1, , 30, , SELECT ROUND(15.193,1);, --------------------------15.2, , 1, , 31, , SELECT SQRT(26);, ---------------------5.09901951, , 1, , 32, , SELECT TRUNCATE(15.79,1);, -----------------------------------15.7, , 1, , 33., , SELECT CURDATE();, , 1, , 34, , SELECT MONTH(‘2021-02-03’);, --------------------------------------02, , 1, , 35, , SELECT DAYNAME(‘2021-02-03’);, --------------------------------------Wednesday, , 1, , 106 | P a g e
Page 107 :
SHORT ANSWER QUESTIONS, 1., , Explain each of the following with illustrations using a table, (i), Candidate Key, (ii) Primary Key, (iii) Foreign Key, , 3, , 2., , Observe the following tables TRANSACTIONS and CUSTOMERS carefully and answer the, questions that follows :, Table : Transaction, , 2, , TNo, , Type, , Amount, , CNo, , T1, T2, , CREDIT, DEBIT, , 1000, 1500, , C3, C1, , Table : Customer, CNo, CNAME, C1, ZEESHAN, C2, AMAN, C3, JASPREET, (i), (ii), , What is the degree of the table Transaction ? what is the cardinality of the table, Customers ?, Identify the primary key and candidate keys from the table Transcations., , 3., , Are count(*) and count(<column-name>) the same functions? Why/ Why not?, , 2, , 4., , Identify the problem/issue with the following SQL query :, SELECT house, count(*), FROM student;, , 2, , 5., , Consider the following SQL string : ‘Preoccupied’. Write commands to display:, (a) ‘occupied’, (b) ‘cup’, , 2, , 6., , Consider the same string : ‘Preoccupied’. Write commands to display:, (a) The position of the substring ‘cup’ in the string ‘Preoccupied’., (b) The first 4 letters of the string., , 2, , 7., , Anjali writes the following commands with respect to a table employee having fields, empno, 2, name, department, commission., Command1: Select count(*) from employee;, Command2 :Select count(commission) from employee;, She gets the output 4 for the first command but get an output 3 for the second command., Explain the output with justification., , 8., , Gopi Krishna is using a table Employee. It has the following columns :, Code, Name, Salary, Deptcode, He wants to display maximum salary departmentwise. He wrote the following command :, SELECT Deptcode, Max(Salary) FROM Employee;, But he did not get the desired result., Rewrite the above query with necessary changes to help him get the desired output., , 107 | P a g e, , 2
Page 108 :
9., , A relation Vehicles is given below :, Vno, Type, Company, Price, Qty, AW125, Wagon, Maruti, 250000, 25, J0083, Jeep, Mahindra, 4000000, 15, S9090, SUV, Mitsubishi, 2500000, 18, M0892, Mini van, Datsun, 1500000, 26, W9760, SUV, Maruti, 2500000, 18, R2409, Mini van, Mahindra, 350000, 15, Write SQL Commands to :, (a) Display the average price of each type of vehicle having quantity more than 20., (b) Count the type of vehicles manufactured by each company., (c) Display the total price of all the types of vehicles., , 3, , 10., , Shanya Khanna is using a table Employee. It has the following columns :, Admno, Name, Agg, Stream, , 2, , [Column Agg contain Aggregate marks], She wants to display the highest Agg obtain in each Stream., She wrote the following statement:, SELECT Stream, Max(Agg) FROM Employee;, But she did not get the desired result., Rewrite the above query with necessary changes to help her get the desired output., , 11., , Write SQL queries for (i) to (iii), which are based on the following table PARTICIPANTS:, PNO, EVENT, SNAME, CLASS, DOB, P1, DEBATE, SANYAM, 12, 2001-12-25, P2, DEBATE, SHRUTI, 10, 2003-11-10, P3, DEBATE, MEHER, 12, 2001-11-10, P4, QUIZ, SAKSHI, 11, 2002-10-12, P5, QUIZ, RITESH, 12, 2001-10-12, P6, QUIZ, RAHUL, 10, 2003-10-12, P7, CROSSWORD, AMEER, 11, 2002-05-09, P8, CROSSWORD, MINAKSHI, 12, 2001-05-09, (i), To display details of all PARTICIPANTS of class 10 and 12., (ii), To display the SNAME and Class of all PARTICIPANTS in ascending order of, their SNAME., (iii) To display the number of PARTICIPANTS along with their respective CLASS, of, every CLASS., , 3, , 12., , Write ouputs for SQL queries (i) to (iii), which are based on the following tables, CUSTOMERS and PURCHASES :, Table : CUSTOMERS, CNO, CNAME, CITIES, C1, SANYAM, DELHI, C2, SHRUTI, DELHI, C3, MEHER, MUMBAI, C4, SAKSHI, CHENNAI, C5, RITESH, INDORE, C6, RAHUL, DELHI, C7, AMEER, CHENNAI, C8, MINAKSHI, BANGLORE, C9, ANSHUL, MUMBAI, , 3, , 108 | P a g e
Page 109 :
SNO, S1, S2, S3, S4, S5, S6, S7, S8, S9, S10, S11, (i), (ii), (iii), , Table : PURCHASES, QTY, PUR_DATE, 15, 2018-12-25, 10, 2018-11-10, 12, 208-11-10, 7, 2019-01-12, 11, 2019-02-12, 10, 2018-10-12, 5, 2019-05-09, 20, 2019-05-09, 8, 208-05-09, 15, 2018-11-12, 6, 2018-08-04, , CNO, C2, C1, C4, C7, C2, C6, C8, C3, C9, C5, C7, , SELECT COUNT(DISTINCT CITIES) FROM CUSTOMERS;, SELECT MAX(PUR_DATE) FROM PURCHASES;, SELECT CNAME,QTY, PUR_DATE FROM CUSTOMERS, PURCHASES, WHERE CUSTOMERS.CNO=PURCHASES.CNO AND QTY IN (10,20);, , 13., , Write SQL queries for (i) to 9iv), which are based on the tables : CUSTOMERS and, PURCHASES given in above., (i), To Display details of all CUSTOMERS whose CITIES are neither Delhi nor, Mumbai., (ii), To Display the CNAME and CITIES of all CUSTOMERS in ascending order of, their CNAME., (iii) To Display the number of CUSTOMERS along with their respective CITITES in, each of the CITITES., (iv), To Display details of all PURCHASES whose Quantity is more than 15., , 3, /, 4, , 14., , Consider the following table ACTIVITY and COACH and answer the following parts of this, question : Table : ACTIVITY, , 4, , Acode, , ActivityName, , Stadium, , ParticipantsNu, m, , PrizeMone, y, , ScheduleDate, , 1001, , Relay 100 x 4, , Star Annex, , 16, , 10000, , 23-Jan-04, , 1002, , High Jump, , Star Annex, , 10, , 12000, , 12-Dec-03, , 1003, , Shot Put, , 12, , 8000, , 14-Feb-04, , 1005, , Long Jump, , Super, Power, Star Annex, , 12, , 9000, , 01-Jan-04, , 1008, , Discuss Throw, , Super, Power, , 10, , 15000, , 19-Mar-04, , PCode, 1, 2, 3, 109 | P a g e, , Table :COACH, Name, Ahmad Hussain, Ravinder, Janila, , ACode, 1001, 1008, 1001
Page 110 :
4, Naaz, 1003, Give the output of the following SQL queries:, (i), SELECT COUNT(DISTINCT ParticipantsNum) FROM ACTIVITY;, (ii), SELECT MAX(ScheduleDate), MIN(ScheduleDate) FROM ACTIVITY;, (iii) SELECT Name,ActivityName FROM ACTIVITY A, COACH C, WHERE A.Acde=C.Acode AND A.ParticipantsNum=10;, (iv), SELECT DISTINCT ParticipantsNum FROM ACTIVITY;, , 15., , Consider the following table STOCK and DEALERS and answer the following parts of this, question :, Table :STOCK, ItemNo, , Item, , Dcode, , Qty, , UnitPrice, , StockDate, , 5005, 5003, , Ball Pen 0.5, Bal Pen 0.25, , 102, 102, , 100, 150, , 16, 20, , 31-Mar-10, 01-Jan-10, , 5002, 5006, 5001, , Gel Pen Premium, Gel Pen Classis, Eraser Small, , 101, 101, 102, , 125, 200, 210, , 14, 22, 5, , 14-Feb-10, 01-Jan-09, 19-Mar-09, , 5004, 5009, , Eraser Big, Sharpener Classis, , 102, 103, , 60, 160, , 10, 8, , 12-Dec-09, 23-Jan-09, , Table :DEALERS, Dcode, 101, 103, 102, , Dname, Reliable Stationers, Classis Plastics, Clear Deals, , Give the output of the following SQL queries:, (i), SELECT COUNT(DISTINCT Dcode) FROM STOCK;, (ii), SELECT QTY*UnitPrice FROM STOCK, WHERE ItemNo=5006;, (iii) SELECT Item, Dname FROM STOCK S DEALERS D, WHERE S.Dcode=D.Dcode AND ItemNo=5004;, (iv), SELECT MIN(StockDate) FROM STOCK;, , 110 | P a g e, , 4
Page 111 :
ANSWER, Short Answer Questions, 1., , (i) Candidate Key :It refers to any column/attribute that can uniquely identify record in a, table., (ii) Primary key : It referes to designated attribute(s)/column(s) that uniquely identifies a, row/tuple in a table/relation. It is one of the candidates keys., (iii) Foreign key :is an attribute in a table which is the primary key in linked table, , 2., , (i) Degree of the table TRANSACTIONS=4, Cardinality of table CUSTOMERS=3, (ii) TNO PRIMARY KEY; TNO, CNO CANDIDATES KEYS, , 3, , No, Count(*) and Count(<column-name>) are not the same., While count(*) counts and return the number of records in a table, count(<column-name>), counts number of records where the mentioned column-name is not null., , 4, , The problem with the given SQL query is that there is no GROUP BY clause is given and, thus, it will lead to an error., The reason being that the select list use COUNT() function, which is an aggregate function,, along with a field. When we use an aggregate function in the select list along with a database, field, we need to add a GROUP BY clause., To correct the error it should use GROUP BY clasue., SELECT house, count(*) FROM student, GROUP BY house;, , 5., , (a) SELECT substr(‘’Preoccupied’, 4); OR SELECT substring(‘Preoccupied’,4);, Or, SELECT mid(‘’Preoccupied’, 4);, (b) SELECT substr(‘’Preoccupied’, 6,3); OR SELECT substring(‘Preoccupied’,6,3);, Or, SELECT mid(‘’Preoccupied’, 6,3);, , 6, , (a) SELECT instr(‘Preoccupied’, ‘cup’);, (b) SELECT left(‘Preoccupied’, 4);, , 7., , The Count(*) function returns the total number of records in the table while count(<field>), will return the count of non-null values in the given field and this is the reason for the different, results by the given queries above., The field commission must be containing a NULL value and thus count(commission) returned, the count of non-null values and count(*) return total number of records (Irrespective of, NULL values in the field)., , 8, , SELECT Deptcode,Max(Salary), FROM Employee, GROUP BY Deptcode;, , 9, , (a) SELECT Type, avg(Price) FROM Vehicle GROUP BY Type having Qty>20;, (b) SELECT Company, count(Distinct Type) FROM Vehicle GROUP BY Compnay;, , 111 | P a g e
Page 112 :
(c) SELECT Type, Sum(Price*Qty) FROM Vehicle GROUP BY Type;, , 10., , 11, , SELECT Stream, MAX(Agg), FROM Employee, GROUP BY Stream;, (i), , (ii), (iii), 12, , (i), , (ii), , (iii), , 13, , (i), (ii), (iii), (iv), , 14, , (i), , (ii), , (iii), , (iv), , 112 | P a g e, , SELECT * FROM PARTICIPANTS WHERE CLASS IN(10,12);, OR, SELECT * FROM PARTICIPANTS WHERE CLASS = 10 OR CLASS=12;, SELECT SNAME, CLASS FROM PARTICIPANTS ORDER BY SNAME;, SELECT COUNT(*), CLASS FROM PARTICIPANTS GROUP BY CLASS;, COUNT(DISTINCT CITITES), ------------------------------5, MAX(PUR_DATE), ---------------------2019-05-09, CNAME, QTY, PUR_DATE, ---------------------------------------------SANYAM, 10, 2018-11-10, RAHUL, 10, 2018-10-12, MEHER, 20, 2019-05-09, SELECT * FROM CUSTOMER WHERE CITITES NOT IN(‘DELHI’,, ‘MUMBAI’);, SELECT CNAME, CITITES FROM CUSTOMERS ORDER BY CNAME;, SELECT COUNT(*), CITIES FROM CUSTOMERS GROUP BY CITIES;, SELECT * FROM PURCHASES WHERE QTY>15;, , COUNT(DISTINCT ParticipantsNum), ------------------------------3, MAX(ScheduleDate), MIN(ScheduleDate), --------------------------------------------------------19-Mar-04, 12-Dec-03, Name, ActivityName, -----------------------------------Ravubder, Discuss Throw, DISTINCT ParticipantsNum, ----------------------------------16, 10, 12
Page 113 :
15., , (i) COUNT(DISTINCT Dcode), -----------------------------3, (ii) QTY*UnitPrice, -----------------4400, (iii) Item, Dname (iv) MIN(StockDate), ----------------------------------------------Eraser Big Clear Deals, 01-Jan-09, , CASE STUDY BASED QUESTIONS, 1., , A library uses a database management system (DBMS) to store the details of the books that, it stocks, it registered members and the book-loans that the library has made. These details, are stored in a database using the following three relations., Name of the Database : KV Library, • Book (BookID : Char(5), Title : Varchar(25), Author :Varchar(25), Publisher :, Varchar(100)), • Member(MemberID:Char(5), LastName:Varchar(25), FirstName:Varchar(25),, Correspondence-Address : Varchar(100), Pincode : Char(6), DateofBirth : Date,, EmailID : Varchar(50)), • Loan(MemberID: Char(5), BookID:Char(5), LastDate:Date, DueBackDate:Date,, Returned :Boolean), Note : The Library does not stock more than one copy of the same book., (a) Identify the table that uses a composite primary key from the library database., (i), Book Table (ii) Member Table (iii) Loan Table (iv) all of these, (b) I. Identify the possible alternate keys from relations Book and Member., (i) Book : Title (ii) Books Author (iii) Member:EmailID (iv) Member:FirstName’, II. Can the Loan relation have an alternate key ?Why ?, , 1, , (c) Relations Book and Member have the following records :, Book, BookID, Title, Author, Publisher, , 1, , B1103, B2902, B2950, B3100, B3275, Member, BookID, B1103, B2902, B2950, B3100, B3275, , 113 | P a g e, , -, , -, , -, , 1, 1
Page 114 :
Write an example of the valid record for the loan relation. Write a query to insert a, valid record in the Loan relation., (d) Write a SQL query to retrieve the names and email addresses of the members who, have not returned their books., 2, , A library uses database management system(DBMS) to store the details of the books that it, stocks, its registered membes and the book-loan that the library has made. These details are, stored in a database using the following three relations. Name of the Database : KV Library, • Book (BookID : Char(5), Title : Varchar(25), Author :Varchar(25), Publisher :, Varchar(100)), • Member(MemberID:Char(5), LastName:Varchar(25), FirstName:Varchar(25),, Correspondence-Address : Varchar(100), Pincode : Char(6), DateofBirth : Date,, EmailID : Varchar(50)), • Loan(MemberID: Char(5), BookID:Char(5), LastDate:Date, DueBackDate:Date,, Returned :Boolean), Note : The Library does not stock more than one copy of the same book., , (a) Identify following types of keys from all the relations of the given database Foreign, keys along with parent relations., (b) Can a relation have multiple foreign keys? Give example., (c) Can a foreign key be part of a primary key? Give example., (d)Write a SQL query to retrieve the names and email addresses of the members, belonging to KVS (they have email ids as
[email protected]) and wo have not returned their, books., 3., , 1, , 2, 1, 1, 1, , FurnFly is a furniture company selling furniture to customers of its store and operates a, follows:, • The store does not keep the furniture in stock., • The company places orders for the furniture required from its suppliers ONLY AFTER, a customer places an order at the store., • When the ordered furniture arrives at the store, the customer is informed via, telephone or e-mail that it is ready for delivery., • Customers often order more than one type of furniture on the same order, for example,, a sofa, two puffy chairs and centre table., Details of the furniture, customers and orders are to be stored in a relational database using, the following four relations :, Database Name :FurnFly Furnishers, Furniture (FurnitureID : Char(7), FurnitureName : Varchar(50), Category : Varchar(25),, Price : Float, SupplierName : Varchar(100)), CustomerOrder(OrderId : Number(8,0), CustomerID : Char(10), OrderDate:Date), CustomerOrderLine :(OrderID : Number(8,0), FurnitureID: Char(7), Quantity:, Number(4,0)), Customer :(CustomerID : Char(10), CustomerName:Varchar(100), EmailAddress :, Varchar(30), TelephoneNumber: Number(15,0)), (a) Identify the relationships among tables., (b) Identify the relation having composite primary key and its primary key., (c) Write a SQL query to create table customerOrder. It should also define required, primary key and foreign key(s), , 114 | P a g e, , 1, 1, 1
Page 115 :
(d) A fault has been identified with the furnitureID number 6281. The manager needs to, known how many orders need to be recalled. Write a SQL query for the same., (e) A customer with ID number ‘C5104’ wants to change his registered telephone number, as 9988776655. Write a SQL query to achieve this., 4., , 1, 1, , Rachana Mittal runs a beauty parlor. She uses a database management system(DBMS) to, store the information that she needs to manage her business. This information includes, customer contact details, staff names, the treatments that the parlor offer (for example, ‘’Hair, Massage’) and appointment that customers have made for treatments. A separate, appointment must be made for each treatment., The details are stored in a database using the following four relations:, Customer: (CustomerID, FirstName, LastName, TelephoneNumber, EmailAddress), Staff :(StaffID, FirstName,LastName, IsQualified), Treatment: (TreatmentName,Price,TimeTaken,NeedsQualification), Appointment : (CustomerID,TreatmentName,ApDate,ApTime), • The IsQualifiedattribute for a member of staff stores one of the value True or False,, to indicate if the member of staff is fully qualified or not., • The NeedsQualifictionattribute for a treatment stores True or False to indicate if the, treatment can only be given by a qualified member of staff., • The TimeTakenattribute for a treatment is the number of minutes (a whole number), that the treatment takes., (a) Write a SQL statement to create the table staff., 1, (b) Write a query to Insert a record in the table Staff with following data ;, (2009, ‘Sheril’, ‘Mark’, ‘True’), (c) Which table’s records can be deleted without affecting any other table?, 1, (i), Customer, (ii) Staff, (iii) Treatment, (iv) Appointment, (d) Write a query to Modify table Appointment to add a new column StaffID, which, should hold a legal StaffID value from the staff table., (e) Rachana wants to send e-mail advertisement to all the customers who had a ‘RF 1, Facial’ treatmentin 2020. To send the email, the customer’s email address, firstname, and lastname are needed., Write a SQL query to retrieve the email address, firstname and lastname of each, customer to whom email should be sent., , 5., , Consider the table STUDENT given below:, RollNo, 1, 2, 3, 4, 5, 6, 7, 8, , Name, Anand, Chetan, Geet, Preeti, Saniyal, Maakhiy, Neha, Nishant, , Class, XI, XII, XI, XII, XII, XI, X, X, , DOB, 6/6/97, 7/5/94, 6/5/97, 8/8/95, 8/10/95, 12/12/94, 8/12/95, 12/6/95, , (a) State the command that will give output as:, 115 | P a g e, , Gender, M, M, F, F, M, F, F, M, , City, Agra, Mumbai, Agra, Mumbai, Delhi, Dubai, Moscow, Moscow, , Marks, 430, 460, 470, 492, 360, 256, 324, 429
Page 116 :
Name, Anand, Chetan, Geet, Preeti, , (i), (ii), (iii), (iv), , Select Name from student where class= ‘XI’ and class=‘XII’;, Select Name from student where not class= ‘XI’ and class=‘XII’;, Select Name from student where city = ‘Agra’ or city = ‘Mumbai’;, Select Name from student where city IN(‘Agra’ , ‘Mumbai’);, , Choose the correct option :, (a) Both (i) and (ii), (b) Both (iii) and (iv), (c) any of the option (i) , (ii) and (iv), (d) Only (iii), (b) What will be the output of the following command?, Select * from student where gender= ‘F’ order by marks;, (i), RollNo, 4, 3, 7, 6, , Name, Preeti, Geet, Neha, Maakhiy, , Class, XII, XI, X, XI, , DOB, 8/8/95, 6/5/97, 8/12/95, 12/12/94, , Gender, F, F, F, F, , City, Mumbai, Agra, Moscow, Dubai, , Marks, 492, 470, 324, 256, , (ii), RollNo, 6, 7, 3, 4, , Name, Maakhiy, Neha, Geet, Preeti, , Class, XI, X, XI, XII, , DOB, 12/12/94, 8/12/95, 6/5/97, 8/8/95, , Gender, F, F, F, F, , City, Dubai, Moscow, Agra, Mumbai, , Marks, 256, 324, 470, 492, , (iii), Gender, F, F, F, F, , (iv), 116 | P a g e, , 1, , Marks, 256, 324, 470, 492
Page 117 :
Gender, F, F, F, F, , Marks, 492, 470, 324, 256, , (iii) Prachi has given the following command to obtain the highest marks, SELECT max(Marks) from student where group by class;, But she is not getting the desired result. Help her by writing the correct command., (a) Select max(Marks) from student where group by class;, (b) Select class, max(Marks) from student group by Marks;, (c) Select class, max(Marks) group by class from students;, (d) Select class, max(Marks) from student group by class;, (iv) State the command to display the average marks scored by students of each gender who, are in class XI?, (a) Select Gender, avg(Marks) from student where class= ‘XI’ group by gender;, (b) Select Gender, avg(Marks) from student group by gender where class= ‘XI’;, (c) Select Gender, avg(Marks) group by Gender from student having class= ‘XI’;, (d) Select Gender, avg(Marks) from student group by Gender having class= ‘XI’;, Choose the correct option:, (a) Both (ii) and (iii), (b) Both (ii) and (iv), (c) Both (i) and (iii), (d) Only (iii), (v) Help Ritesh to write the command to display the name of the youngest student., (a) Select Name, min(DOB) from student;, (b) Select Name, max(DOB) from student;, (c) Select Name, min(DOB) from student group by Name;, (d) Select Name, maximum(DOB) from student;, , ANSWER, CASE STUDY BASED QUESTIONS, 1., , (a) (iii) Loan Table, (b) I. (i) Book : Title (ii) Member: EmailID, II. No, the Loan relation cannot have alternate key as its primary key is a composite key, having foreign key., (c) INSERT INTO Loan Values(‘M1255’, ‘B3100’, ‘02/02/2020’, ‘09/02/2020’, False), (d) Select FirstName, LastName, EmailID, From Member, Loan, Where Member.MemberID=Loan.MemberID, AND Returned = ‘False’;, , 2, , (a) Foreign Keys in Relation Loan, MemberID(Parent Table Member), BookID (Parent Table Book), , 117 | P a g e, , 1, , 1
Page 119 :
(e) Select EmailAddress, FirstName,LastName, From Customer C, Appointment A, Where C.CustomerID=A.CustomerID, AND TreatmentName= ‘RF Facial’;, 5., , (i) (b) Both (iii) and (iv), (ii) (b), (iii) (d), (iv) (b) Both (ii) and (iv), (v) (b), , 119 | P a g e
Page 120 :
COMPUTER NETWORK, INTRODUCTION, 1) Guided Media or wired communication channel:, The guided media refers to the different types of cables used in the network., They are of Type, a. Twisted Pair Cable, i. Shielded Twisted Pair (STP), ii. Unshielded Twisted Pair (UTP), b. Coaxial Cables, c. Optical Fibers, 2) Unguided media or Wireless Communication Channel:, The unguided or wireless communication channels referred to a wireless connection to the network. There, is no physical connection given through wires in this channel. The connection will be done through either, sensors, antenna or any other component, a. Microwave, b. Radio Wave, c. Satellite, d. Infrared, e. Laser, f. Bluetooth, 3) Modem:, A modem stands for MOdulator/DEModulator. It works on the function process of Modulation and, Demodulation, 4) Ethernet Card:, It provides an interface between the computer and the network. It is also called as Network Interface, Card., 5) WiFi Card :, The card enables a Wi-Fi connectivity for the computers. It is known as wireless NIC., 6) MAC Address:, A MAC address is a unique address that is assigned by the manufacturer of the NIC Card. It is a 6byte address. Each byte in MAC address is separated by a colon. It looks like:, 20:CY:01:58:4d:LK, 7) NIC:, Network Interface Card is the physical card that can be used to connect the networking media with, the system. It is also called as Ethernet card., 8) HUB:, A hub is a device which is used to connect more than one device in the network., 9) SWITCH:, Switch is a smart Hub, 10) Repeater:, The repeater is a device that amplifies the network over geographical distance, 11) GATEWAY :, It is a device which connects dissimilar networks. It expands the functionality of routers. It is not a, device but a node or workstation or computer connected to the network, , 120 | P a g e
Page 121 :
12) ROUTER:, A router is more powerful and intelligent than hub or switch. It has advanced capabilities as it can, analyze the data and decide the data is packed and send it to the other network. It can handle huge, packets. It can be wired or wireless, both. A wireless router can provides access to many devices like, smartphones, and connected devices, 13) PAN – Personal Area Network:, Personal Area Network refers to the network created by persons or individuals. Let’s understand, with this example. If you are sending files from your smartphone to another smartphone using, Bluetooth or any other app is considered as Personal Area Network. Mostly people using their own, devices like PDAs, Smartphones, Tablets etc. to share the data using Bluetooth or Wi-Fi., 14) LAN – Local Area Network, Local area networks are limited to one specific area and cover limited distance. A network that, spreads up to a building, office, organization or institute is known as Local Area Network., 15) MAN – Metropolitan Area Network, This is an extended form of LAN. It can be spread over cities of one country. It can connect different, cities of a country, 16) Network Topologies:, Topologies are the types of network layout. It provides the interconnection to the network using, cables and network devices, 17) STAR Topology:, A central device (hub or switch) is required to connect all the devices with cables, 18) BUS or linear Topology:, The bus or linear topology uses a single length cable to connect the devices, 19) RING or circular topology:, The bus or linear topology uses a single length cable to connect the devices. This single length cable, has a terminator at both the ends, 20) TREE Topology :, The tree topology is similar to bus topology. In tree topology, the network shapes like a tree with, different nodes connected together., 21) Mesh Topology :, Mesh topology offers excellent connectivity over long distances. In this, each node is connected to, more than one device, 22) Wireless Access Point:, It is wireless router used to connect wireless device to the network, 23) Browser, It is the software to access internet based webpages in the computer, 24) Cookies :, Cookies are plain text files which store the browsing-related information on user’s computer. These, unable you to save password for the website and all the customer setting for the website in the, browser for later visits. You can enable or disable cookies from browser settings. You can either, allow or block third-party cookies on your browser, 25) .Plug-in or Add on or Extension :, A plug-in or add on or extension is software that adds additional functionality to your web browser., It adds a number of features to web browsers. For example, enable emoticons, reading pdfs, languages, etc, , 121 | P a g e
Page 122 :
MCQ, 1) What is an standalone computer system, a. It is a computer system with internet connectivity, b. It is a server, c. It is a computer without any networking, d. None is correct, 2) The main computer in any network is called as, a. Client, b. Server, c. Hub, d. Switch, 3) What is the full form of NIC, a. Network Interchange Card, b. Net Interconnect Card, c. Network Interface Card, d. Network Interconnection Card, 4) Which is called a smart HUB, a. HUB with high speed ports, b. Switch, c. Router, d. All of the Above, 5) A network with all client computer and no server is called, a. Networking, b. Peer to Peer Computing, c. Client Server Computing, d. Any of them, 6) The wireless access point in the networking is also, a. An wireless switch, b. An Wireless Security Point, c. An Address where all the wifi devices connect, d. All of the above, 7) Generally which topology is used in the backbone of Internet, a. BUS, b. STAR, c. RING, d. Any of them, 8) IP Stands for, a. Internet Protocol, b. Intranet Protocol, c. Internet Practice, d. Intranet Practice, 9) Which of this is not a part of URL, a. IP Address, b. Port Number, c. Domain Name, d. None of these, 122 | P a g e
Page 123 :
10) What is the example of Instant Messenger, a. Yahoo messenger, b. WhatApp messenger, c. iMessenger, d. All of them, 11) Which of the following is an browser, a. Chrome, b. Whatsapp, c. Twitter, d. All of them, 12) Repeaters work on the __________ layer, a. Network Layer, b. Physical Layer, c. Application Layer, d. All of the Above, 13) Which device is used to transfer Communication Signal to Long Directions, a. Amplifier, b. Repeater, c. Router, d. All of the Above, 14) Which topology in general uses less wire length compare to other, a. Star Topology, b. Ring Topology, c. Bus Topology, d. All use same Length of Wire, 15) The device with smartly controls the flow of data over the network by hoping is, a. Router, b. Gateway, c. Switch, d. None of them, 16) javascript is a ___________ based language, a. interpretor, b. compiler, c. None, 17) Which one in a micro blogging software, a. Twitter, b. Facebook, c. Whatsapp, d. All of them, 18) Sending the email to any cc means, a. Sending the mail with a carbon copy, b. Sending the mail without a carbon copy, c. Sending the email to all and hiding the address, d. All of the above, 19) The backbone of internet is, a. WAN Network, b. Fibre optical networks across long distances like intercontinental or intra continental, c. Wireless networks, d. All of them, 123 | P a g e
Page 124 :
20) Which is the physical address to identify the Machine uniquely in network, a. IP Address, b. MAC Address, c. Computer Name, d. Your Used ID, 21) Online textual talk is called, a. Video Conference, b. Text Chat, c. Video Call, d. Audio Call, 22) The First Page we generally view when we open the browser is called., a. Default page, b. First page, c. Home page, d. Landing Page, 23) URL stands for, a. Uniform Run Line, b. Uniform Resource Line, c. Uniform Resource Location, d. Uniform Resource Locator, 24) Digital foot print is of ___ types, a. 1, b. 2, c. 3, d. 4, 25) What is noise in the voice channel, a. Cable disturbance, b. Cable sort length, c. Loss of Signal Strength, d. Unwanted disturbance with the genuine signal, 26) php language is used to create, a. Dynamic Website, b. Static Website, c. Both the types of website, d. It is not a programming language, 27) HTML language is used to create, a. Accounting Program, b. Static Website, c. Both website and accounting program, d. It is not a programming language, 28) Google is a, a. Web service, b. Website, c. Program, d. All of it, , 124 | P a g e
Page 125 :
29) When the signal from one wire bleeds into another wire , it is called as, a. Radio waves, b. Infrared, c. Laser, d. None of them, 30) Communication Media can be of ___________ and _____________ type, a. Twisted pair , Shielded Twisted pair, b. Fiber optics , coaxial, c. Guided , Unguided, d. Wire , Laser, 31) To prevent unauthorized access to and / or from the network, a system known as ____________, can, be implemented by hardware and / or software, a. Antivirus, b. Firewall, c. Software, d. Hardware, , 125 | P a g e
Page 126 :
1 MARKS QUESTION, 1) What is the need for a network., 2) Write the full form of following :, a. NIC, b. ICT, c. PCB, d. DND, e. STP, f. UTP, g. CAT-6, h. CRT, i. TFT, j. LED, 3) Expand WAN and MAN, 4) Expand LAN and PAN, 5) What is a Node, 6) Why in NIC needed in the computer?, 7) What is the use of a Server, 8) What is the Latency in Bluetooth Headsets, 9) What is an Networking Topology, 10) How internet is difference from LAN or Networks?, 11) To protect the data in the network from unauthorized access what device is used?, 12) What is the use of ISP in internet networks?, 13) Define the use of IP address, 14) Why STAR network is more efficient in network fault tolerance in place of BUS network., 15) Raju wants to save the password and other setting for the website he will use what to save it in the, computer., 16) Ravi is setting the home page of his browser. He will use ___________ of the browser to set the set, home page., 17) What is the use of modem., 18) Text chatting software used in computer network used which technology to communicate?, 19) What is the use of router?, 20) Keeping Password and OTP in proper safty is called as ____________, 21) ftth network is fasted then STP cable network why is this correct, 22) what do you mean by URL, 23) What is an absolute URL, 24) What is history in the browser ?, 25) What is the use of HyperLink., 126 | P a g e
Page 127 :
2 Marks Questions, 1) What is the difference between STAR and BUS topologies?, 2) www mean internet or not ? Explain with example ?, 3) What is the deference between the http and Https: websites, 4) What are Plug-in or Add on or Extension, 5) Email is our phone uses which protocal, 6) Which address is used to uniquely identify the machines in a network, 7) What s VoIP? Where is it used ?, 8) Which protocol is used to upload files to webserver for creating websites., 9) Please help Amit to understand the parts of Email Address, 10) What is difference between a website and an webpage, 11) What is a gateway and why is it used?, 12) Router is needed for internet to work? Explain if true or false?, 13) When can an HUB be used in place of Switch?, 14) How website is not same as web portal?, 15) What are the common services provided by any web portal?, 16) Google.co.in is a static webpage . The statement is correct or wrong ? Help Raj to define the correct, webpage type ?, 17) What browser setting is needed to do when we access any site in public computer like cyber café?, 18) What in a VPN software, 19) Why we use a domain name address in place of IP address of the Server to access any web site?, 20) Redirection or Popups in the website are to be checked carefully before forwarding? Why is this so, important?, , 127 | P a g e
Page 128 :
CASE BASED QUESTIONS (4 Marks), 1) KVS consultants are setting up a secured network for their office campus at Gurgaon. They are, planning to have connectivity between 3 blocks and the head office at Mumbai. Answer the, questions (a) to (d) after going through the block positions in the campus and other details, which are, given below:, , Distances between various buildings:, Block A to Block C, , 120m, , Block A to Block B, , 55m, , Block B to Block C, , 85m, , New Delhi Campus to Head office, , 2060 Km, , Number of computers:, Block A, , 32, , Block B, , 150, , Block C, , 45, , Head office, , 10, , a. Suggest the most suitable place to house the server with justification., b. Suggest a connection medium to connect Gurgaon campus with head office., c. Suggest the placement of the following devices with justification:, i)Switch, ii)Repeater, d. The organization is planning to provide a high speed link with its head office situated in, Mumbai using a wired connection. Which of the following cables will be most suitable for, this job?, i) Optical Fibre, ii)Co-axial Cable, iii)Ethernet Cable, , 128 | P a g e
Page 129 :
2) Sarguja University is setting up its new academic block in KP Gaon. The University has 3 new, academic block and 1 human resource centre., , The distance between the blocks are given below, , Number of computer in the blocks, , a. Where can we put the internet gateway server, b. Where can we put switch, c. Where we have to fix repeater, d. Where we can have Hub, 3) Zetking industries has set up its new center at Ambikapurfor its office and web based activities. The, company compound has 4 buildings as shown in the diagram below:, , 129 | P a g e
Page 130 :
Center to center distances between various building is as follows:, harsh building to raj building 50m, raj building to fazz building 60m, fazz building to jazz building 25m, jazz building to harsh building, , 170m, , harsh building to fazz building, , 125m, , raj building to jazz building 90m, , Number of computers in each of the buildings is as follows:, harsh building 15, raj building, , 150, , fazz building 15, jazz building 25, a. Suggest the most suitable place to house the server of this organization with a suitable reason., b. Suggest the placement of the following devices with justification., i)Internet connecting device, , ii)switch, , c. The organization is planning to link its sale counter situated in various parts of the same city,, which type of network out of LAN, MAN or WAN will be formed? Justify your answer., d. If there will be connection between all building using mesh topology, suggest where need to, place repeater., 4) “KVS” is planning to setup its new campus at Raipur for its educational activities. The campus has, four(04) UNITS as shown below:, , 130 | P a g e
Page 131 :
a. Suggest an ideal cable layout for connecting the above UNITs, b. Suggest the most suitable place i.e. UNIT to install the server for KVS, c. Which network device is used to connect the computers in all UNITs, d. Suggest the placement of Repeater in the UNITs of above network., 5) Knowledge All Organization has set up its new center at Kolkata for its office and web based, activities. It has 4 blocks of building as shown in the diagram below, , a. Suggest a layout of connections between the blocks, b. Suggest the most suitable place (i.e. block) to house the server of this organization with a, suitable reason, c. Suggest the placement of the following devices with justification, i. Repeater, , 131 | P a g e, , ii. Hub / Switch
Page 132 :
d. The organization is planning to link its front office situated in the city in the hilly region, where cable connection is not feasible , suggest an economic way to connect it with, reasonably high speed, 6) Ramji Training Educational Institute is setting up its centre in RAIPUR with four specialized, departments for Orthopaedics, Neurology and Paediatrics along with an administrative office in, separate buildings. The physical distances between these department buildings and the number of, computers to be installed in these departments and administrative office are given as follows. Answer, the queries as raised by them in (a) to (d), , Shortest distances between various locations in metres:, , Number of Computers installed at various locations are as follows :, , a) Suggest the most suitable location to install the main server of this institution to get efficient, connectivity., b) Suggest the best cable layout for effective network connectivity of the building having server with, all the other buildings., c) Suggest the devices to be installed in each of these buildings for connecting computers installed, within the building out of the following : Gateway, switch, Modem, 132 | P a g e
Page 133 :
d) Suggest the topology of the network and network cable for efficiently connecting each computer, installed in each of the buildings out of the following :, Topologies: Bus Topology, Star Topology, Network Cable: Single Pair Telephone Cable, Coaxial Cable, Ethernet Cable., 7) RAJKUMARMedicos Centre has set up its new centre in Bilaspur. It hasfour buildings as shown in, the diagram given below, , Distances between various buildings are as follows:, , Number of Computers, , As a network expert, provide the best possible answer for the following queries:, a. Suggest a cable layout of connections between the buildings, b. Suggest the most suitable place (i.e. buildings) to house the server of this organization., c. Suggest the placement of the following device with justification, i. Repeater, ii. Hub/Switch, d. Suggest a system (hardware/software) to prevent unauthorized access to or from the network, , 133 | P a g e
Page 134 :
ANSWER, 1. C, 2. B, 3. C, 4. B, 5. B, 6. D, 7. A, 8. A, 9. A, 10. A, 11. A, 12. B, 13. B, 14. C, 15. A, 16. A, 17. A, 18. A, 19. B, 20. B, 21. B, 22. C, 23. D, 24. B, 25. D, 26. C, 27. B, 28. A, 29. C, 30. C, 31. B, 1 MARKS QUESTIONS, 1. Network is the interconnection between systems for resource sharing like printing and internet, sharing., 2. FULL ABBRIBIATION, NIC→Network Interface Card, ICT→Information and Communication Technology, PCB→Printer Circuit Board, DND→Do Not Disturb Directory, STP→Shielded Twisted Pair, UTP→Un-Shielded Twisted Pair, CAT-6→Category 6 Cables, CRT→Cathod Ray Tube, TFT→Thin Film Transistor, LED→Light Emmited Diode, 3. WAN – WIDE AREA NETWORK / MAN – METROPLITON AREA NETWORK, 4. LAN- LOCAL AREA NETWORK / PAN – PERSONAL AREA NETWORK, 134 | P a g e
Page 135 :
5., 6., 7., 8., , Node is the client computer that is connected to a computer, NIC is the card that create an interface between the computer and the internet or network medium, Server is the Computer that serve as the main computer to serve information., Bluetooth Headsets are used to get voice from the source but there is a delay in the voice and the, video played, 9. Networking Topology is physical layout of the networking connection to the computer, 10. Internet is the network of networks and LAN is only a single network, 11. Firewall is used to save the network from un-authorised access, 12. It is the Internet Service Provider for the Clients, 13. IP or Internet Protocol Address is the 32 Bit Address Logical Number to be given to any network for, uniquely identifying the Computers, 14. Because each node is connected directly to the main server and any fault is highly localised, 15. He will us his cookies in the browser to save the password and details, 16. Setting -> default page->home page address, 17. Modem is used to connect Digital computer to Analog Line for Digital data Transfer, 18. They use IM (Instance Messaging) for Text Chatting other then SMS, 19. Router is used to connect all the different networks together. It also forwards and receives different, data packets from different places, 20. Password Security Ethics, 21. Yes ftth is faster the STP because of ftth uses laser to transmit data, 22. URL (Uniform Resource Locator) is the human understandable format for website address., 23. An absolute URL is the complete website address with protocal and landing page details also, 24. History is the link to last visited websites in the browser, 25. Hyperlink is link to another website or page from the current page, 2 MARKS QUESTIONS, 1) STAR Topology is topology in which the all the nodes are connected with central computer. But is, Bus topology a single wire runs across the network and all the nodes are connected to the central bus, 2) www is world wide web and it is the protocol to define the website or web address.e.g., http://www.google.co.in. This address defines that the website is in the internet., 3) http: is the normal Hyper Text Transfer Protocol but https: is the Secured Hyper Text Transfer, Protocal., 4) The software that are installed with the browser for better performance and utility are called the, Plug-in or Add On, 5) Email in our phone uses POP3 protocol to access, 6) The MAC address is used to uniquely identify the machine in a network, 7) VoIP or Voice Over IP is a protocol used to transmit data, 8) FTP or File Transfer Protocol is used to transfer files to the web server for creating web site, 9) Email has used id and the domain name in its complete address, kvs@kvs,gov.in where kvs is used id and kvs,gov.in is domain name, 10) Website is the complete software and webpage is just one of the page from the website like, www.ambikapur.kvs.ac.in is website and, https://ambikapur.kvs.ac.in/admin/content?type=school_class_wise_enrolment_posi is a single web, page, 11) Gateway is the computer used to connect different networks to one network, 12) Router is a dynamic device to connect different networks in real time. Internet cannot work without, routers., 13) Hub is a device that broadcast all the signals so Hub is used in less computers with a limited speed or, bandwidth requirements, 135 | P a g e
Page 136 :
14) Website is a single software and web portal is a combination of both online and offline services, given by the webportal . like www.google.co.in is a website and www.ola.com is aweb portal, 15) The most common services provided by the web portal are web hosting and business website, developments., 16) Google is a dynamic website. It connects us directly to the related websites what are searched., 17) We need to use incognito mode or public mode while accessing internet in the public place., 18) A VPN software is a software that hides the machine address from the network so that no one can, trace the computer in the network, 19) We use Domain name as it is more easy to remember that to remember the IP Address of the, Website., 20) The popups or redirection can be a trap form the hackers to hack your computer so they needed to, check carefully, CASE STUDY (4 MARKS), 1., a., b., c., d., , Block C because of the higest no of computer, VPN in Internet or Satellite communication can be use, Switch in Block A, B and C. repeater in Block C or Head Office, Optical Fiber, , a., b., c., d., , Internet Gateway in the HR Block, Switch in Technology Block and HR Block, Between Law Block and HR Block, In Law Block and Business Block, , a., b., c., d., , Raj Building because of Max Number of Computers, Both in Raj Building, MAN, Jazz Building, , a., b., c., d., , BUS Topology, ADMIN Unit as Max computer are in the Building, Bus / Switch, Between Admin and Finance Building, , 2. ., , 3., , 4., , 136 | P a g e, , ., , .
Page 137 :
Sample Question Paper – 1(Term-2), 2021, Informatics Practices (065), Class 12, Time: 02:00 Hrs, , Marks: 35, , Instructions:, 1. There are 16 questions in the question booklet., 2. Each question is compulsory., 3. The Question paper is divided into four sections - Section A containing 05 questions each, of 01 mark, Section B containing 05 questions each of 02 marks, Section C containing, 04 questions each of 03 marks, Section D containing 02 questions each of 04 marks., 4. Options are available with the questions in Section D., , 137 | P a g e
Page 138 :
SECTION - A (01 MARK QUESTIONS), QNo., 1, , Question, , Marks, , Write the output of the following command?, , 1, , select round(123.789,-2);, , 2, , 3, , 4, , 5, , (a) 100, , (b) 120, , (c) 123.78, , (d) 123.80, , A website is a collection of, , 1, , (a) Webpages, , (b) Webpages, , (c) Webservers, , (d) Hyperlinks, , Which of the following network devices is also known as intelligent hub?, (a) Router, , (b) Gateway, , (c) Repeater, , (d) Switch, , The protocols used to send and receive emails, respectively, are, (a) SMTP, MIME, , (b) SMTP, POP3, , (c) POP3, SMTP, , (d) POP3, MIME, , Which of the following SQL commands may output 24?, (a) select, (b)select, (c) select, (d) select, , 1, , 1, , 1, , day(now());, now();, dayname(now());, month(now());, SECTION - B (02 MARK QUESTIONS), , 6, , Consider the string “Class 12 CS”. Write command to display:, , 2, , (a) the position of string “CS” in the string “Class 12 CS”., (b) Last six characters of the string “Class 12 CS”., 7, , Explain the difference between where and having clauses in SQL with the, help of a suitable example., , 138 | P a g e, , 2
Page 139 :
8, , Consider the below given Student table and answer the questions which, follow:, , 2, , (a) What will be the output of, select sum(roll)+count(roll)+sum(marks)+count(marks), from student;, (b) Write command to update marks equal to 0 where roll number is NULL., , 9, , Given a decimal number 1905.675, write commands in SQL to, (a) round it off to the number 2000., (b) round it off to 1 place after the decimal., , 2, , 10, , Anisha has been given the below given student table:, , 2, , (a) How will she generate the following output using group by and having, statements?, , (b) How will she update the student table to increase marks of all students, by 10% and obtain the following output?, , SECTION - C (03 MARK QUESTIONS), , 139 | P a g e
Page 140 :
11, , A Salesman relation is given below:, , 3, , (a) Write SQL command to display the area-wise count of salesmen for those, areas who have more than 1 salesman., (b) Write SQL command to find the total Sales., (c) Write SQL command to display the Sname and Dojoin of the salesman, who has joined most recently., 12, , How are aggregate functions different from other SQL functions? Ishita is, trying to find the max sales out of all the sales corresponding to Salesmen, having Delhi as address in the Salesman table given in Q11. Write two, different SQL queries (using group by and without using group by) to perform, this task., , 3, , 13, , Predict the output of below given SQL queries, a. select length(ltrim(" ABCD EFGH "));, b. select length(trim(" ABCD EFGH "));, , 3, , c., , 14, , select power(instr(lower('A@123'),'2'),instr(lower('A@123'),'3'));, , Differentiate between the following, a. static and dynamic web page, b. website and webpage, , 3, , SECTION - D (04 MARK QUESTIONS), 15, , Write the SQL commands which will perform the following operations?, a. To display the starting position of your last name (lname) from the, whole name (name)., b. To display dayname, month name and year from today’s date., c. To display the remainder on dividing 3 raised to power 5 by 5., d. To display ‘I am here’ in lower as well as uppercase., OR, Consider the table Salesman with the given data, , Write SQL queries using function to perform the following operation:, a. Display Scode and Sales after rounding off the Sales to 1 decimal, place., b. Display the dayname from Dojoin of Salesman., c. Display the position of occurrence of “a” in the Sname., d. Display three characters from Sname starting from the second, character for those salesmen whose name ends with ‘t’., , 140 | P a g e, , 4
Page 141 :
16, , Indian School, in Mumbai is starting up the network between its different, wings. There are four Buildings named as SENIOR, JUNIOR, ADMIN and, HOSTEL. The distance between various buildings is as follows:, , The number of computers is as follow:, , a. Suggest the cable layout of connections between the buildings., b. Suggest the most suitable place (i.e., building) to house the server of, this school, provide a suitable reason., c. Suggest the placement of the following devices with justification., Repeater, Hub/Switch, d. The organisation also has inquiry office in another city about 100 kms, away in hilly region. Suggest the suitable transmission media to, interconnect to school and inquiry office out of the following :, Fiber optic cable, Microwave, Radiowave, , OR, Trine Tech Corporation (TTC) is a professional consultancy company. The, company is planning to set up their new offices in India with its hub at, Hyderabad. As a network adviser, you have to understand their, requirements and suggest them the best available solutions. Their queries, are mentioned as (a) to (d) below. TTC is having three blocks, namely, Human Resource Block, Conference Block and Finance Block., Distance between blocks:, Block (From), , Block (To), , Distance, , Human Resource, , Conference, , 110, , Human Resource, , Finance, , 40, , Conference, , Finance, , 80, , Also, the number of computers to be installed in each block are:, Block, , 141 | P a g e, , Computers, , Human Resource, , 25, , Finance, , 120, , Conference, , 90, , 4
Page 142 :
a. What will be the most appropriate block, where TTC should plan to, install their server?, b. Draw a block to cable layout to connect all the buildings in the most, appropriate manner for efficient communication., c. What will be the best possible connectivity out of the following, you, will suggest to connect the new setup of offices in Bangalore with its, London based office: Satellite Link, Infrared, Ethernet Cable, d. Which of the following device will be suggested by you to connect, each computer in each of the buildings: Switch, Modem, Gateway, , MARKING SCHEME (SET – 1), 1., 2., 3., 4., 5., 6., , a, b, d, b, a, select instr("Class12 CS","CS");, select right("Class12 CS",6);, 7. A HAVING clause is like a WHERE clause, but applies only to groups as a whole (that is, to the rows, in the result set representing groups), whereas the WHERE clause applies to individual rows., A query can contain both a WHERE clause and a HAVING clause. In that case: The WHERE clause, is applied first to the individual rows in the tables or table-valued objects in the Diagram pane. Only, the rows that meet the conditions in the WHERE clause are grouped. The HAVING clause is then, applied to the rows in the result set. Only the groups that meet the HAVING conditions appear in the, query output. You can apply a HAVING clause only to columns that also appear in the GROUP BY, clause or in an aggregate function., Any suitable example, 8. 77, update student set marks=0 where roll is null;, 9. select round(1905.675,-3);, select round(1905.675,1);, 10. select class,sum(marks) from myschool group by class having class=11;, update myschool set marks=marks+0.1*marks;, 11. select Area, count(*) from Salesman group by Area having count(*)>1, Select sum(sales) from Salesman, Select Sname,max(Dojoin) from Salesman, 12. Select address,max(Sales) from Salesman group by address having address=”Delhi”, Select address,max(Sales) from Salesman where address=”Delhi”, 13. 10, 9, 1024, , 14., , 142 | P a g e
Page 143 :
Static Webpage, , Dynamic Webpage, , In static web pages, Pages will remain same, until someone changes it manually., , In dynamic web pages, Content of pages are, different for different visitors., , Static Web Pages are simple in terms of, complexity., , Dynamic web pages are complicated., , Static Web Page takes less time for loading, than dynamic web page., , Dynamic web page takes more time for, loading., , Website, A website is a collection of webpages, , Webpage, A webpage is defined as a single document, or a solitary page of any website. Every, webpage is attached to a unique URL, address used to render or access that, particular page., , The website takes more time to develop than, a webpage., The website URL does not include any, extension., , The web page URL includes the extension., i.e., the path of the file., , 15. select instr(name,lname), select dayname(now()),monthname(now()),year(now());, select mod(power(3,5),5);, select lcase('I am here'),ucase('I am here');, OR, Select scod, round(Sales,1) from Salesman, Select dayname(Dojoin) from Salesman, Select instr(Sname,”a”) from Salesman, Select substr(Sname,2,3) from Salesman where name like “%t”, , 16., , Server can be placed in the ADMIN building as it has the maxium number of computer., Repeater can be placed between ADMIN and SENIOR building as the distance is more than 110 m., Also, hub/switch to be used in each building., Radiowaves can be used in hilly regions as they can travel through obstacles., 143 | P a g e
Page 144 :
OR, Finance block because it has the maximum number of computers., , Satellite link, Switch, , Sample Question Paper – 2 (Term-2), 2021, Informatics Practices (065), Class 12, Time: 02:00 Hrs, , Marks: 35, , Instructions:, 1. There are 16 questions in the question booklet., 2. Each question is compulsory., 3. The Question paper is divided into four sections - Section A containing 05 questions each, of 01 mark, Section B containing 05 questions each of 02 marks, Section C containing, 04 questions each of 03 marks, Section D containing 02 questions each of 04 marks., 4. Options are available with the questions in Section D., , 144 | P a g e
Page 145 :
SECTION - A (01 MARK QUESTIONS), QNo., 1, , Question, , Marks, , Write the output of the following command?, , 1, , select truncate(123.789,-2);, , 2, , 3, , 4, , 5, , (a) 120, , (b) 130, , (c) 123.78, , (d) 100, , Which of the following communication mediums will offer the highest, bandwidth?, (a) Optical Fibre, , (b) Shielded Twisted Pair, , (c) Unshielded Twisted Pair, , (d) Coaxial cable, , For n devices in a network, what is the number of cable links required for a, mesh topology?, (a) n*2, , (b) n*(n-1), , (c) (n-1)/2, , (d) n*(n-1)/2, , Which of the following protocols is used in real time internet based, communication?, (a) VoIP, , (b) SMTP, , (c) POP3, , (d) MIME, , If on ‘1990-01-22', it was Monday, what will be the output of following SQL, command?, select dayname('1990-01-22')+1;, , 1, , 1, , 1, , 1, , (a) Error, (b) 1, (c) 7, (d) Monday, SECTION - B (02 MARK QUESTIONS), 6, , Consider the string “ PYTHON LANGUAGE ”. Write command to display:, (a) the length of the string after trimming spaces from the beginning and, end., (b)Position of string “LA” after trimming only beginning spaces from the, string “ PYTHON LANGUAGE ”., , 145 | P a g e, , 2
Page 146 :
7, , Given a table Orders (oid, cuid, item), Radhika applies the following, command to find cuid of those customers who have two or more than two, orders., select cuid,count(*) from orders where count(*)>=2;, However, the code gives an error. Explain the reason and write correct code, to achieve the desired task., , 2, , 8, , Akash writes the following commands for a student table having attributes, roll, name, age and class., Command1: select count(*) from student, Command2: select count(age) from student., He gets the output 10 for the first command but gets an output 8 for the, second command. Explain the reason behind this difference., , 2, , 9, , Given a number n, write commands in SQL to, (a) compute cube of this number using SQL function., (b) compute remainder on division of n by another number m using SQL, function., , 2, , 10, , Anita has been given the below given orders table:, , 2, , (a) How will she generate the following output using group by and aggregate, functions wherein the count of items for cuid are arranged in descending, order?, , (b) How will she count the number of distinct items in the orders table?, SECTION - C (03 MARK QUESTIONS), , 146 | P a g e
Page 147 :
11, , A student relation is given below:, , 3, , (a) Write SQL command to display the class-wise count of students for those, classes who have more than 2 students., (b) Write an SQL command to find the average marks for class XI and class, XII students., (c) Write an SQL command to display the name and DOB of the youngest, student., 12, , Give suitable examples to explain the role of % and _ characters for pattern, matching in SQL., , 3, , 13, , Predict the output of below given SQL queries, a. select power(instr('abcd412','1'),3);, b. select substr(lower('ABC 123'),1,3), , 3, , c., , 14, , select power(instr(upper('A@123'),'1'),instr(upper('A@123'),'2'));, , Differentiate between the following, a. LAN and WAN, b. SMTP and POP3, , 3, , SECTION - D (04 MARK QUESTIONS), 15, , Write the SQL commands which will perform the following operations?, a. To display the position of space character in your name (myname)., b. To display day, month and year from today’s date., c. To compute 5 raised to the power remainder on dividing 15 by 4., d. To display the leftmost as well as the rightmost character of the string, ‘PYTHON’., OR, Consider the table Salesman with the given data, , Write SQL queries using function to perform the following operation:, a. Display maximum sales for each area., b. Display the month name from Dojoin of Salesman., c. Display those addresses which anywhere contain ‘i’., d. Display two characters from Sname starting from the first character, for those salesmen who belong to Delhi., , 147 | P a g e, , 4
Page 148 :
16, , ABC is an online corporate training provider company for IT related, courses. The company is setting up their new campus in Kolkata. You as a, network expert have to study the physical locations of various blocks and, the number of computers to be installed. In the planning phase, provide the, best possible answers for the queries (i) to (iv) raised by them., Distance between blocks:, Block (From), , Block (To), , Distance, , Administrative, , Finance, , 60, , Administrative, , Faculty studio, , 120, , Faculty studio, , 70, , Finance, , Also, the number of computers to be installed in each block are:, Block, , Computers, , Administrative, , 20, , Finance, , 40, , Faculty studio, , 120, , a. Suggest the most appropriate block, where ABC should plan to install, the server., b. Suggest the most appropriate block to block cable layout to connect, all three blocks for efficient communication., c. Which type of network out of the following is formed by connecting, the computers of these three blocks? LAN, MAN, WAN, d. Which wireless channel out of the following should be opted by ABC, to connect to students from all over the world? Infrared, Microwave,, Satellite., OR, A company XYZ Enterprises has four blocks of buildings as shown:, , Center to center distance between various blocks, , 148 | P a g e, , 4
Page 149 :
B3 TO B1, , 40 M, , B1 TO B2, , 50 M, , B2 TO B4, , 15 M, , B4 TO B3, , 150 M, , B3 TO B2, , 115 M, , B1 TO B4, , 90 M, , Number of computers in each block :, B1, , 140, , B2, , 20, , B3, , 18, , B4, , 30, , Computers in each block are networked but blocks are not networked. The, company has now decided to connect the blocks also, a. Suggest the most appropriate topology for the connections between, the blocks., b. The company wants internet accessibility in all the blocks. The, suitable and cost-effective technology for that would be ___., c. Which device will you suggest for connecting all the computers, within each of their blocks?, d. The company is planning to link its head office situated in New, Delhi with the offices in hilly areas. Suggest a way to connect it, economically:, , Marking Scheme (Set – 2), 1., 2., 3., 4., 5., 6., , d, a, d, a, b, select length(trim(" PYTHON LANGUAGE "));, select instr(ltrim(" PYTHON LANGUAGE")," ");, 7. The code gives an error because aggregate functions can not be used with where clause. The, correct code will be, select cuid,count(*) from orders group by cuid having count(*)>=2;, 8. The reason behind this difference is that the count function when applied to an attribute does not, count NULL values. The age attribute must be containing two NULL values, hence the difference., 9. select power(n,3);, select mod(n,m);, 10. select cuid,count(*) from orders group by cuid order by count(*) desc;, select count(distinct(item)) from orders;, 11. select class, count(*) from student group by class having count(*)>2, select class,avg(Marks) from student where class=’XI’ or class=’XII’ group by class, select name, max(DOB) from student, 149 | P a g e
Page 150 :
12. % and _ are used for pattern matching in SQL. While % corresponds to 0 or more characters, _, corresponds to 1 character., Consider the following customer table, custid, , name, , order, , The query select * from customer where name like ‘%a’will match those tuples, where name of the customer ends with ‘a’., The query select * from customer where name like ‘_ _ a’will match those tuples, where name of the customer is of the length three and the name ends with ‘a’., 13. 216, abc, 81, 14. LAN vs WAN, LAN, , WAN, , Local Area Network, , Wide Area Network, , Geographical speed is less., , Geographical speed is more., WAN comprises several LANs., , Its design and maintenance is easy., , Its design and maintenance is difficult., , SMTP, , POP3, , Simple Mail Transfer Protocol, , Post Office Protocol Version 3, , Used to send emails, , Used to receive emails, , The port number of SMTP is 25., , The port number of POP3 is 110., , It is implied between sender mail server and, receiver mail server., , It is implied between receiver and receiver, mail server., , 15. select instr(myname,’ ‘), select day(now()),month(now()),year(now());, select pow(5,mod(15,4));, select left('PYTHON',1),right('PYTHON',1);, OR, select area,max(sales) from Salesman group by area, select monthname(dojoin) from salesman, select(Address) from salesman where Address like ‘%i%’, select left(Sname,2) from Salesman where Address=”Delhi”, , 16., Faculty studio, Star topology, LAN, Satellite Connection, , 150 | P a g e
Page 151 :
OR, Star topology, Broadband, Switch/Hub, Radio waves, , 151 | P a g e
Page 152 :
Sample Question Paper Set - 3 (Term 2), Session 2021-22, Subject : Informatics Practices (065), Class XII, Max Time: 02:00 Hours, , Max Marks: 35, , Instructions:, 1. There are 16 questions in the question booklet., 2. Each question is compulsory., 3. The Question paper is divided into four sections - Section A containing 05 questions each, of 01 mark, Section B containing 05 questions each of 02 marks, Section C containing 04, questions each of 03 marks, Section D containing 02 questions each of 04 marks., Options are available with the questions in Section D., Section A, 1. Which of the following is not a text function:, a. TRIM(), b. TRUNCATE(), c. LEFT(), d. MID(), , 1, , 2. Which of the following is not a date function:, a. Month, b. Year, c. NOW, d. POW, , 1, , 3. Central computer which is powerfull than other computers is called as:, a. Client, b. Server, c. HUB, d. Switch, , 1, , 4. The device that can operate in place of a HUB is a :, a. Switch, b. Bridge, c. Router, d. Gateway, 5. The combination of bus and star topology is called a:, a. Hybrid, b. Mesh, c. Tree, d. Ring, , 152 | P a g e, , 1, , 1
Page 153 :
Section - B, , 6. Differentiate between Degree and Cardinality with example., , 2, , 7. Consider the given table and answer the questions:, , 2, , a. Identify the attribute best suitable to be declared as a primary key,, b. Insert the following data into the attributes ItemNo, ItemName and SCode respectively in the, given table STORE., ItemNo = 2010, ItemName = “Note Book” and Scode = 25, 8. Consider the given table and find the output of the given queries:, , 2, , (i) SELECT Department, count(*) FROM Teacher GROUP BY Department;, (ii)SELECT Max(Date_of_Join),Min(Date_of_Join) FROM Teacher;, , 9. Write short note on Primary and Foreign key with example., 10. Differentiate between order by and group by clause with example., , 153 | P a g e, , 2, 2
Page 154 :
Section C, 11. Write short notes on the following constraints, a. Unique, b. Distinct, c. Where clause, , 3, , 12. Consider the following table and answer the questions from i to iii, , (i), (ii), (iii), , 3, , List the details of mobile whose name starts with „S‟ or ends with „a‟,, Display the Mobile supplier & quantity of all mobiles except „MB003‟,, List showing the name of mobile company having price between 3000 & 5000,, , 13. Write the commands for the following:, , 3, , a. To remove the table named “Store” from the database., b. To add one more column to the table with column name abc, datatypr varchar and size 10., c. To arrange the values of the table according to the abc column in ascending order in output., 14. What is website? Differentiate between static and dynamic pages., , 154 | P a g e, , 3
Page 155 :
Section D, , 15. Write the SQL functions which will perform the following operations:, 4, i) To display the name of the month of the current date ., ii) To remove spaces from the beginning and end of a string, “ Panorama “., iii) To display the name of the day eg, Friday or Sunday from your date of birth, dob., iv) To display the starting position of your first name(fname) from your whole name (name)., OR, Consider a table SALESMAN with the following data:, , Write SQL queries using SQL functions to perform the following operations:, a) Display salesman name and bonus after rounding off to zero decimal places., b) Display the position of occurrence of the string “ta” in salesman names., c) Display the four characters from salesman name starting from second character., d) Display the month name for the date of join of salesman, 16. A company in Mega Enterprises has 4 wings of buildings as shown in the diagram, , Center to center distances between various Buildings:, W3 to W1 - 50m, W1 to W2 - 60m, W2 to W4 - 25m, W4 to W3 - 170m, W3 to W2 - 125m, W1 to w4 - 90m, 155 | P a g e, , 4
Page 156 :
Number of computers in each of the wing:, W1 - 150, W2 - 15, W3 - 15, W4 - 25, Computers in each wing are networked but wings are not networked The company has now decided to, connect the wings also., i.Suggest a most suitable cable layout for the above connections., ii. Suggest the most appropriate topology of the connection between the wings., iii. The company wants internet accessibility in all the wings. Suggest a suitable, technology ., iv. Suggest the placement of the following devices with justification if the company wants, minimized network traffic a)Repeater b)Hub / switch, , OR, The Virtual Connects organization has set up its new centre at Noida for its office and webbased activities. It has 4 blocks of buildings as shown in the diagram below:, , (i) Suggest the most suitable place (the Block) to install the server of this organization with a, suitable reason., (ii) Which device will you suggest to be placed/installed in each of these blocks to efficiently, connect all the computers within these blocks?, (iii) Suggest the placement of a Repeater in the network with justification., (iv) The organization is planning to link its office to an office in the hilly areas. Suggest a wayto connect it, economically. Justify your answer., , ************__________************, , 156 | P a g e
Page 157 :
157 | P a g e
Page 158 :
MARKING SCHEME (SET – 3), 1. b, 2. d, 3. b, 4. a, 5. c, 6. Degree: Number of columns in a table, Cardinality : Number of rows in a table.With suitable, example., 7. a. ItemNo, b. INSERT INTO store (ItemNo,ItemName,Scode) VALUES(2010,, , “Note Book”,25);, , 8. Answers:, , 9. Definition of Primary and Foreign key with example., 10. Differece between order by and group by clause with example., 11. Definition of all 3 clauses, 12. (i) SELECT * FROM MobileMaster WHERE M_Name LIKE “S%”;, (ii) SELECT M_Supplier, M_Qty FROM MobileStock WHERE M_Id<>MB003”;, (iii)SELECT M_Company FROM MobileMaster WHERE M_Price BETWEEN 3000 AND 5000;, 13. (i)Drop table store;, (ii)Alter table store add column (abc varchar (10));, (iii)Select * from store order by abc;, 14. Website: Collection of interrelated web pages, Static web page: Which has a fixed content and thus it gets delivered to user’s browser exactly as, created., Dynamic Web page: Which displays different content every time it is loaded., 15. i) monthname(date(now())), ii) trim(“ Panaroma “), iii) dayname(date(dob)), iv)instr(name, fname), , 158 | P a g e
Page 159 :
OR, , (i) Select sname, round(bonus,0) from Salesman;, (ii) Select instr(Sname, “ta”) from Salesman;, iii) Select mid(Sname,2,4) from Salesman;, alternative answer, iii) Select Substring(Sname,2,4) from Salesman;, iv) Select monthname(DateofJoin) from Salesman;, , 16., , Ans. Most suitable layout according to distance is, , ii. Star Topology, iii Broadband, iv. a. Not required., Repeaters may be skipped as per above layout (because distance is less than 100 m), b. In every wing (switch), OR, (i) The most suitable place to install the server is Block C as this place has maximum number of, computers., (ii)Switch, (iii) Repeater may be placed when the distance between 2 buildings is more than 70 metres, i.e.,, Block B to Block C, Block A to Block D, Block B to Block D, (iv) Radio waves, because these waves are easy to generate, can travel long distances and can, penetrate mountains easily., , 159 | P a g e
 Learn better on this topic
Learn better on this topic