Notes of S.E B.Tech(CSE), Discrete Mathematics BTechComp .pdf - Study Material
Page 1 :
Course Structure and Syllabus, For, , B. Tech Programme, (With effect from the Academic Year 2017-2018), , Department of Computer Engineering, DR. BABASAHEB AMBEDKAR TECHNOLOGICAL, UNIVERSITY, MAHARASHTRA (INDIA).
Page 2 :
Department of Computer Engineering, Dr. Babasaheb Ambedkar Technological University, Lonere 402 103, Programme Educational Objectives, Name of Programme: Bachelor of Technology (Computer Engineering), A graduate in the discipline of Computer Engineering is generally expected to have three kinds of, knowledge. First, the graduate should have conceptual knowledge of the core topics of Computer, Science. Second, she/he should have knowledge of mathematical formalism underlying various, programming concepts. Third, graduates in the discipline of Computer Engineering should have the, knowledge of the state of the technologies and tools so that he/she can apply the principles of Computer, Science to solve real-life problems from diverse application domains. The programme of B. Tech. in, Computer Engineering at Dr. Babasaheb Ambedkar Technological University (DBTAU) essentially, aims to meet these broad expectations. At the same time, the program intends to comply with the, courses and syllabus available at National Program on Technology Enhanced Learning (NPTEL)., The following specific educational objectives aims to achieve these global and regional expectations., , Objective, Identifier, , Objectives, , PEO1, , To provide knowledge of sound mathematical principles underlying various programming, concepts., , PEO2, , To develop an ability to understand complex issues in the analysis, design, implementation, and operation of information systems., , PEO3, , To provide knowledge of mechanisms for building large-scale computer-based systems., , PEO4, , To develop an ability to provide computer-based solutions to the problems from other, disciplines of science and engineering., , PEO5, , To impart skills necessary for adapting rapid changes taking place in the field of information, and communication technologies., , PEO6, , To provide knowledge of ethical issues arising due to deployment of information and, communication technologies in the society on large scale., , 2
Page 3 :
Programme Outcomes, After undergoing the learning process of four years, students of B. Tech. (Computer Engineering) at, Dr. Babasaheb Ambedkar Technological University will have an ability to build information systems, and provide computer based solutions to real life problems. The graduates of this programme will, demonstrate following abilities and skill sets., , Outcome, Identifier, , Outcomes, , PO1, , The graduates will possess the knowledge of various discrete mathematical structures,, Logic and numerical techniques., , PO2, , The graduates will have an ability to apply mathematical formalism of Finite Automata, and Probability in modeling and analysis of systems., , PO3, , The graduates will have knowledge of core programming paradigms such as database, orientation, object orientation, and agent orientation and concepts essential to implement, software based system., , PO4, , The graduates will have an ability to analyze problem, specify algorithmic solutions to, them and to evaluate alternative solutions., , PO5, , The graduate will have broad understanding of the impact of a computer based solutions in, economic, environmental and social context and will demonstrate use of analytical tools in, gathering requirements and distilling relevant information to provide computer based, solutions., , PO6, , The graduates will demonstrate the ability to build human centric interfaces to computers., , PO7, , The graduates will posses the knowledge of advanced and emerging topics in the fields of, operating systems, databases and computer networks., , PO8, , The graduates will posses skills necessary to communicate design engineering ideas. The, skills set include verbal, written and listening skills., , PO9, , The graduates will understand ethical issues in providing computer based solutions also, they will have an ability and attitude to address the ethical issues., , PO10, , The graduates will understand the role of system software such as operating systems,, database management systems, compilers, middle-ware and internet protocols in realizing, distributed information environment, , 3
Page 4 :
ABET's Criteria for Accreditating Engineering Programmes, (a) An ability to apply knowledge of mathematics, science and engineering., (b) An ability to design and conduct experiments as well as to analyze and interpret data., (c) An ability to design a system, a component, or process, to meet desired needs within realistic, constraints such as economic, environmental, social, political, ethical, health and safety,, manufacturability, and sustainability., (d) An ability to function on multidisciplinary teams., (e) An ability to identify, formulate and solve engineering problems., (f) An understanding of professional and ethical responsibility., (g) An ability to communicate effectively., (h) The broad education necessary to understand the impact of engineering solutions in a global,, economical, environmental and social context., (i) A recognition of the need for and an ability to engage in life-long learning., (j) A knowledge of contemporary issues, and, (k) An ability to use the techniques, skills, and modern engineering tools necessary for engineering, practice., Mapping of Programme Outcomes with ABET's Criteria, a, PO1, , x, , PO2, , x, , PO3, , b, , c, , e, , f, , g, , h, , i, , j, , k, , x, x, , x, , PO4, , x, , PO5, , x, , PO6, , d, , x, x, x, , PO7, , x, , PO8, , x, , PO9, , x, , PO10, , x, , 4
Page 5 :
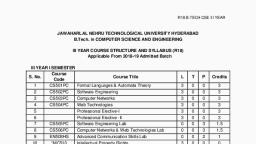
Second Year B. Tech. (Computer Engineering), No., , Course Type Code, , Course Name, , L, , T, , P, , CR, , Semester Third, 1, , Core, , CE301, , Digital Circuits, , 3, , 1, , 4, , 2, , Core, , CE302, , Discrete Mathematics, , 3, , 1, , 4, , 3, , Core, , CE303, , Computer Architecture and Organization, , 3, , 3, , 4, , Humanities, , CE304, , Basic Human Rights, , 3, , 3, , 5, , DSE, , CE305, , Elective 301, 1. Object-Oriented Programming in C++, 2. Object-Oriented Programming in Java, , 3, , 3, , 6, , Mathematical CE306, , Numerical Methods, , 3, , 3, , 7, , Lab Course, , CE307, , Digital Circuits Laboratory, , 2, , 1, , 8, , Lab Course, , CE308, , Object-Oriented Programming Laboratory, , 2, , 1, , 9, , SEC, , CE309, , Web Page Design (HTML), , 2, , 3, , 1, , Total Credits 25, Semester Fourth, 1, , Core, , CE401, , Data Communications, , 3, , 1, , 4, , 2, , Core, , CE402, , Data Structures, , 3, , 1, , 4, , 3, , Core, , CE403, , Operating Systems, , 3, , 1, , 4, , 4, , GE, , CE404, , Elective 401, 1. Micro-Processors, 2. Any Course offered by other Departments, in IV Sem., , 3, , 3, , 5, , GE (Math), , CE405, , Elective 402, 1. Probability, Statistics, and Queueing, Theory, 2. Engineering Mathematics – III, , 3, , 3, , 6, , Lab Course, , CE406, , Data Structure Laboratory, , 4, , 2, , 7, , Lab Course, , CE407, , Operating System Laboratory, , 2, , 1, , 8, , SEC, , CE408, , Web Application Development (JSP, PHP, J2EE), , 1, , 2, , 2, , 9, , SEC, , CE409, , Python Programming, , 1, , 2, , 2, , Total Credits 25, , 5
Page 6 :
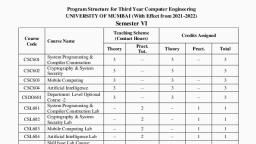
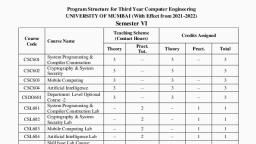
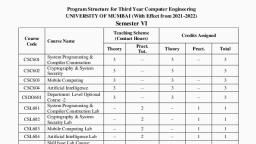
Third Year B. Tech. (Computer Engineering), No., , Course Type, , Code, , Course Name, , L, , T, , P, , CR, , Semester Fifth, 1, , Core, , CE501, , Database Management System, , 3, , 1, , 4, , 2, , Core, , CE502, , Design and Analysis of Algorithms, , 3, , 1, , 4, , 3, , Core, , CE503, , Theory of Computations, , 3, , 1, , 4, , 4, , DSE, , CE504, , Elective 501, 1. Object Oriented Analysis and Design, 2. Introduction to Data Analytics, 3. Digital Image Processing, , 3, , 3, , 5, , GE, CE505, (Humanities), , Elective 502, 1. Management Sciences, 2. Development Engineering, 3. National Service Scheme – I (NSS – I), , 3, , 3, , 6, , Lab Course, , CE506, , Database Management System Laboratory, , 2, , 1, , 7, , Lab Course, , CE507, , Design & Analysis of Algorithm Laboratory, , 4, , 2, , 8, , SEC, , CE508, , Smart Phones Application Development, , 2, , 2, , 9, , AECC, , CE509, , Seminar, , 4, , 2, , 1, , Total Credits 25, Semester Sixth, 1, , Core, , CE601, , Compiler Construction, , 3, , 1, , 4, , 2, , Core, , CE602, , Computer Networks, , 3, , 1, , 4, , 3, , DSE, , CE603, , Elective 601, 1. Computer Graphics, 2. Database Implementation Techniques, , 3, , 3, , 4, , DSE, , CE604, , Elective 602, 1. Human Computer Interaction, 2. Real Time System, , 3, , 3, , 5, , DSE, , CE605, , Elective 603, 1. Bio-Metrics, 2. Operating System Design, , 3, , 3, , 6, , Lab Course, , CE606, , Computer Networks Laboratory, , 2, , 1, , 7, , Lab Course, , CE607, , Compiler Construction Laboratory, , 2, , 1, , 8, , SEC, , CE608, , System Administration, , 2, , 2, , 9, , SEC, , CE609, , MOOC (Self Study Course), , 4, , 2, , 10, , AECC, , CE610, , Industrial Training, , 4, , 2, , 6, , 1
Page 7 :
Total Credits 25, Fourth Year of B. Tech. (Computer Engineering), No., , Course Type Code, , Course Name, , L, , T, , P, , CR, , Semester Seventh, 1, , Core, , CE701, , Software Engineering, , 3, , 3, , 2, , Core, , CE702, , Artificial Intelligence, , 3, , 3, , 3, , Core, , CE703, , Inter-Networking Protocols, , 3, , 3, , 4, , DSE, , CE704, , Elective 701, 1. Distributed System, 2. Cloud Computing, , 3, , 3, , 5, , DSE, , CE705, , Elective 702, 1. Computer Vision, 2. Natural Language Processing, , 3, , 3, , Lab Course CE706, , Inter Networking Protocol Laboratory, , 4, , 2, , 6, , Lab Course CE707, , Software Engineering Laboratory, , 2, , 1, , 7, , Lab Course CE708, , Artificial Intelligence Laboratory, , 2, , 1, , 8, , Lab Course CE709, , Project Phase I, , 4, , 4, , 9, , SEC, , Hadoop Platform Development, , 2, , 2, , CE7, , 1, , Total Credits 25, Eight Semester, 1, , DSE, , CE801, , Elective-801, 1. Software Quality Assurance, 2. Software Architecture, , 3, , 3, , 2, , DSE, , CE802, , Elective 802, 1. Data Science with R, 2. Cryptography and Network Security, , 3, , 3, , 3, , DSE, , CE803, , Elective-803, 1. Bio-Informatics, 2. Internet of Things (IoT), 3. Cyber Law, , 3, , 3, , 4, , GE, , CE804, , Elective 804, 1. Principles of Management, 2. Business Intelligence, 3. National Service Scheme – II (NSS-II), , 3, , 3, , 5, , AECC, , CE806, , Project Phase II, , 6, , SEC, , CE807, , Continuous Integration, , 2, , Total Credits 22, 7, , 1, , 6, , 8, , 2, , 2
Page 10 :
Mapping with NPTEL Courses, Course at DBATU, , NPTEL Course and Link, , Course Instructor, , Semester VII, Software Engineering, , Software Enginneing (Video), Software Engineering (Web), , Prof. R. K. Joshi, IIT Bombay, Prof. Rajib Mall, IIT Kharagpur, , Artificial Intelligence, , Artificial Intelligence (Video), Artificial Intelligence (Web), , Prof. Deepak Khemani, IIT Madras, Prof. S. Sarkar,, Prof. P. Mitra, IIT Kharagpur, , Inter Networking Protocols, , Not Available, , Not Available, , Distributed System, , Distributed Computing Systems Prof. Ananthanarayana V. S, NITK, (Web), , Cloud Computing, , Not Available, , Not Available, , Computer Vision, , Not Available, , Not Available, , Natural Language Processing, , Natural Language Processing, (Video), , Prof. Pushpak Bhattacharyya, IIT Bombay, , Hadoop Platform, Development, , Not Available, , Not Available, Semester VIII, , Software Quality Assurance, , Software Testing, , Prof. Rajib Mall, IIT Kharagpur, , Software Architecture, , Software Architecture Design, (Video), Software Enginneing (Video), , Dr. Bedir Tekinerdoğan, Prof. R. K. Joshi, IIT Bombay, , Data Science with R, , Introductory Data Science using David Langer, R (Video), , Cryptography and Network, Security, , Cryptography and Network, Security (Video), , Dr. Debdeep Mukhopadhyay, IIT Kharagpur, , Bio-Informatics, , Not Available, , Not Available, , Internet of Things, , Not Available, , Not Available, , IBM Watson/Bluemix, , Not Available, , Not Available, , Principles of Management, , Not Available, , Not Available, , National Service Scheme – II, , Not Available, , Not Available, , Business Intelligence, , Not Available, , Not Available, , 10
Page 11 :
CE301 Digital Circuits, Course Objectives and Outcomes:, • [DCCO1] Perform the conversion among different number systems., • [DCCO2] Design digital components including – decoders, multiplexers, arithmetic circuits., • [DCCO3] Design of synchronous sequential circuits., • [DCCO4] Describe design methodology for different combinational logic circuit., • [DCCO5] Analyze digital systems and improve the performance by reducing complexities., • [DCCO6] Test digital systems and analyze faults., CO to PO Mapping:, PO1, DCCO1, , PO2, , PO3, , PO4, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , DCCO2, , x, , DCCO3, , x, , DCCO4, , x, , x, , DCCO5, , x, , x, , DCCO6, , PO5, , x, , x, , Unit I, Number Systems and Codes: Binary number system, Signed binary numbers, Binary arithmetic,, Decimal number system, Hexadecimal number system, Octal number system, Arithmetic operations, using 1’s complement, 2’s complement, 9’s complement, 10’s complement. Codes: Numeric codes,, Weighted and non-weighted codes, Sequential codes, Self complimenting codes, Cyclic codes,, Reflective codes, BCD code, Excess-3 code, Gray code, Error detecting and correcting codes., Unit II, Boolean Algebra and Logic Functions: Introduction to analog and digital signal, Logic gates and, switching functions: AND, OR, NOT, EX-OR, EX-NOR, NAND, NOR. Implementation of universal, gates using logic gates, De Morgan’s theorem, Boolean algebra, Representation of logic functions using, POS and SOP form, Minimization of completely and incompletely specified switching functions, Karnaugh map (2,3,4,5,6 variable)., Unit III, Combinational Circuits Design: Quine – McCluskey method, TTL and CMOS logic families, Half, and full adder, Half and full subtractor, Binary parallel adder, Binary parallel subtractor, Look ahead, carry header, BCD to 7-segment decoder, Binary to Gray code converter, Gray to Binary code, converter., 11
Page 12 :
Unit IV, Combinational Logic Design using MSI Circuits: Multiplexer, Demultiplexer, BCD arithmetic: BCD, adder, BCD subtractor, Arithmetic logic unit, Digital comparators, Parity generators. Design of PAL,, Design of PLA, Design of PROM., Unit V, Designing with Sequential MSIs: Comparison between sequential and combinational circuit,, Synchronous sequential circuits and asynchronous sequential circuits, Registers, Shift registers,, Counters: asynchronous counters and synchronous counters, Sequential circuit’s implementation. Flip, flops: Edge triggered flip-flops, S-R flip flop, J-K flip flop, T flip flop, D flip flop., conversion., Unit VI, Finite State Machines and ASM Charts: Regular expressions using FSM, Optimization using FSM,, Reduction of states, Mealy and Moore machine. Representation of sequential circuits using ASM, charts, Synthesis of output and next state functions, Data path and control path, Partition-based design., Text Books:, 1. R. P. Jain, Modern Digital Electronics, 3rd Edition, McGraw-Hill Publication, 2003., 2. Zvi Kohavi, Switching and Finite Automata Theory, 2nd Edition, McGraw-Hill Publication,, 2001., 3. M. Morris Mano, Digital Design, 3rd Edition, Prentice Hall Publication, 2001., Reference Books:, 1. F. J. Gill Peterson, Switching Theory and Logic Design, John Wiley Publication., 2. Samuel C. Lee, Digital Circuits and Logic Design, PHI Publication., 3. V. Rajaraman, T. Radhakrishnan, An Introduction to Digital Computer Design, McGraw-Hill, Publication., 4. Hatchell and Gray, Logic Synthesis and Verification Algorithms, Kluwer Academic Publication., 5. A. Anandkumar, Switching Theory and Logic Design, PHI Learning, 2008., , 12
Page 13 :
CE302 Discrete Mathematics, Course Objectives and Outcomes:, • [DMCO1] Understand sets, relations, functions and discrete structures. Apply Propositional, logic and First order logic to solve problems., • [DMCO2] Express and solve number theoretic problems using algebraic properties of groups,, rings and fields., • [DMCO3] To design and develop real time application using graph theory., • [DMCO4] Students would be able to model and analyze computational processes using analytic, and combinatorial methods., • [DMCO5] Students will be able to use the methods learnt as part of this subject in subsequent, courses in the design and analysis of algorithms, theory of computation, and compilers., • [DMCO6] Develop a discrete model for a given computational problem and solve., CO to PO Mapping:, PO1, , PO2, , DMCO1, , x, , x, , DMCO2, , x, , DMCO5, DMCO6, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , DMCO3, DMCO4, , PO3, , x, , x, x, x, , x, , Unit I, Fundamental Structures and Basic Logic: Sets, Venn diagram, Cartesian product, Power sets,, Cardinality and countability, Propositional logic, Logical connectives, Truth tables, Normal forms,, Validity, Predicate logic, Limitations of predicate logic, Universal and existential quantification, First, order logic., Unit II, Functions and Relations: Subjective, Injective, Bijective and inverse functions, Composition of, function, Reflexivity, Symmetry, Transitivity and equivalence relations., Unit III, Combinatorics: Counting, Recurrence relations, generating functions., Unit V, Graph Theory: Basic terminology, Multi graphs and weighted graphs, Paths and circuits, Shortest path, problems, Euler and Hamiltonian paths, Representation of graph, Isomorphic graphs, Planar graphs,, Connectivity, Matching Coloring., 13
Page 14 :
Unit IV, Trees: Rooted trees, Path length in rooted tree, Binary search trees, Spanning trees and cut set,, Minimal spanning trees, Kruskal’s and Prim’s algorithms for minimal spanning tree., Unit VI, Algebraic Systems: Algebraic systems, Groups, Semi group, Monoid, Subgroup, Isomorphism and, homomorphism, Rings and fields, Lattices, Boolean lattices and Boolean algebra., Text Books:, 1. C. L. Liu, Elements of Discrete Mathematics, 3rd Edition, McGraw-Hill Publication, 2008., 2. Kenneth H. Rosen, Discrete Mathematics and its Applications, 6th Edition, McGraw-Hill, Publication, 2010., 3. Y. N. Singh, Discrete Mathematical Structures, Wiley Publication., 4. Dr. Sukhendu Dey, Graph Theory with Applications, SPD Publication., Reference Books:, 1. Lipschutz Lipson, Discrete Mathematics, 3rd Edition, McGraw Hill Publication, 2009., 2. V. K. Balakrishnan, Schaum's Outline Of Graph Theory, 1st Edition, McGraw Hill Publication., 3. Eric Gossett, Discrete Mathematics with Proof, 2nd Edition, Wiley Publication., , 14
Page 15 :
CE303 Computer Architecture and Organization, Course Objectives and Outcomes:, • [CACO1] To understand the basic hardware and software issues of computer organization., • [CACO2] Identify functional units, bus structure and addressing modes., • [CACO3] Students will be able to identify where, when and how enhancements of computer, performance can be accomplished., • [CACO4] Students will also be introduced to more recent applications of computer organization, in advanced digital systems., • [CACO5] Identify memory hierarchy and performance., CO to PO Mapping:, PO1, CACO1, CACO2, , PO2, , PO3, , PO4, , PO5, , PO7, , PO8, , PO9, , PO10, , x, x, x, , CACO3, , x, , x, , CACO4, CACO5, , PO6, , x, , Unit I, Introduction: Concept of computer organization and architecture, Fundamental unit, Computer, function and interconnection, CPU structure and function., Unit II, Instruction Sets: Characteristics, Types of operands, Types of operations, Assembly language,, Addressing modes, Instruction format, Types of instruction, Instruction execution, Machine state and, processor status, Structure of program, Introduction to RISC and CISC architecture., Unit III, Computer Arithmetic: The arithmetic and logic Unit, Integer representation, Integer arithmetic,, Floating point representation, Floating point arithmetic, Introduction of arithmetic co-processor., Unit IV, Memory Organization: Internal Memory: Semiconductor main memory, Error correction, Advanced, DRAM organization, Virtual memory systems and cache memory systems. External Memory:, Organization and characteristics of magnetic disk, Magnetic tape, Optical memory, RAID, Memory, controllers., Unit V, Control Unit: Control unit operation: Micro-operations, Control of the processor, Hardwired, implementation, Micro-programmed Control Unit, Basic concepts, Micro-instruction sequencing,, 15
Page 16 :
Micro-instruction execution, Applications of micro-programming., Unit VI, Input/ Output Organization: External devices, I/O module, Programmed I/O, Interrupt driven I/O,, Direct memory access, I/O channels and processors, External interface., Instruction pipe-lining: Concepts. Parallel processing: Multiple processor organization, Symmetric, multiprocessor, Cache coherence and the MESI protocol., Text Books:, 1. William Stalling, Computer Organization and Architecture: Designing for Performance, 8th, Edition, Prentice Hall Publication, 2009., 2. Hayes, Computer Architecture and Organization, 3rd Edition, McGraw-Hill Publication., 3. Zaky, Computer Organization, 5th Edition, McGraw-Hill Publication., Reference Books:, 1. Hennessy and Patterson, Computer Architecture: A Quantitative Approach, 4th Edition, Morgan, and Kaufman Publication, 2007., 2. Morris Mano, Computer Architecture and Organization, PHI Publication., 3. Mostafa Abd-El-Barr, Hesham El-Rewini, Fundamentals of Computer Organization and, Architecture, Wiley Publication., 4. Miles J. Murdocca, Vincent P. Heuring, Computer Architecture and Organization: An, Integrated Approach, Wiley Publication., 5. Sajjan G. Shiva, Computer Organization, Design, and Architecture, CRC Press., , 16
Page 17 :
CE304 Basic Human Rights, Course Objectives and Outcomes:, • [BHCO1] Be familiar with the major universal and regional systems of human rights law, their, relationships to each other, and the legal value and authority of declarations, decisions,, judgments and other materials generated by them., • [BHCO2] Develop an awareness of the primary areas of concern within the field of human, rights law and other relevant branches of law, and the ways in which human rights are promoted, and protected., CO to PO Mapping:, PO1, , PO2, , PO3, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , BHCO1, x, , BHCO2, , Unit I, The Basic Concepts, Individual, group, civil society, state, equality, justice, Human Values: - Humanity, virtues, compassion., Unit II, Human rights and Human Duties, Origin, civil and political rights, Contribution of American bill of rights, French revolution, Declaration, of independence, Rights of citizen, Rights of working and exploited people, Fundamental rights and, economic program, India’s charter of freedom., Unit III, Society, religion, culture, and their inter-relationship, Impact of social structure on human behavior, Roll of socialization in human values, Science and, Technology, modernization, globalization, and dehumanization., Unit IV, Social Structure and Social Problems, Social and communal conflicts and social harmony, rural poverty, unemployment, bonded labour,, Migrant workers and human rights violations, human rights of mentally and physically challenged., Unit V, State, Individual liberty, Freedom and Democracy, The changing of state with special reference to developing countries, Concept of development under, development and social action, need for collective action in developing societies and methods of social, action, NGOs and human rights in India: - Land, Water, Forest issues., , 17
Page 18 :
Unit VI, Human Rights in Indian Constitution and Law, The constitution of India:, (i) Preamble, (ii) Fundamental rights., (iii) Directive principles of state policy., (iv) Fundamental duties., (v) Some other provisions., Universal declaration of human rights and provisions of India, Constitution and law, National human, rights commission and state human rights commission., Text Books:, 1. Shastry, T. S. N., India and Human rights: Reflections, Concept Publishing Company India Pvt., Ltd., 2005., 2. Nirmal, C.J., Human Rights in India: Historical, Social and Political Perspectives (Law in, India), Oxford India., , 18
Page 19 :
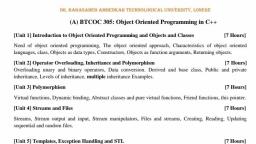
CE305 Object-Oriented Programming using C++ (Elective 301), Course Objectives and Outcomes:, • [OCCO1] Appreciation and understanding of object oriented concepts and their utility., • [OCCO2] Apply Object oriented approach to design software., • [OCCO3] Ability to formulate the problem, come up with object oriented design., • [OCCO4] Practicing use of different features of Object Oriented Methodology like templates,, exception handling, reflection etc., • [OCCO5] Study different systems and apply different design methodologies based on the, problem specification and objectives., CO to PO Mapping:, PO1, OCCO1, , x, , PO2, , PO3, , PO4, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , OCCO2, x, , OCCO3, OCCO4, OCCO5, , PO5, , x, , x, , x, , x, , x, , x, , Unit I, Introduction to Object Oriented Programming and Objects and Classes: Need of object oriented, programming, The object oriented approach, Characteristics of object oriented languages. A class,, Objects as data types, Constructors, Objects as function arguments, Returning objects., Unit II, Operator Overloading and Inheritance:. Overloading unary and binary operators, Data conversion., Derived and base class, Public and private inheritance, Levels of inheritance, Multiple inheritance, Examples., Unit III, Polymorphism: Virtual functions, Dynamic binding, Abstract classes and pure virtual functions,, Friend functions, The this pointer., Unit IV, Streams and Files: Streams, Stream output and input, Stream manipulators, Files and streams,, Creating, Reading, Updating sequential and random files., Unit V, Templates and Exception Handling: Function templates, Overloading function templates, Class, templates, Exception handling overview, Need of exceptions, An exception example, Multiple, 19
Page 20 :
exceptions, Exception specifications., Unit VI, Standard Template Library (STL): Introduction to STL- Containers, Iterators, Algorithms, Sequence, containers, Associative containers, Container adapters., Text Books:, 1. E. Balagurusamy, Object Oriented Programming with C++, McGraw-Hill Publication., 2. Robert Lafore, Object Oriented Programming in C++, Sams Publishing., 3. Dr. B. B. Meshram, Object Oriented Paradigms with C++ Beginners Guide for C and C++,, SPD Publication., 4. Rajesh R. Shukla, Object-Oriented Programming in C++, Wiley India Publication., Reference Books:, 1. P. J. Deitel, H. M. Deitel, C++ How to Program, PHI Publication., 2. John Hubbard, Programming with C++, Schaum’s outlines, McGraw-Hill Publication., 3. Nicolai M. Josuttis, Object-Oriented Programming in C++, Wiley Publication., , 20
Page 21 :
CE305 Object-Oriented Programming using Java (Elective 301), Course Objectives and Outcomes:, • [OJCO1] Appreciation and understanding of object oriented concepts and their utility., • [OJCO2] Apply Object oriented approach to design software., • [OJCO3] Ability to formulate the problem, come up with object oriented design., • [OJCO4] Practicing use of different features of Object Oriented Methodology like templates,, exception handling, reflection etc., • [OJCO5] Study different systems and apply different design methodologies based on the, problem specification and objectives., CO to PO Mapping:, PO1, OJCO1, , x, , PO2, , PO3, , PO4, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , OJCO2, x, , OJCO3, OJCO4, OJCO5, , PO5, , x, , x, , x, , x, , x, , x, , Unit I, Introduction to Computers and Java: Introduction, Computers: Hardware and Software, Data, Hierarchy, Computer Organization, Machine Languages, Assembly Languages and High-Level, Languages, Introduction to Object Technology, Operating Systems, Programming Languages, Java and, a Typical Java Development Environment, Your First Program in Java: Printing a Line of Text,, Modifying Your First Java Program, Displaying Text with printf, Another Application: Adding Integers,, Memory Concepts, Arithmetic, Decision Making: Equality and Relational Operators., Unit II, Introduction to Classes, Objects, Methods and Strings: Introduction, Declaring a Class with a, Method and Instantiating an Object of a Class, Declaring a Method with a Parameter, Instance, Variables, set Methods and get Methods, Primitive Types vs. Reference Types, Initializing Objects with, Constructors Floating-Point Numbers and Type double., Unit III, Control Statements: Introduction, Algorithms, Pseudocode, Control Structures, if Single-Selection, Statement, if...else Double-Selection Statement, while Repetition Statement, Formulating Algorithms:, Counter-Controlled Repetition, Formulating Algorithms: Sentinel-Controlled Repetition, Formulating, Algorithms: Nested Control Statements, Compound Assignment Operators, Increment and Decrement, Operators, Primitive Types, Essentials of Counter-Controlled Repetition, for Repetition Statement,, Examples Using the for Statement, do...while Repetition Statement, switch Multiple-Selection, 21
Page 22 :
Statement, break and continue Statements, Logical Operators., Unit IV, Array: Introduction, Declaring and Creating Arrays, Examples Using Arrays, Case Study: Card, Shuffling and Dealing Simulation, Enhanced for Statement, Passing Arrays to Methods, Case Study:, Class GradeBook Using an Array to Store Grades, Multidimensional Arrays, ase Study: Class, GradeBook Using a Two-Dimensional Array, Variable-Length Argument Lists, Using Command-Line, Arguments, Class Arrays., Unit V, Classes and Objects: Introduction, Controlling Access to Members, Referring to the Current Object’s, Members with the this Reference, Time Class Case Study: Overloaded Constructors, Time, Default and, No-Argument Constructors, Notes on Set and Get Methods, Composition, Enumerations, Garbage, Collection and Method finalize, static Class Members, static Import, final Instance Variables, Time, Class Case Study: Creating Packages, Package Access., Unit VI, Inheritance: Introduction, Superclasses and Subclasses, protected Members, Relationship between, Superclasses and Subclasses, Hierarchy Using private Instance Variables, Constructors in Subclasses, Software Engineering with Inheritance, Class Object., Polymorphism: Introduction, Polymorphism Examples, Demonstrating Polymorphic Behavior,, Abstract Classes and Methods, Case Study: Payroll System Using Polymorphism, final Methods and, Classes, Case Study: Creating and Using Interfaces., Reference Book:, 1. Java: How to Program, 9th Edition, Paul Deitel and Harvey Detail, Pearson's Publication., 2. Joel Murach and Michael Urban, Murach’s Beginning Java with Eclipse, Murach's, Publication., 3. Doug Lowe, Java All-in-One For Dummies, 4th Edition, Wiley Publication., 4. Herbert Schildt, Java The Complete Reference, 8th Edition, McGraw-Hill Publication., 5. Patrick Niemeyer, Daniel Leuck, Learning Java, 4th Edition A Bestselling Hands-On Java, Tutorial, O'Reilly Media., , 22
Page 23 :
CE306 Numerical Methods, Course Objectives and Outcomes:, • [NMCO1] Determine an interpolating function for data., • [NMCO2] Solve initial value problems., • [NMCO3] aware of the use of numerical methods in modern scientific computing., • [NMCO4] Students would be able to assess the approximation techniques to formulate and, apply appropriate strategy to solve real world problems., CO to PO Mapping:, PO1, , PO2, x, , NMCO1, , PO3, , PO4, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , NMCO2, , x, , x, , NMCO3, , x, , x, , x, , x, , x, , NMCO4, , PO5, , x, , Unit I, Solution of Algebraic and Transcendental Equation: Bisection method, Method of false position,, Newton’s method and Newton-Raphson method, Approximate solution of equation – Horner’s method., Unit II, Solution of Linear Simultaneous Equation: Gauss elimination method, Gauss-Jordan method,, Crout's triangular method, Iterative method of solution- Jacobi iteration method, Gauss-Seidal iteration, method, Relaxation method., Unit III, Finite Differences: Forward difference operator, Backward difference operator, Central difference, operator, Newton’s interpolation formula, Newton’s forward–backward-central interpolation formula,, Sterling formula, Bessel’s formula, Interpolation with unequal intervals., Unit IV, Differentiation and Integration: Newton-Cortes formula, Trapezoidal rule, Simpson one–third rule,, Simpson three- eighth rule, Weddle’s rule., Unit V, Numerical Solution of ODE: Picard’s methods, Taylor series method, Euler’s method, Modified, Euler’s method, Runge – Kutta method, Predictor–corrector method, Milne’s method. Adams-Bash, fourth method, Second–order differential equation, Numerical solution for elliptical partial differential, equation., , 23
Page 24 :
Text Books:, 1. B.S Grewal, Higher Engineering Mathematics, 40th Edition, Khanna Publication., 2. S. S. Shastri, Introduction to Numerical Methods, PHI Publication., 3. V. Rajaraman, Computer Oriented Methods, 3rd Edition, PHI Publication., 4. Raymond P. Canale and Steven C. Chapra, Numerical Methods for Engineers, 7th Edition,, McGraw-Hill Publication., Reference Books:, 1. Conte and De boor, Elementary Numerical Analysis, BPB Publication., 2. E. Kreyszig, Advanced Engineering Mathematics, Wiley Publication., 3. Steven C Chapra, Numerical Methods for Engineers, 5th Edition, McGraw Hill Publication., 4. James F. Epperson, An Introduction to Numerical Methods and Analysis, 2nd Edition, Wiley, Publication., , CE307 Digital Circuits Laboratory, (1) Simplification, realization of Boolean expressions using logic gates/universal gates., (2) Realization of half/full adder & half/full subtractors using logic gates., (3) Realization of parallel adder/subtractors using 7483 chip, BCD to Excess-3code conversion &, vice versa., (4) Realization of binary to gray code conversion & vice versa., (5) MUX/DEMUX – use of 74153,74139 for arithmetic circuits & code converter., (6) Realization of one/two bit comparator and study of 7485 magnitude comparator., (7) Use of a) Decoder chip to drive LED display & b) Priority encoder., (8) Truth table verification of flip-flops: i) JK Master Slave ii) T type iii) D type., (9) Realization of 3-bit counters as a sequential circuit & MOD-N counter design, (7476,7490,74192,74193)., (10) Writing & testing of sequence generator., (11) Design of FSM: Moore machine, Mealy machine., , 24
Page 25 :
CE308 Object-Oriented Programming Laboratory, (1) Simple programs in C++/Java, (2) Matrix multiplication in C++/Java., (3) Operator overloading exercises., (4) Matrix manipulation using dynamic memory allocation., (5) Overloading dynamic memory allocation operators., (6) Implementation of virtual function, friend function., (7) String/text processing programs., (8) Error and Exception handling., (9) Inheritance based exercise., (10) File handling using streams, (11) Practice on templates., (12) Implementation of sorting algorithms using templates., , 25
Page 26 :
CE309 Web Page Design, Course Objectives and Outcomes:, • [WPCO1] Use a variety of strategies and tools to create websites., • [WPCO2] Create a functioning web application suitable for portfolio presentation., • [WPCO3] Learn the language of the web: HTML and CSS., • [WPCO4] Understand and apply effective web design principles., CO to PO Mapping:, PO1, WPCO1, , PO2, , PO3, , WPCO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , WPCO2, WPCO3, , PO4, , x, x, , Web Site development Essentials, Overview of Web Design Concepts, Web Development Teams, Web Project Management, Fundamentals, Web Site Development Process, Web Page Layout and Elements, Web Site Usability, and Accessibility, Configure Browsers Setting, Navigation Concepts, Web Graphics, Multimedia and, the Web., Hyper Text Markup Language (HTML), HTML and the Evolution of Markup languages, Create Hyperlinks, Create Tables, Create Web Forms,, Image Inserting Techniques, Create Frames, GUI HTML Editors, Site Content and Metadata., , Introduction to Client-Server Model, Features of Dreamweaver Interface, Setting Up a Site with Dreamweaver, FTP -Site Upload Feature of, Dreamweaver, Create various types of Links, Insert multimedia including text, image, animation &, video, Finding a Home for your WordPress Site, Installing WordPress on Your Site, Content, Management using WordPress, Selecting the Right Tools, Image Formats, Fonts and Colors, Designing, Your WordPress Site, The WordPress Default Layout, Creating a Custom Site., Cascading Style Sheets, Cascading Style Sheets for Web page design, Creating CSS rules in Dreamweaver, Format Text with, CSS, Use of CSS Selectors, Embed Style Sheets, Attach External Style Sheets., Using CSS with Tables, Insert and Styling Tables, Import Table Data, Style Tables with CSS, Sort Data in Table., 26
Page 27 :
*Programming assignments are mandatory., Reference Books:, 1. J. N. Robbins, Learning Web Design, Fourth Edition, O'Reilly Media., 2. Steven M. Schafer, HTML, XHTML, and CSS Bible, 5th Edition, Wiley India., 3. John Duckett, Beginning HTML, XHTML, CSS, and JavaScript, Wiley India., 4. Hal Stern, David Damstra, Brad Williams, Professional WordPress: Design and Development,, Wrox Publication., 5. E. Robson, E. Freeman, Head HTML & CSS, O'Reilly Media., , 27
Page 28 :
CE401 Data Communication, Course Objectives and Outcomes:, • [DCCO1] Build an understanding of the fundamental concepts of computer networking., • [DCCO2] Introduce students to the digital and analogue representations and channels., • [DCCO3] Describe the mechanism and techniques of encoding., • [DCCO4] To understand the concept of data communication and modulation techniques., • [DCCO5] To understand the error detection and correction in transmission of data., • [DCCO6] Understand, explain and calculate digital transmission over different types of, communication media., CO to PO Mapping:, PO1, , PO2, , PO3, , PO4, , PO5, , PO8, , PO9, , PO10, , x, x, , DCCO3, DCCO4, , x, , DCCO5, , x, , DCCO6, , PO7, , x, , DCCO1, DCCO2, , PO6, , x, , x, , Unit I, Introduction: Components of communication, Data representation, Data flow, Communication model,, Network, Network topologies, Network connection, Network categories, LAN, WAN, MAN, Internet,, Addressing., Unit II, Data and Signals: Analog and digital data, Analog and digital signals, Periodic and non-periodic, signals, Sine wave, Parameters of sine wave, Time and frequency domain, Composite signals,, Bandwidth, Digital signal-bit rate, Baseband and broadband transmission, Transmission impairments,, Nyquist bit rate, Shannon capacity, Performance: Throughput, Latency, Bandwidth-delay product,, Jitter., Unit III, Analog Transmission: Digital to analog conversion- Amplitude shift keying, Frequency shift keying,, Phase shift keying, Quadrature amplitude Modulation, Analog to analog Conversion – Amplitude, modulation, Frequency modulation, Phase modulation., Multiplexing: Need of multiplexing, Introduction, Multiplexer and demultiplexer, Frequency division, multiplexing, Wavelength division multiplexing, Time division multiplexing, Statistical TDM,, Synchronous TDM, Data rate management in TDM., 28
Page 29 :
Unit IV, Digital Transmission: Digital to digital conversion, Signals element, Data element, Signal rate, Data, rate, DC-component, Self synchronization, Line coding schemes – NRZ, NRZI, Bipolar AMI,, Pseudo-ternary, Manchester, Differential Manchester. Block coding schemes – 4B/5B, 8B/10B,, Scrambling –HDB3, B8ZS., Analog to digital conversion: Pulse code modulation, Delta modulation, Transmission modes- serial, and parallel transmission., Unit V, Transmission Media: Guided Media – Twisted pair cable, Co-axial cable, Fiber optic cable,, Performance of each, Unguided media – Radio waves, Microwaves, Infrared., Introduction to fiber optics: Nature of light, Fiber characteristics, Sources and detectors, Connectors, and splices., Unit VI, Error Detection and Correction: Introduction, Types of errors, Redundancy, Detection versus, correction, Forward error correction and re-transmission, Modular arithmetic, Block Coding: error, detection, error correction, Hamming distance, Minimum hamming distance, Linear block codes,, Cyclic Codes: Cyclic Redundancy check, Hardware implementation, Polynomials, Cyclic code, analysis, Checksum: Concept, One‟s component, Internet checksum., Text Books:, 1. Behrouz Forouzan, Data Communications and Networking, 4th Edition, McGraw-Hill, Publication, 2010., 2. William Stalling, Data Communications and Computer Network, PHI Publication., Reference Books:, 1. Schweber, Data Communication, McGraw Hill Publication., 2. Irvine & Harle, Data Communications and Networking, Wiley Publication., , 29
Page 30 :
CE402 Data Structures, Course Objectives and Outcomes:, • [DSCO1] Student should able to know fundamentals of data structures like array, list, linked, list, stack, queue, tree, graph, hashing., • [DSCO2] Student should able to identify suitable data structure for application., • [DSCO3] Student should able to use data structure to solve problems., • [DSCO4] Student should able to implement various data structures and algorithm essential for, implementing computer based solutions., CO to PO Mapping:, PO1, DSCO1, , x, , PO2, , PO3, , DSCO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , DSCO2, DSCO3, , PO4, , x, , x, x, , x, , Unit I, Introduction: Data, Data types, Data structure, Abstract Data Type (ADT), representation of, Information, characteristics of algorithm, program, analyzing programs., Unit II, Arrays and Hash Tables: Concept of sequential organization, linear and non-linear data structure,, storage representation, array processing sparse matrices, transpose of sparse matrices. Hash Tables,, Direct address tables, Hash tables, Hash functions, Open addressing, Perfect hashing., Unit III, Searching and Sorting: Sequential, binary searching, skip lists – dictionaries, linear list, representation, skip list representation, operations – insertion, deletion and searching. Insertion sort,, selection sort, radix sort, File handling., Unit IV, Linked Lists: Concept of linked organization, singly and doubly linked list and dynamic storage, management, circular linked list, operations such as insertion, deletion, concatenation, traversal of, linked list, dynamic memory management, garbage collection., Unit V, Stacks and Queues: Introduction, stack and queue as ADT, representation and implementation of stack, and queue using sequential and linked allocation, Circular queue and its implementation, Application of, stack for expression evaluation and expression conversion, recursion, priority queue., , 30
Page 31 :
Unit VI, Trees and Graphs: Basic terminology, binary trees and its representation, insertion and deletion of, nodes in binary tree, binary search tree and its traversal, threaded binary tree, Heap, Balanced Trees., Terminology and representation of graphs using adjacency matrix, Warshall’s algorithm., Text Books:, 1. Mark Allen Weiss, Data structures and algorithms analysis in C++, Second Edition, Pearson, Education., 2. S. Lipschutz, Data Structures, McGraw-Hill Publication., 3. Y. Langsm, M. Augenstin, A. Tanenbaum, Data Structure using C and C++, Pearsons, Education Asia Publication., 4. Trembley and Sorenson, Introduction to Data Structures, PHI Publication., Reference Books:, 1. E. Horowitz, S. Sahani, Data Structure and Algorithms, Galgotia Publication., 2. Thomas Cormen, Introduction to Algorithms, PHI Publication., 3. Venkatesan & Rose, Data Structure, Wiley Publication., 4. Goodrich & Tamassia, Data Structure & Algorithm in C++, Wiley Publication., 5. Rod Stephens, Learning Data Structures and Algorithms: Implementation and Analysis for, Increased Software Performance, O'Reilly Media., 6. Kyle Loudon, Mastering Algorithms with C: Useful Techniques from Sorting to Encryption,, O'Reilly Media., , 31
Page 32 :
CE403 Operating System, Course Objectives and Outcomes:, • [OSCO1] Understand functional architecture of an operating system., • [OSCO2] To provide a detailed discussion of the various memory management techniques., • [OSCO3] Learn about and understand theoretical concepts and programming constructs used, for the operation of modern operating systems., • [OSCO4] Gain practical experience with software tools available in modern operating systems, such as semaphores, system calls, sockets and threads., CO to PO Mapping:, PO1, OSCO1, , PO2, , PO3, , PO4, , PO5, , OSCO4, , PO7, , x, , PO8, , PO9, , PO10, x, , x, , OSCO2, OSCO3, , PO6, , x, , x, x, , x, , Unit I, Introduction and Operating system structures: Definition, Types of Operating system, Real-Time, operating system, System Components- System Services, Systems Calls, System Programs, System, structure. Virtual Machines, System Design and Implementation, System Generations., Unit II, Processes and CPU Scheduling: Process Concept, Process Scheduling, Operation on a process,, Cooperating processes. Threads, Interprocess Communication, Scheduling criteria, scheduling, Algorithms, Multiple-Processor Scheduling, Real-Time Scheduling, Scheduling Algorithms and, performance evaluation., Unit III, Process Synchronization The critical-section problem, Critical regions, Synchronization Hardware,, Semaphores, Classical Problems of synchronization, Monitors Synchronizations in Solaris., Unit IV, Deadlocks: Systems Model, Deadlock characterization, Methods for handling Deadlocks, Deadlock, Prevention, Deadlock Avoidance, Deadlock Detection, Recovery from Deadlock, Combined approach, to deadlock Handling. Logical versus Physical address space, Swapping, Contiguous allocation,, Paging, Segmentation with Paging, Demand Paging, Page replacement algorithms, Thrashing., Unit V, File System and Secondary storage devices, Real-Time Operating Systems, RT Linux and Case, Studies: MS-DOS and UNIX., 32
Page 33 :
Text Books:, 1. Abraham Silberschatz, Peter B. Galvin and Greg Gagne, Operating System Concepts, Addison, Wesley Publishing Company, 1993., 2. Andrew S. Tanenbaum, Modern Operating System, PHI Publication, 1995., Reference Books:, 1. D. M. Dhamdhere, Systems Programming and Operating Systems, 2nd Edition, McGraw Hill,, 1996., 2. Garry Nutt, Operating Systems Concepts, Addison Wesley Publication., 3. Harvey M. Deitel, An Introduction to Operating Systems, Addison Wesley Publication., 4. Doeppner, Operating System in Depth, Wiley Publication., , 33
Page 34 :
CE404 Micro-Processors (Elective 401), Course Objectives and Outcomes:, • [MPCO1] To understand the concepts of Architecture of 8086 Microprocessor., • [MPCO2] Ability to write assembly language programs to realize various high level language, constructs, considering the architectural features, memory design of the underlying hardware., To realize the issues in computer architecture and organization., • [MPCO3] Ability to interface various programmable devices to the microprocessor and, program them to perform data transfer in real life applications., • [MPCO4] Understand concept of interfacing of peripheral devices and their applications., CO to PO Mapping:, PO1, MPCO1, , PO3, , PO4, , PO5, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , MPCO2, MPCO3, MPCO4, , PO2, , x, , Unit I, Architecture of Microprocessors: General definitions of mini computers, Microprocessors, Micro, controllers and digital signal processors. Overview of 8085 microprocessor, Overview of 8086, microprocessor, Signals and pins of 8086 microprocessor., Unit II, Assembly language of 8086: Description of Instructions, Assembly directives, Assembly software, programs with algorithms., Unit III, Interfacing with 8086: Interfacing with RAMs, ROMs along with the explanation of timing diagrams,, Interfacing with peripheral IC like 8255, 8254, 8279, 8259, 8259 etc., Interfacing with keyboards,, LED, LCD, ADC, and DAC etc., Co-processor 8087: Architecture of 8087, Interfacing with 8086, Data types, Instructions and, programming., Unit V, Architecture of Micro controllers: Overview of the architecture of 8051 micro-controller, Overview, of the architecture of 8096 16 bit micro-controller. Assembly language of 8051: Description of, Instructions, Assembly directives, Assembly software programs with Algorithms., Unit VI, 34
Page 35 :
Interfacing with 8051: Interfacing with keyboards, LED, 7-segment LED, LCD, Interfacing with, ADC, Interfacing with DAC, etc., High end processors: Introduction to 80386 and 80486., Text Books:, 1. Douglas Hall, 8086 Microprocessor, Architecture and Programming, PHI Publication., 2. Muhammad Ali Mazidi, The 8051 Micro-controllers & Embedded System, Pearson Education, India Publication., 3. Turley, Advanced 80386 Programming, McGraw-Hill Publication., Reference Books:, 1. Liu, Gibson, Microcomputer System – The 8086/8088 Family, PHI Publication., 2. John F. Uffenbeck, The 8086/8088 Family Design, Programming and Interfacing, PHI, Publication., 3. Intel 8086, 80386, 80486 manuals., 4. A. K. Ray and K. M. Bhurchandi, Advanced Microprocessors and Peripherals, McGraw-Hill, Publication., , 35
Page 36 :
CE405 Probability, Statistics and Queueing Theory (Elective 402), Course Objectives and Outcomes:, • [PQCO1] Develop appropriate probabilistic model for a given problem of algorithmic nature, and computation of its statistical parameters., • [PQCO2] Learning of different methods of statistics for data analysis., • [PQCO3] Modeling of various real life problems of operation research., • [PQCO4] Determine service time and waiting time in a queue., • [PQCO5] To understand elementary queuing concepts and apply elsewhere in computer, science., CO to PO Mapping:, PO1, , PQCO3, , PO3, , PO4, , PO5, , PO7, , PO8, , PO9, , PO10, , x, x, , x, x, , PQCO4, PQCO5, , PO6, , x, , PQCO1, PQCO2, , PO2, , x, , x, , Unit I, Probability Theory: Definition of probability: classical, empirical and axiomatic approach of, probability, Addition theorem of probability, Multiplication theorem of probability, Bayes’ theorem of, inverse probability, Properties of probabilities with proofs, Examples., Unit II, Random Variable and Mathematical Expectation: Definition of random variables, Probability, distributions, Probability mass function, Probability density function, Mathematical expectation, Join, and marginal probability distributions, Properties of expectation and variance with proofs, Examples., Unit III, Theoretical Probability Distributions: Binomial distribution, Poisson distribution, Normal, distribution, Fitting of binomial distributions, Properties of binomial, Poisson and normal distributions,, Relation between binomial and normal distributions, Relation between Poisson and normal, distributions, Importance of normal distribution, Examples., Unit IV, Correlation: Introduction, Types of correlation, Correlation and causation, Methods of studying, correlation, Karl Pearson's correlation coefficient, Spearman’s rank correlation, Coefficient, Properties, of Karl Pearson's correlation coefficient, Properties of Spearman’s rank correlation coefficient,, Probable errors, Examples., 36
Page 37 :
Unit V, Linear Regression Analysis: Introduction, Linear and non-linear regression, Lines of regression,, Derivation of regression lines of y on x and x on y, Angle between the regression lines, Coefficients of, regression, Theorems on regression coefficient, Properties of regression coefficient, Examples., Unit VI, Queuing Theory: Introduction, Queuing systems, The input or arrival pattern, The service pattern and, service discipline, Notation, Performance measures, Little’s formula, Relation between the probabilities, of states, M/M/1/∞ systems, Examples., Text Books:, 1. S. C. Gupta, "Fundamentals of Statistics", 46th Edition, Himalaya Publishing House., 2. G. V. Kumbhojkar, "Probability and Random Processes", 14th Edition, C. Jamnadas and co., 3. G. Haribaskaran, "Probability, Queuing Theory and Reliability Engineering", 6th Edition,, Laxmi Publications., 4. Murray Spiegel, John Schiller, R. ALU Srinivasan, Probability And Statistics, Schaum's, Outlines., Reference Books:, 1. Kishor S. Trivedi, "Probability, Statistics with Reliability, Queuing and Computer Science, Applications", 2nd Edition, Wiley India Pvt. Ltd., 2. Vijay K. Rohatgi, A. K. Md. Ehsanes Saleh, An Introduction To Probability And Statistics,, 3rd Edition, Wiley Publication., , 37
Page 38 :
CE405 Engineering Mathematics-III (Elective 402), Unit I, Laplace Transform: Transform of elementary functions, Transform periodic function, Transform of, special function, Transform of derivative, Transform of integral, Properties of Laplace transform,, Evaluation of integrals of Laplace transform., Unit II, Inverse Laplace Transform: Properties of inverse Laplace transform, Other methods for finding, inverse Laplace transform, Convolution theorem for inverse Laplace transform, Application to the, differential equations, Simultaneous linear equations with constant coefficients., Unit III, Partial Differential Equations and Applications: Formation of Partial differential equations, Linear, equations of the first order, Homogeneous linear equations with constant coefficients, Rules for finding, complementary and particular integrals, Working procedure to solve the equations, Non-homogeneous, linear equations, Wave equations, One dimensional heat flow equation, Laplace equation., Unit IV, Series Solution of Differential Equations and Special Functions: Validity of series solution, Series, solution when x = 0 is an ordinary point, Frobenius method, Bessel’s equation, Recurrence relation for, Jn(x), Crthogonality of Bessel function., Unit V, Fourier Transform: Fourier integral: Fourier sine and cosine integral – complexity forms of Fourier, integral, Fourier transform – Fourier sine and cosine transform – finite Fourier sine and cosine, transform, Properties of F- transform, Convolution theorem for F- transform, Parseval’s identity for Ftransform., Unit VI, Integral Equations: Conversion of linear differential equation to an integral equation and vice versa,, Conversion of boundary value problem to integral equation using Green’s functions, Solution of an, integral equations, Integral equations of the convolution type, Abel’s integral equation,, Intergro-differential equation, Solution of Fredhlom and Volterra equations by the methods of, successive approximations., Text Books:, 1. B. S. Grewal, Higher Engineering Mathematics, Khanna Publication., 2. Kreszig, Advanced Engineering Mathematics, 6th Edition, Wiley Eastern Publication., 3. Ravish R. Singh and Mukul Bhatt, Engineering Mathematics, McGraw-Hill Publication., Reference Books:, 1. Ray C. Wylie, Advanced Engineering Mathematics, 4th Edition. McGraw-Hill Publication., 2. E. Kreyszig, Advanced Engineering Mathematics, Wiley Publication., 38
Page 39 :
CE406 Data Structure Laboratory, 1., 2., 3., 4., 5., 6., , Write a program to implement stack using arrays., Write a program to evaluate a given postfix expression using stacks., Write a program to convert a given infix expression to postfix form using stacks., Write a program to implement circular queue using arrays., Write a program to implement double ended queue (dequeue) using arrays., Write a program to implement a stack using two queues such that the push operation runs in, constant time and the pop operation runs in linear time., 7. Write a program to implement a stack using two queues such that the push operation runs in, linear time and the pop operation runs in constant time., 8. Write a program to implement a queue using two stacks such that the enqueue operation runs, in constant time and the dequeue operation runs in linear time., 9. Write programs to implement the following data structures: (a) Single linked list (b) Double, linked list., 10. Write a program to implement a stack using a linked list such that the push and pop operations, of stack still take O(1) time., 11. Write a program to create a binary search tree(BST) by considering the keys in given order, and perform the following operations on it. (a) Minimum key (b) Maximum key (c) Search for, a given key (d) Find predecessor of a node (e) Find successor of a node (f) delete a node with, given key., 12. Write a program to construct an AVL tree for the given set of keys. Also write function for, deleting a key from the given AVL tree., 13. Write a program to implement hashing with (a) Separate Chaining and (b) Open addressing, methods., 14. Implement the following sorting algorithms: (a) Insertion sort (b) Merge sort (c) Quick sort, (d) Heap sort., 15. Write programs for implementation of graph traversals by applying: (a) BFS (b) DFS., , 39
Page 40 :
CE407 Operating System Laboratory, 1. Hands on Unix Commands, 2. Shell programming for file handling., 3. Shell Script programming using the commands grep, awk, and sed., 4. Implementation of various CPU scheduling algorithms (FCFS, SJF, Priority)., 5. Implementation of various page replacement algorithms (FIFO, Optimal, LRU)., 6. Concurrent programming; use of threads and processes, system calls (fork and v-fork)., 7. Study pthreads and implement the following: Write a program which shows the performance, improvement in using threads as compared with process.(Examples like Matrix Multiplication,, Hyper Quick Sort, Merge sort, Traveling Sales Person problem)., 8. Implementation of Synchronization primitives – Semaphore, Locks and Conditional Variables., 9. Implementation of Producer-Consumer problem, Bankers algorithm., 10. Implementation of various memory allocation algorithms, (First fit, Best fit and Worst fit), Disk, Scheduling algorithms (FCFS, SCAN, SSTF, C-SCAN)., 11. Kernel reconfiguration, device drivers and systems administration of different operating, systems., 12. Writing utilities and OS performance tuning., , 40
Page 41 :
CE408 Web Application Development, Course Objectives and Outcomes:, • [WACO1] Develop skills in client-side web application development technologies including, HTML, CSS, Javascript, and Javascript libraries., • [WACO2] Program, access, and manipulate data through the adoption of accepted standards,, mark-up languages, client-side programming, and server-side programming, • [WACO3] Understand and customize an existing open source application., • [WACO4] Design and implement an interactive web site(s) with regard to issues of usability,, accessibility and internationalization., CO to PO Mapping:, PO1, WACO1, , PO2, , PO3, , WACO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , WACO2, WACO3, , PO4, , x, , x, x, , x, , I. Client Side Scripting / Coding – Client Side Scripting is the type of code that is executed or, interpreted by browsers. Client Side Scripting is generally view-able by any visitor to a site (from the, view menu click on "View Source" to view the source code)., Below are some common Client Side Scripting technologies:, • HTML (HyperText Markup Language), • CSS (Cascading Style Sheets), • JavaScript, • Ajax (Asynchronous JavaScript and XML), • jQuery (JavaScript Framework Library – commonly used in Ajax development), • MooTools (JavaScript Framework Library – commonly used in Ajax development), • Dojo Toolkit (JavaScript Framework Library – commonly used in Ajax development), II. Server Side Scripting / Coding – Server Side Scripting is the type of code that is executed or, interpreted by the web server., Server Side Scripting is not view-able or accessible by any visitor or general public., Below are the common Server Side Scripting technologies:, • PHP (very common Server Side Scripting language – Linux / Unix based Open Source – free, redistribution, usually combines with MySQL database), • Zend Framework (PHP's Object Oriented Web Application Framework), • ASP (Microsoft Web Server (IIS) Scripting language), ASP.NET (Microsoft's Web Application, 41
Page 42 :
Framework – successor of ASP), • ColdFusion (Adobe's Web Application Framework), • Ruby on Rails (Ruby programming's Web Application Framework – free redistribution), • Perl (general purpose high-level programming language and Server Side Scripting Language –, free redistribution – lost its popularity to PHP), *Programming assignments are mandatory., Reference Books:, 1. Santosh Kumar K., Kogent Learning Solutions Inc., JDBC, Servlets, and JSP (Includes JSF and, Design Patterns) Black Book, Dreamtech Press/Wiley India., 2. Vivek Chopra, Jon Eaves, Rupert Jones, Sing Li, John T. Bell, Beginning JavaServer Pages,, Wrox Publication., 3. Janet Valade, PHP and MySQL For Dummies, 4th Edition., 4. Rasmus Lerdorf, Programming PHP, Third Edition, O'Reilly Media., 5. Bruce W. Perry, JAVA Servlet & JSP Cookbook, O'Reilly Media., 6. Gorge Reese, Database Programming with JDBC & JAVA, O'Reilly Media., , 42
Page 43 :
CE409 Python Programming, Course Objectives and Outcomes:, • [PPCO1] Develop a basic understanding of the Python programming language., • [PPCO2] To learn how to design and program Python applications., • [PPCO3] Demonstrate significant experience with Python program development environment., • [PPCO4] Solve problems requiring the writing of well-documented programs in the Python, language, including use of the logical constructs of that language., CO to PO Mapping:, PO1, PPCO1, , x, , PPCO2, , x, , PO2, , PO3, , PO4, , PO5, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , PPCO3, , x, , PPCO4, , x, , x, , Informal introduction to programming, algorithms and data structures, Downloading and installing, Python, run a simple program on Python interpreter., Variables, operations, control flow – assignments, conditionals, loops, functions: optional arguments,, default values, Passing functions as arguments., Statements, Expressions, Strings: String processing. Exception handling, Basic input/output, Handling, files., Class and Object, Data Structure: List, Tuple and Sequences, Set, Dictionaries., Using Database and Structured Query Languages (SQL): SQLite manager, Spidering Twitter using a, Database, Programming with multiple tables, JOIN to retrieve data., *Programming assignments are mandatory., Text Books:, 1. Michael Urban and Joel Murach, Murach’s Python Programming, Murach's Publication., 2. "Python for Informatics: Exploring Information", Charles Severance, University of Michigan., 3. "Core Python Programming", Dr. R. Nageswara Rao, Dreamtech Press., Reference Books:, 1. Mark Lutz, Learning Python, Fifth Edition, O'Reilly Media., 2. "Dive into Python 3", Mark Pilgrim, Apress Publication., 3. "Think Python", Allen B. Downey, 2nd Edition, O'Reilly Media., 43
Page 44 :
4. "Algorithm Design", Jon Kleinberg and Eva Tardos, Pearson (2013)., , CE501 Database Management System, Course Objectives and Outcomes:, • [DBCO1] Model, design and normalize databases for real life applications., • [DBCO2] To learn data models, conceptualize and depict a database system using ER diagram., • [DBCO3] Query Database applications using Query Languages like SQL., • [DBCO4] Understand validation framework like integrity constraints, triggers and assertions., • [DBCO5] Understand various storage structures and query optimization., CO to PO Mapping:, PO1, DBCO1, DBCO2, , x, , PO3, , PO4, , PO5, , x, , x, , x, , x, , PO7, , PO8, , PO9, , PO10, x, , x, x, , DBCO4, , PO6, , x, x, , DBCO3, DBCO5, , PO2, , x, , x, , x, , Unit I, Introduction to DBMS: Historical perspective, File Versus a DBMS, Advantages of DBMS,, Describing and storing data in DBMS, Architecture of a DBMS, Different Data Models., Unit II, Introduction to the Relational Model: Structure of Relational Databases, Database Schema, Keys,, Schema Diagrams, Relational Query Languages, Relational Operations., Database Design and the E-R Model: features of ER model, conceptual design using ER model,, design for large enterprises, Relational model-structure and operations, Integrity constraints over, relations, Extended E-R Features., Unit III, Query Language: Overview, SQL Data Definition, Basic Structure of SQL Queries, Additional Basic, Operations, Set Operations, Null Values, Aggregate Functions, Nested Subqueries, Modification of the, Database, Join Expressions, Views, Integrity Constraints, SQL Data Types and Schemas, Authorization,, Functions and Procedures, Triggers, The Relational Algebra, The Tuple Relational Calculus, The, Domain Relational Calculus., Functional Dependency: Closer of functional dependencies, closer of attributes, canonical cover and, Properties of Decomposition, Normalization process- 1NF, 2NF, 3NF and BCNF, Multivalued, dependency: Closer properties of Multi-valued dependency and 4NF., 44
Page 45 :
Unit IV, Database Application Development: Accessing Databases from Applications, An Introduction to, JDBC, JDBC Classes and Interfaces, SQLJ, Stored Procedures., Storage and File Structure: Overview of Physical Storage Media, Magnetic Disk and Flash Storage,, RAID, Tertiary Storage, File Organization, Organization of Records in Files, Data-Dictionary Storage,, Database Buffer., Unit V, Indexing and Hashing: Intuition For Tree Indexes, Indexed Sequential Access Method (ISAM), B+, Trees: A Dynamic Index Structure, Search, Insert, Delete, Duplication, B+ Trees in Practice, Static, Hashing, Extendable Hashing, Linear Hashing, Extendable vs. Linear Hashing., Unit VI, Query Processing: Overview of Query Evaluation, operator evaluation, Algorithms for relational, operations- Selection operation, General selection condition, Projection operation, Join operation, set, operation and aggregate operation, Evaluation of relational operations., Query optimization: Alternative plans, functions of query optimizer, translating SQL queries into, relational algebra, estimating the cost of a plan, relational algebra equivalences, and other approaches, to query optimization., Text Books:, 1. C. J. Date, Introduction to Database Management, Narosa Publication., 2. Henry Korth, Abraham Silberschatz & S. Sudarshan, Database System Concepts, 6th Edition,, McGraw Hill Publication., 3. Database Management Systems, Raghu Ramakrishnan & Johannes Gehrke, McGraw-Hill, Publication., 4. James Martin, Principles of Database Management, McGraw Hill Publication., Reference Books:, 1. Joel Murach, Murach's Oracle SQL and PL/SQL for Developers, 1st Edition, Mike Murach &, Associates., 2. Wiederhold, Database Design, McGraw Hill Publication., 3. Navathe, Fundamentals of Database System, Addison Wesley Publication., 4. Mark L. Gillenson, Fundamental of Database Management System, Wiley Publication., , 45
Page 46 :
CE502 Design and Analysis of Algorithms, Course Objectives and Outcomes:, • [DACO1] Analyzing the amortized time complexity of a given algorithm and data structure, operations., • [DACO2] Decide the appropriate design methodology for a given problem from among the, paradigms of Divide and Conquer, Dynamic Programming, Greedy, Branch and Bound., • [DACO3] Design algorithms for network flows., • [DACO4] Distinguish between P and NP classes of problems., CO to PO Mapping:, PO1, DACO1, DACO2, DACO3, , PO2, , PO3, , PO4, , PO5, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , x, x, , DACO4, , Unit I, Introduction to Algorithms: Definition of Algorithms, Properties of Algorithms, Expressing, Algorithm, Flowchart, Algorithm Design Techniques, Performance Analysis of Algorithms, Types of, Algorithm's Analysis, Order of Growth, Asymptotic Notations, Recursion, Recurrences Relation,, Substitution Method, Iterative Method, Recursion Tree, Master Theorem, Changing Variable, Heap, Sort., Unit II, Divide and Conquer: Introduction to Divide and Conquer Technique, Binary Search, Merge Sort,, Quick Sort, Strassen’s Matrix Multiplication., Unit III, Greedy Algorithms: Introduction to Greedy Technique, Greedy Method, Optimal Merge Patterns,, Huffman Coding, Knapsack Problem, Activity Selection Problem, Job Sequencing with Deadline,, Minimum Spanning Tree, Single-Source Shortest Path Algorithm., Unit IV, Dynamic Programming: Introduction, Characteristics of Dynamic Programming, Component of, Dynamic Programming, Comparison of Divide-and-Conquer and Dynamic Programming Techniques,, Longest Common Sub-sequence, matrix multiplication, shortest paths: Bellman Ford, Floyd Warshall,, Application of Dynamic Programming., Unit V, Backtracking: Backtracking Concept, N–Queens Problem, Four–Queens Problem, Eight–Queen, 46
Page 47 :
Problem, Hamiltonian Cycle, Sum of Subsets Problem, Graph Coloring Problem., Branch and Bound: Introduction, Traveling Salesperson Problem, 15-Puzzle Problem, Comparisons, between Backtracking and Branch and Bound., Unit VI, Tree: Introduction, B-tree, Red-Black Tree (RBT): Insertion, Deletion., NP Completeness: Introduction, The Complexity Class P, The Complexity Class NP, Polynomial-Time, Reduction, The Complexity Class NP-Complete., Text Books:, 1. Cormen, Introduction to Algorithms, 2nd Edition, PHI Publication., 2. Elise Horowitz, Sartaj Sahni, S. Rajasekaran, Fundamentals of Computer Algorithms, 2nd, Edition, University Press (India) Private Ltd., 3. Sara Base, Computer algorithms: Introduction to Design and Analysis, 2nd Edition, Addison, Wesley Publication, 1988., Reference Books:, 1. Aho, Ullman, Data Structure and Algorithms, Addison Wesley Publication., 2. Michel Goodrich, Roberto Tamassia, Algorithm Design – Foundation, Analysis & Internet, Examples, Wiley Publication., 3. George T. Heineman, Gary Pollice, Stanley Selkow, Algorithms in a Nutshell, 2nd Edition A, Practical Guide, O'Reilly Media., , 47
Page 48 :
CE503 Theory of Computation, Course Objectives and Outcomes:, • [TCCO1] Design finite state machines, regular expressions and grammars for given languages., • [TCCO2] Understand formal machines, languages and computations, • [TCCO3] Develop analytical thinking and intuition for problem solving situations in related, areas of theory of computation., • [TCCO4] To know the limitations of computation, i.e. the unsolvability of problems., CO to PO Mapping:, , TCCO1, , PO1, , PO2, , x, , x, , TCCO2, , x, , TCCO3, , x, , PO3, , PO4, , PO5, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , TCCO4, , Unit I, Finite Automata and Regular Expressions: Definition of deterministic finite automata,, Non-deterministic finite automata, Moore and Mealy machines and their conversions, Regular, expressions, Recursive definition, NFA with e-moves, Inter-conversion between NFA and DFA,, Regular expression and FA, Pumping lemma., Unit II, Context Free Grammars: Definition, Production rules, Ambiguous grammar, Removal of ambiguity,, Chomsky hierarchy, Context Free Grammar (CFG) – definition, Simplification of CFG., Unit III, Context Free Languages: Definition of context free languages, Regular grammar definition, Left, linear, Right linear grammar, Interconversion between left linear and right linear regular grammar,, Regular grammar and finite automata, CNF, GNF, Derivation graphs, Type 0 and Type 1 grammars., Unit IV, Pushdown Automata: Formal definition, Pushdown automata (PDA), Deterministic Pushdown, automata (DPDA) – definition, Non-deterministic Pushdown automata (NPDA)-definition, relative, powers of DPDA and NPDA., Unit V, Turing Machines: The definition of a Turing machine, Computing with Turing machine, Extensions of, Turing machines, Random access Turing machines, Non-deterministic Turing machines, Grammars,, The Church’s Turing hypothesis, Universal Turing machines, The Halting problem, Unsolvable, problems about Turing machines., 48
Page 49 :
Unit VI, Applications: Applications of RE and FA – Lexical analyzer, Text editor and searching using RE,, Applications of PDA – Expression conversion, Applications of CFG – syntax analysis, Language, definition., Text Books:, 1. Hopcroft, Ullman, Motwani, Introduction to Automata Theory, Languages, and Computation,, Addison Wesley Publication., 2. Daniel I. A. Cohen, Introduction to Computer Theory, Wiley Publication., Reference Books:, 1. John C. Martin, Introduction to Languages and Theory of Computation, McGraw Hill, Publication., 2. Krithivasan Kamala, Introduction to Formal Languages, Automata Theory and Computation,, Pearson Education., 3. Papadimitriou, Lewis, Elements of the Theory of Computations, PHI Publication., 4. E. V. Krishnmurthy, Theory of Computer Science, EWP Publication., , 49
Page 50 :
CE504 Object Oriented Analysis and Design (Elective 501), Course Objectives and Outcomes:, • [OOCO1] Develop a working understanding of formal Object-Oriented Analysis and Design, processes., • [OOCO2] Analyze real problems/requirements and design systems by developing specifications, and abstractions to make development of complex systems easy., • [OOCO3] Develop the skills to determine which processes and OOAD techniques should be, applied to a given project., • [OOCO4] Develop an understanding of the application of OOAD practices from a software, project management perspective., CO to PO Mapping:, PO1, OOCO1, , PO2, , PO3, , PO5, , PO6, , x, , x, , x, , PO7, , PO8, , PO9, , PO10, , x, , OOCO2, x, , OOCO3, OOCO4, , PO4, , x, , x, , x, , Unit I, Introduction Overview of object oriented system, Object orientation, Objects, attributes, object, behavior, Object respond to messages, encapsulation, Inheritance, Polymorphism, object relationships, and association, aggregation, Object identity static and dynamic binding, Object persistence, meta, classes. Object oriented system development life cycle., Unit II, Object oriented modeling Modeling, UML Modeling, class diagram, activity diagram, Sequence, diagram, collaboration diagram state chart diagram, interaction diagram, Implementation diagram, use, case diagram., Unit III, Object oriented analysis Use case analysis, CRC card analysis, Unit IV, Object Oriented Design Design Patterns., Unit V, Implementation From Design to Implementation, Programming Style, Object-Oriented languages,, Non- Object- Oriented languages, Object Oriented Databases. Computer animation, Electrical, Distribution design System, Future of Object-Oriented Technology., , 50
Page 51 :
Text Books:, 1. Grady, Booch, Object Oriented analysis and design with applications, 2nd Edition, PHI., 2. James Rumbaugh, Object-Oriented Modeling And Design, 1st Edition, PHI Publication., 3. Ali Bahrami, Object Oriented Systems Development, 1st Edition, McGraw-Hill Publication., Reference Books:, 1. Robert Lafore, Object Oriented Programming, Galgotia Publication., 2. Dan Pilone, Neil Pitman, UML 2.0 in a Nutshell: A Desktop Quick Reference, O'Reilly Media., 3. E. Balagurusamy, Object Oriented Programming, McGraw-Hill Publication., 4. S. Koshafian, Object Orientation, Wiley Publication., 5. Mike O'Docherty, Object-Oriented Analysis Design: Understanding System Development with, UML 2.0, Wiley Publication., , 51
Page 52 :
CE504 Introduction to Data Analytics (Elective 502), Course Objectives and Outcomes:, • [IDCO1] Understand big data challenges in different domains including social media,, transportation, finance and medicine., • [IDCO2] Use data analytics to explore and gain a broad understanding of a dataset., • [IDCO3] Use data analytics methods to make predictions for a dataset., • [IDCO4] Predict outcomes with supervised machine learning techniques., • [IDCO5] Apply basic machine learning algorithms Linear Regression, k-Nearest Neighbors, (k-NN), k-means, Naive Bayes for predictive modeling to solve various real-life examples., CO to PO Mapping:, PO1, IDCO1, , PO2, , PO4, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , x, , x, , x, x, , IDCO4, IDCO5, , PO5, , x, , IDCO2, IDCO3, , PO3, , x, , x, , x, , Descriptive Statistics: Introduction to the course, Descriptive Statistics, Probability Distributions., Inferential Statistics: Inferential Statistics through hypothesis tests. Regression & ANOVA: Regression,, ANOVA(Analysis of Variance)., Machine Learning: Introduction and Concepts: Differentiating algorithmic and model based, frameworks, Regression: Ordinary Least Squares, Ridge Regression, Lasso Regression, K Nearest, Neighbours Regression & Classification., Supervised Learning with Regression and Classification techniques-1: Bias-Variance Dichotomy,, Model Validation Approaches, Logistic Regression, Linear Discriminant Analysis, Quadratic, Discriminant Analysis, Regression and Classification Trees, Support Vector Machines., Supervised Learning with Regression and Classification techniques-2: Ensemble Methods: Random, Forest, Neural Networks, Deep learning., Unsupervised Learning and Challenges for Big Data Analytics: Clustering, Associative Rule Mining,, Challenges for big data analytics., Prescriptive analytics: Creating data for analytics through designed experiments, Creating data for, analytics through Active learning, Creating data for analytics through Reinforcement learning., 52
Page 53 :
Reference Books:, 1. Michael Milton, Head First Data Analysis A learner's guide to big numbers, statistics, and, good decisions, O'Reilly Media., 2. Hastie, Trevor, et al., The elements of statistical learning. Vol. 2. No. 1, New York: Springer., 3. Montgomery, Douglas C., and George C. Runger, Applied statistics and probability for, engineers, John Wiley & Sons., 4. Anil Maheshwari, Data Analytics, McGraw-Hill Publication., 5. EMC Education Services, Data Science & Big Data Analytics: Discovering, Analyzing,, Visualizing and Presenting Data, Wiley Publication., 6. Philipp K. Janert, Data Analysis with Open Source Tools A Hands-On Guide for Programmers, and Data Scientists, O'Reilly Media., , 53
Page 54 :
CE504 Digital Image Processing (Elective 501), Course Objectives and Outcomes:, • [DICO1] To understand the fundamentals of Digital imaging and Image Processing techniques., • [DICO2] Apply various filtering techniques and segmentation methods for image enhancement, and image segmentation., • [DICO3] Image restoration techniques and methods used in digital image processing., • [DICO4] To be familiar with image compression and segmentation., CO to PO Mapping:, PO1, DICO1, , PO2, , PO3, , PO4, , PO5, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , DICO2, DICO3, , x, , DICO4, , x, , x, x, , x, , Introduction: Light, Brightness adaption and discrimination, Pixels, coordinate conventions, Imaging, Geometry, Perspective Projection, Spatial Domain Filtering, sampling and quantization., Spatial Domain Filtering: Intensity transformations, contrast stretching, histogram, equalization,, Correlation and convolution, Smoothing filters, sharpening filters, gradient and Laplacian., Filtering in the Frequency domain: Hotelling Transform, Fourier Transforms and properties, FFT, (Decimation in Frequency and Decimation in Time Techniques), Convolution, Correlation, 2-D, sampling, Discrete Cosine, Transform, Frequency domain filtering., Image Restoration: Basic Framework, Interactive Restoration, Image deformation and geometric, transformations, image morphing, Restoration techniques, Noise characterization, Noise restoration, filters, Adaptive filters, Linear, Position invariant degradation, Estimation of Degradation functions,, Restoration from projections., Image Compression: Encoder-Decoder model, Types of redundancies, Lossy and Lossless, compression, Entropy of an information source, Shannon's 1st Theorem, Huffman Coding, Arithmetic, Coding, Golomb Coding, LZW coding, Transform Coding, Sub-image size selection, blocking, artifacts, DCT implementation using FFT, Run length coding, FAX compression (CCITT Group-3 and, Group-4), Symbol-based coding, JBIG-2, Bit-plane encoding, Bit-allocation, Zonal Coding, Threshold, Coding, JPEG, Lossless predictive coding, Lossy predictive coding, Motion Compensation., Wavelet based Image Compression: Expansion of functions, Multi-resolution analysis, Scaling, functions, MRA refinement equation, Wavelet series expansion, Discrete Wavelet Transform (DWT),, Continuous Wavelet Transform, Fast Wavelet Transform, 2-D wavelet Transform, JPEG-2000, 54
Page 55 :
encoding, Digital Image Watermarking., Morphological Image Processing: Basics, SE, Erosion, Dilation, Opening, Closing, Hit-or-Miss, Transform, Boundary Detection, Hole filling, Connected components, convex hull, thinning,, thickening, skeletons, pruning, Geodesic Dilation, Erosion, Reconstruction by dilation and erosion., Image Segmentation: Boundary detection based techniques, Point, line detection, Edge detection, Edge, linking, local processing, regional processing, Hough transform, Thresholding, Iterative thresholding,, Otsu's method, Moving averages, Multi-variable thresholding, Region-based segmentation, Watershed, algorithm, Use of motion in segmentation., Reference Books:, 1. Digital Image Processing, 3rd Edition, by Rafael C. Gonzalez and Richard E. Woods, Pearson, Education., 2. Ramesh R. Manza, Yogesh M. Rajput, Deepali Rathod, Manjiri B. Patwari, Understanding, Digital Image Processing Using MATLAB, SPD Publication., 3. William K. Pratt, Digital Image Processing, PIKS Scientific Inside, Fourth Edition, Wiley, Publication., 4. J. R. Parker, Algorithms for Image Processing and Computer Vision, 2nd Edition, O'Reilly, Media., 5. S. Jayaraman, S. Esakkirajan, T. Veerakumar, Digital Image Processing, McGraw-Hill, Publication., , 55
Page 56 :
CE505 Management Sciences (Elective 502), Management: Managing in global environment, Principles of Management, Management Theory,, Management Levels & Skills., Ethics: Ethical issues in management, ethical challenges and social responsibility of business., Planning and organizing: Strategic & operational plans, process of planning, organizational design &, structure, decentralization, departmentation, Types of organization, Delegation of authority., Human resource management: Staffing, selection, placement, Orientation & training, Performance, appraisal, Career planning., Leadership: Managers Vs Leaders, leadership styles, Foundation of leadership, Role and functions of, leaders, Motivation, Essence of motivation, issues in motivation, Approaches to motivation, Theories, of motivation., Decision Making & Information Systems: Decision making process, Individual & group decisions,, Decision making models, Decision making tools, Management information system for decision, making, Communication – Interpersonal, grapevine–process, Technology & communication., Group Behavior: Group Behavior and Team Building, Individual vs. Group Behavior, Group dynamics,, team building, Conflict Management – Kinds & causes of conflict, Settlement of conflict., Controlling: Process, Methods, Use of MIS for control., , NPTEL CONTENT:, 1. Management Science-I by Prof. M. Thenmozhi, IIT Madras (WEB CONTENT), 2. Management Science-I by Prof. Anuradha Sharma, IIT Delhi (VIDEO CONTENT), , 56
Page 57 :
CE505 Development Engineering (Elective 502), Introduction to Development Engineering: Introduction to development engineering; need of, development engineering; core disciplines and concept; major issues in development; urban, development; rural development; socioeconomic development; scientific social research, formulation, of research problem, field work and data collection, report drafting., Design of Sustainable Communities: Concept and development of sustainable communities;, Sustainable design principles, building regulations, codes and standards – ANSI, ASTM, ASHRAE,, approval process; green buildings – green building techniques-energy solutions, site solutions, site, solutions, exterior and interior solutions, Certification – BREEAM, GRIHA, NAHB, LEED, IGBC., Town/City Planning: Town Planning, history of town planning in India, characteristics of, city/town, town planning at national, regional and local levels, planning standards, master plan, site, layout and development, zoning and density control, green belt, slum redevelopment; Smart city, planning introduction to city planning, infrastructure elements of smart city planning, d imensions of, smart cities global standards and performance benchmark; smart solutions e-governance, waste, management, water management, energy management, urban mobility, citizen services, other services, such as telemedication and education, trade facilitation, skill development; GIS for Planning., Planning and Development of Rural Areas: District administration, District Planning, introduction, to various sectors of rural areas such as drinking water, Waste water treatment, electricity, public, transport, irrigation, sanitation and cooking energy; issues and challenges associated with these, sectors; People’s participation and role in development of rural areas; various schemes and policies, floated by state and central government – phases in the schemes; life cycle costing of these schemes., Geoinformatics for Planning and Development: Introduction to Geoinformatics; Advantages,, benefits and limitations; Interdisciplinary applications; Data extraction; use of Geoinformatics for, planning, mapping and preparation of layouts., Development aspects: Urban and Rural: Planning and designing of a model town / city and using, Auto-CAD and/or GIS, Visit to a village or small town – The project will be carried out in groups., Problem faced by the villagers pertaining to various sectors or existing schemes; define the need,, method, tools and techniques for development; deliver technology based solution., Text Books:, 1. Chand M. and Purr U.K. (1983), 'Regional Planning in India’, Allied Publisher, New Delhi., 2. Kaiser E. J., et.at., ‘Urbun Landuse Planning’, 4th Edition Urbana, University of Illinois, Press., 3. Sundaram K. V., ‘Geography Planning’, Concept Publishing Co., New Delhi., 4. Ayyar C.P.V., ‘Town Planning in Early South India’, Mittal Publications, Delhi., 5. Reeder, Hoboken, 'Guide to green building rating systems’, John Wiley & sons, Inc., 6. Longley, et.al, ‘Geographic Information Systems and Science’, John Wiley & Sons, New York., 7. Desai V., ‘Rural Development of India’, Himalaya publishing house, Mumbai., 57
Page 58 :
8. Rau S. K., ‘Global Search for Rural Development’, NIRD, Hyderabad., Reference Books:, 1. Institute of Town Planners, India, Ministry of Urban Affairs & Employment, Government of India,, New Delhi, UDPFI Guidelines, 1996., 2. Miles R. Simon, 1970, ‘Metropolitan Problems’, Methuen Publications, Canada., 3. B.I.S., 1980, 'National Building Code of India’, ISI, New Delhi., 4. ANSI/ASHRAE/USGBC/IES Standard 189.1, Standard for the Design of High – Performance Green, Buildings Except Low-Rise Residential Buildings., 5. ASHRAE Standard 90.1, Energy Standard for Buildings Except Low-Rise Residential, Buildings., , 58
Page 59 :
CE505 National Service Scheme – I (NSS-I) (Elective 502), Unit I, Introduction and Basic Concepts of NSS, History, Philosophy, Aims & objectives of NSS Organizational structure, Concept of regular activities,, Special camping, Day Camps. Basis of adoption village/slums, Methodology of conducting Survey., Unit II, Youth and community mobilization, Definition, Profile of youth, Categories of youth, Issues, Challenges and opportunities for youth, Youth, as an agent of social change, Youth-adult partnership, Mapping of community stakeholders, Identifying, methods of mobilization, Needs & importance of volunteerism., Unit III, Importance and Role of Youth Leadership, Meaning and types of leadership, Qualities of good leaders; Traits of leadership, Importance and role of, youth leadership., Unit IV, Life Competencies and skill, Definition and importance of life competencies, Communication, Inter Personal, Problem solving and, decision making, Positive thinking, Self-confidence and self-esteem, Life goals, Stress and time, management., Unit V, Social Harmony and National Integration, Indian history and culture, Role of youth in peace-building and conflict resolution, Role of youth in, Nation building., Unit VI, Youth Development Programmes in India, National Youth Policy, Youth development programmes at the National Level, State Level and, voluntary sector, Youth-focused and Youth-led organizations., References Books:, 1. National Service Scheme Manual (Revised) 2006, Government of India, Ministry of Youth, Affairs and Sports, New Delhi., 2. University of Mumbai National Service Scheme Manual, 2009., 3. Avhan Chancellor’s Brigade – NSS Wing, Training camp on Disaster Preparedness Guidelines,, March 2012., 4. Rashtriya Seva Yojana Sankalpana – Prof. Dr. Sankay Chakane, Dr. Pramod Pabrekar, Diamond, Publication, Pune., 5. National Service Scheme Manual for NSS District Coordinators, National Service Scheme Cell,, Dept. of Higher and Technical Education, Mantralaya., 6. Annual report of National Service Scheme (NSS) published by Dept. of Higher and Technical, 59
Page 61 :
CE506 Database Management System Laboratory, 1. Defining schema for applications., 2. Creating tables, Renaming tables, Data constraints (Primary key, Foreign key, Not Null), Data, insertion into a table., 3. Grouping data, aggregate functions, Oracle functions (mathematical, character functions)., 4. Sub-queries, Set operations, Joins., 5. Creation of databases, writing SQL and PL/SQL queries to retrieve information from the, databases., 6. Triggers & Cursors., 7. Normal Forms: First, Second, Third and Boyce Codd Normal Forms., 8. Assignment in Design and Implementation of Database systems or packages for applications, such as office automation, hotel management, hospital management;, 9. Deployment of Forms, Reports Normalization, Query Processing Algorithms in the above, application project;, 10. Large objects – CLOB, NCLOB, BLOB and BFILE,, 11. Distributed data base Management, creating web-page interfaces for database applications, using servlet., , CE507 Design and Analysis of Algorithm Laboratory, 1. Divide and conquer method (quick sort, merge sort, Strassen's matrix multiplication)., 2. Greedy method (knapsack problem, job sequencing, optimal merge patterns, minimal spanning, trees)., 3. Dynamic programming (multistage graphs, OBST, 0/1 knapsack, traveling sales person, problem)., 4. Obtain the Topological ordering of vertices in a given digraph., 5. Back tracking (n-queens problem, graph coloring problem, Hamiltonian cycles)., 6. Selection: Minimum/ Maximum, Kth smallest element., 7. Find optimal ordering of matrix multiplication. (Note: Use Dynamic programming method)., 8. Use dynamic programming algorithm to solve the optimal binary search tree problem., 9. Compute the transitive closure of a given directed graph using Warshall's algorithm., 10. Write programs to find out a minimum spanning tree of a simple connected undirected graph, by applying: (a) Prim’s algorithm (b) Kruskal’s algorithm., 11. Write a program to implement Dijkstra’s algorithm for solving single source shortest path, problem using priority queue., 12. Write a program to implement Floyd-Warshall algorithm for solving all pairs shortest path, problem., , 61
Page 62 :
CE508 Smart Phone Application Development, Course Objectives and Outcomes:, • [SPCO1] To learn the basics of mobile application development., • [SPCO2] To get accustomed to different Mobile Operating System platforms., • [SPCO3] To develop skills in developing applications on different flavors of Mobile Operating, System., CO to PO Mapping:, PO1, SPCO1, SPCO2, SPCO3, , x, , PO2, , PO3, , PO4, , PO5, , PO6, , x, , x, , x, , PO7, , PO8, , PO9, , PO10, , x, x, x, , (a) Introduction to mobile computing, installing of required software and preparing the working, environment, creating your first Android Application;, (b) Layouts, Views, Resources, Activities, Intents, Background tasks, Connecting to the Internet,, Fragments, Preferences;, (c) User Interaction – input, menu items, custom views;, (d) User Experience – themes and styles, material design, adaptive layouts, accessibility,, localization, debugging the UI;, (e) Storing Data, SQLite database, Sharing Data, content resolver and providers, loaders to load, data Services, background work, alarms, broadcast receivers;, (f) Notification, widgets, transferring data efficiently, publishing app, Multiple form factors,, sensors, Google cloud messaging, monetizing your app., Experiments:, 1. Install the Android SDK and developer tools and build a test project to confirm that those tools, are properly installed and configured., 2. Write a program using a Table Layout for our restaurant data entry form, add a set of radio, buttons to represent the type of restaurant., 3. Write a program using activity class to show different events., 4. Write a program to send user from one application to another. (For example redirection to map)., 5. Write a program to play audio files., 6. Write a program to play video files., 7. Write a program to capture image using built in camera., 8. Write a program to send SMS., 9. Write a program to convert text to speech., 10. Write a program to call a number., , 62
Page 63 :
Reference Books:, 1. Brian Fling, Mobile Design & Development, O'Reilly Media., 2. Meier, Android 4 Application Development: Professional, Wrox Publication., 3. Lee, Beginning AndroidTM 4 Application Development, Wrox Publication., 4. J.F. DiMarzio, Android A Programmers Guide, McGraw-Hill Publication., 5. Ian F. Darwin, Android Cookbook, 2nd Edition, O'Reilly Media., 6. Dawn Griffiths, David Griffiths, Head First Android Development, 2nd Edition, O'Reilly, Media., 7. Vandad Nahavandipoor, iOS 10 Swift Programming Cookbook, O'Reilly Media., 8. Craig Clayton, iOS 10 Programming for Beginners, O'Reilly Media., 9. Dan Pilone, Tracey Pilone, Head First iPhone and iPad Development: A Learner's Guide to, Creating Objective-C Applications for the iPhone and iPad, 3rd Edition, O'Reilly Media., , 63
Page 64 :
CE601 Compiler Construction, Course Objectives and Outcomes:, • [CCCO1] To inform students about different parsing techniques, techniques to generate, intermediate code and different optimization techniques., • [CCCO2] To enrich the knowledge in various phases of compiler and its use., • [CCCO3] To introduce the concepts underlying the design and implementation of language, processors., • [CCCO4] To provide practical programming skills necessary for constructing a compiler., CO to PO Mapping:, PO1, CCCO1, , x, , CCCO4, , PO3, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , CCCO2, CCCO3, , PO2, , x, , x, , x, x, , x, , Unit I, Introduction to Compiling and Lexical Analysis: Definition, analysis of the source program, the, phases of a compiler, the grouping of phases, Compiler Construction tools, A simple one-pass compiler,, The role of the Lexical analyzer, Input buffering, Specification of Tokens, A Language for Specifying, Lexical Analyzers, Design of a Lexical Analyzer generator., Unit II, Syntax Analysis: The role of the Parser, Context-free grammars, Writing a Grammar, Top-Down, Parsing, Bottom- Up Parsing, Operator-precedence Parsing, LR-Parsers, Using Ambiguous Grammars,, Parser Generators., Syntax-Directed Translation: Definitions, Construction of Syntax Trees, Bottom-Up Evaluation of SAttributed definitions, Top-Down Translation, Bottom-Up Evaluation of Inherited attributes., Unit III, Intermediate Code Generation: Intermediate Languages, Declarations, Assignment Statements,, Boolean Expressions, Case Statements, Back patching, Procedure Calls., Unit IV, Code Generation: Issues in the Design of a Code Generator, The target Machine, Run-Time Storage, Management, Basic Blocks and Flow Graphs, Next-Use Information, Simple Code Generator, Register, allocation and Assignment, The DAG Representation of Basic Blocks, Generating Code from DAGs,, Dynamic Programming, Code-Generation Algorithm, Code-Generators., , 64
Page 65 :
Unit V, Code Optimization: Peephole Optimization, Principal sources of optimization, Introduction to Global, data flow analysis., Text Books:, 1. Aho, Sethi, Ullman, Compilers Principles, Techniques and Tools, Addison Wesley, 1987., 2. Hopcroft, Motwani and Ullman, Introduction to Automata Theory, Languages and, Computation, Pearson Publication., 3. Dick Grune, Kees van Reeuwijk, Henri E. Bal, Ceriel J. H. Jacobs and Koen Langendoen,, Modern Compiler Design, Wiley Publication., Reference Books:, 1. Paul G. Sorenson, Compiler Writing, McGraw-Hill Publication., 2. Hunter, The Essence of Compilers, Pearson Publication., 3. Lewis, Elements of the Theory of Computation, Pearson Publication., 4. Jean Paul Tremblay, Paul Gordon Sorenson, Theory and Practice of Compiler Writing, BS, Publications, 2008., 5. Ronald Mak, Writing Compilers and Interpreters: A Software Engineering Approach, 3rd, Edition, Wiley Publication., 6. Doug Brown, John Levine, Tony Mason, lex & yacc, 2nd Edition, O'Reilly Media., , 65
Page 66 :
CE602 Computer Networks, Course Objectives and Outcomes:, • [CNCO1] To develop an understanding of modern network architectures from a design and, performance perspective., • [CNCO2] Analyze the requirements for a given organizational structure and select the most, appropriate networking architecture and technologies., • [CNCO3] To study protocols, network standards, the OSI model, IP addressing, cabling,, networking components, and basic LAN design., • [CNCO4] Ability to write program using socket programming., CO to PO Mapping:, PO1, , PO2, , PO3, , PO4, , PO5, , x, , CNCO2, CNCO4, , PO7, x, , CNCO1, CNCO3, , PO6, , x, , PO8, , PO9, , PO10, x, , x, , x, , x, , x, , x, , Unit I, INTRODUCTION: Applications of computer networks, Network hardware, Network software:, Protocol Hierarchy, Design Issue, connection oriented versus connectionless, Service Primitives,, Reference models: OSI and TCP/IP, Example networks: Internet, Network standardization,, Performance: Bandwidth and Latency, Delay and bandwidth product, High-Speed Network,, Application Performance Needs., Unit II, PHYSICAL LAYER: X.25, Frame relay, ATM, Ethernet (802.3), FDDI, Token Rings, Resilient Packet, Rings, Wireless LANs: Wi-Fi (802.11), Cell Phone Technologies, Broadband Wireless: Wi-MAX, (802.16), Bluetooth (802.15.1), RFID., Unit III, DATA LINK LAYER Data Link Layer Design Issues: Service provided to network layer Framing,, Error Control, Flow Control, Error Detection and Correction: error correcting codes, error detecting, codes, Elementary Data Link Protocols: utopian Simplex Protocols, Stop-and-Wait Protocol, Sliding, Window Protocols: One-bit Sliding Window Protocol, Go-Back-N, Selective Repeat, Example Data, Link Protocols., Unit IV, MEDIUM ACCESS CONTROL SUB LAYER: The Channel Allocation Problem, Multiple Access, Protocols: ALOHA, CSMA, Collision-free protocol, Limitation Contention Protocol, Data Link Layer, Switching, What is frame? Why framing is needed?, Hardware Building Blocks, Different framing, 66
Page 67 :
techniques. Bit, byte and clock oriented Protocols: PPP, HDLC, DDCMP, Broadcast and Multicast., Unit V, NETWORK LAYER: Design issues, Connectionless and connection-oriented services, Virtual circuit, and datagram subnets, Routing algorithms, Interior and Exterior Gateway Routing Protocols., Congestion Control and QOS: General principles, Congestion prevention policies, Load shading,, Jitter control, Quality of service: Packet scheduling, Traffic shaping, integrated Services., Unit VI, SOCKET PROGRAMMING: Introduction to IP address, Port Addresses, What is Sockets?, (Barkley's Socket), socket address, Socket types, Client-Server Communication, System Calls used in, UNIX for client-server communication, Socket Program using JAVA.NET Class, TCP and UDP Socket, Programming., Text Books:, 1. A. Tanenbaum, Computer Networks, 4th Edition, PHI Publication., 2. B. Forouzan, Data Communications and Networking, 3rd Edition, McGraw Hill Publication,, 2004., 3. Computer Networks: A Systems Approach, Larry Peterson and Bruce Davie, Elsevier., Reference Books:, 1. S. Keshav, An Engineering Approach to Computer Networking, Pearson education., 2. D. Comer, Computer Networks and Internet, Pearson education., 3. M. Gallo, W. Hancock, Computer Communications and Networking Technologies, Course, Technology., 4. Natalia Olifer, Victor Olifer, Computer Networks: Principles, Technologies and Protocols for, Network Design, Wiley Publication., , 67
Page 68 :
CE603 Computer Graphics (Elective 601), Course Objectives and Outcomes:, • [CGCO1] To understand the basics of various inputs and output computer graphics hardware, devices., • [CGCO2] To provide students with a foundation in graphics applications programming., • [CGCO3] Ability to understand various graphics packages., • [CGCO4] Understand display, manipulation and storage of pictures and experimental data for, proper visualization using a computer., • [CGCO5] To know 2D raster graphics techniques, 3D modelling, geometric transformations,, 3D viewing and rendering., CO to PO Mapping:, PO1, CGCO1, , PO2, , PO3, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , CGCO2, , x, , CGCO3, , x, , x, , CGCO4, , x, , x, , x, , CGCO5, , x, , x, , x, , Unit I, Basic Concepts: Introduction to computer graphics, lines, line segments, pixels and frame buffers,, anti-aliasing techniques and character generation methods. Graphics Display devices (monochrome,, color) interactive devices, Scanners and digitizers, touch panels, tablets, mouse, joysticks, trackball,, light pen., Unit II, 2-D Transformation: Line and circle plotting using Breshemham’s and other algorithms,, transformation matrices, scaling, rotation, translation, picture transformation, mirror image., Window and Clipping: Introduction, viewing transforms, 2-D clipping, Sutherland Cohen approach,, Cyrus Beck Method, Midpoint subdivision algorithm, Liang-Barsky line clipping algorithm, polygon, clipping, text clipping, generalized clipping., Unit III, 3-D Graphics: Introduction, 3-D geometry, Co-ordination system, 3D transformation , rotation about, an arbitrary axis, orthogonal projections, multiple views, isomeric projection, perspective projections,, 3-D clipping., Unit IV, 68
Page 69 :
Hidden Surfaces and Lines: Introduction, Back face removal algorithm, Z-buffers, Scan line and, Painters algorithm hidden surface removal, curved surface generation, generation of solids, sweep, method, interpolation., Unit V, Graphical User Interface: X-Windows, use of graphics tools like OPENGL, DirectX, Windows and, Motif, Graphic Standards., Animation: Introduction, devices for producing animation, computer assisted animation, real time, animation, method for controlling animation (fully explicit control, procedural)., Text Books:, 1. Peter Shirley, Michael Ashikhmin, Steve Marschner, Fundamental Of Computer Graphics, 4th, Edition, CRC Press., 2. Newman, Sprouall, Interactive Computer Graphics, McGraw-Hill Publication., 3. Hearn, Baker, Computer Graphics, PHI Publication., 4. Krishnamurthy, Introduction to Computer Graphics, McGraw-Hill Publication., 5. ISRD Group, Computer Graphics, McGraw-Hill Publication., Reference Books:, 1. Harrington, Computer Graphics, McGraw Hill Publication., 2. Rogers, Procedural Elements of Computer Graphics, McGraw Hill Publication., , 69
Page 70 :
CE603 Database Implementation Techniques (Elective 601), Course Objectives and Outcomes:, • [DTCO1] To provide the students with a better understanding of the essential techniques used in, Database Management System, either by revisiting them or by studying new approaches., • [DTCO2] To understand the different database models and language queries to access, databases., • [DTCO3] To protect the data and the database from unauthorized access and manipulation., • [DTCO4] To handle large concurrent operations., CO to PO Mapping:, PO1, DTCO1, DTCO2, , PO2, , PO3, , PO4, , x, , PO6, , PO7, , PO8, , PO9, , x, x, , x, , PO10, x, , x, x, , DTCO3, DTCO4, , PO5, , x, , x, , Transaction: Transaction Concept, Transaction Model, Storage Structure, Transaction Atomicity and, Durability, Transaction Isolation, Serializability, Transaction Isolation and Atomicity, Transaction, Isolation Levels, Implementing Isolation Levels, Transaction as SQL Statements., Concurrency Control: Lock Based Protocols, Deadlock Handling, Multiple Granularity, Time-Stamp, Based Protocols, Validation Based Protocols, Multi-Version Schemes, Insert-delete Operations and, Predicate Reads., Recovery System: Failure Classification, Storage, Recovery and Atomicity, Recovery Algorithm,, Buffer Management, Failure with Loss of Non Volatile Storage, Early Lock Release and Logical Undo, Operations, Remote Backup Systems., Database System Architectures and Parallel Databases: Centralized and Client Sever Architecture,, Server System Architectures, Parallel Systems, Distributed Systems. Introduction to Parallel Databases,, Inter-Query and Intraquery Parallelism, Intraoperation and Inter-Operation Parallelism, Query, Optimization, Parallelism on Multi-Core Processors, Design of Parallel System., Distributed Database: Homogeneous and Heterogeneous Databases, Distributed Data Storage,, Distributed Transactions, Commit Protocols, Concurrency Control In Distributed Environment,, Distributed Query Processing, Heterogeneous Distributed Databases, Cloud Based Databases., Dataware Housing and Data Mining: Decision support systems, Dataware Housing, Data Mining,, Classification, Association Rules, Other Types of Associations, Clustering, Other Forms of Data, 70
Page 72 :
CE604 Human Computer Interface (Elective 602), Course Objectives and Outcomes:, • [HCCO1] Demonstrate an understanding of guidelines, principles, and theories influencing, human computer interaction., • [HCCO2] Describe the key design principles for user interfaces., • [HCCO3] Carry out the steps of experimental design, usability and experimental testing, and, evaluation of human computer interaction systems., • [HCCO4] Develop and implement a process to gather requirements for, engage in iterative, design of, and evaluate the usability of a user interface., CO to PO Mapping:, PO1, HCCO1, , PO2, , PO3, , PO5, , PO6, , x, , x, , PO7, , PO8, , PO9, , PO10, , x, , HCCO2, , x, , HCCO3, , x, , HCCO4, , PO4, , x, x, , x, x, , x, , Unit I, Introduction: Course objective and overview, Historical evolution of the field, The Human, The, Computer, The Interaction., Design processes: Interaction Design basics, Concept of usability – definition and elaboration, HCI in, the Software Process, Design Rules., Unit II, Implementation and Evaluation: Implementation Support, Evaluation Techniques, Universal Design,, Use Support., Unit III, Models: Cognitive Models, Socio – Organizational Issues and Stakeholders Requirements,, Communication and Collaboration models., Theories: Task Analysis Dialog notations and Design Models of the system Modeling Rich, Interactions., Unit IV, Modern Systems: Group ware, Ubiquitous Computing computing and Augmented Realities Hypertext, Multimedia and World Wide web., , 72
Page 73 :
Text Books:, 1. Alan Dix, Janet Finlay, Gregory Abowd, Russell Beale, Human Computer Interaction, 3rd, Edition Pearson Education., 2. Preece J., Rogers Y., Sharp H., Baniyon D., Holland S. and Carey T., Human Computer, Interaction, Addison-Wesley, 1994., 3. B. Shneiderman, Designing the User Interface, Addison Wesley 2000 (Indian Reprint)., Reference Books:, 1. Jenny Preece, Helen Sharp, Yvonne Rogers, Interaction Design: Beyond Human-Computer, Interaction, 4th Edition, Wiley Publication., 2. Gerard Jounghyun Kim, Human–Computer Interaction: Fundamentals and Practice, CRC, Press., 3. Jenifer Tidwell, Designing Interfaces 2nd Edition, Patterns for Effective Interaction Design,, O'Reilly Media., , 73
Page 74 :
CE604 Real-Time System (Elective 602), Course Objectives And Outcomes:, • [RTCO1] To study issues related to the design and analysis of systems with real-time, constraints., • [RTCO2] Appreciation of the need for integrated mechanism for resource allocation and, scheduling., • [RTCO3] To study the difference between traditional and real time databases., • [RTCO4] To learn about various real time communication protocols., CO to PO Mapping:, PO1, RTCO1, , RTCO4, , PO3, , PO4, , PO5, , PO6, , PO7, , PO8, , x, , PO9, , PO10, x, , x, , RTCO2, RTCO3, , PO2, , x, , x, x, , x, , x, , Unit I, Introduction: What is Real Time System?, Application of Real Time System, A Basic Model of Real, Time System, Characteristics of Real Time System, Safety and Reliability, Types of Real-Time Tasks,, Timing Constraints, Modelling Timing Constraints., Unit II, Real-Time Task Scheduling: Concept, Types of real time task and their characteristics, Task, scheduling, Clock-Driven Scheduling, Hybrid Schedulers, Event-driven scheduling, EDF scheduling,, Rate monotonic System, Issue associate with RMA, Issue in using RMA in practical situations., Unit III, Handling Resource Sharing and Dependencies Among Real-Time Tasks: Resource Sharing Among, Real-time Tasks, Priority Inversion, Priority Inheritance Protocol (PIP), Higher Locker Protocol (HLP),, Priority Ceiling Protocol (PCP), Difference types of Priority Inversion under PCP, Important features of, PCP, Some issues in Using A Resource Sharing Protocol., Unit IV, Scheduling Real-Time Tasks in Multiprocessor and Distributed Systems: Multiprocessor task, Allocation, Dynamic Allocation of Tasks, Fault Tolerant Scheduling of Tasks, Clocks in Distributed, Real Time Systems, Centralized Clock Synchronization, Distributed Clock Synchronization., Commercial Real-Time Operating Systems: Time Services, Features of Real Time Operating, System, Unix as a Real Time Operating System, UNIX-based Real-Time Operating System, Windows, as a Real-Time Operating System, POSIX, A Survey of contemporary Real-Time Operating System,, 74
Page 75 :
Benchmarking Real-Time System., Unit V, Real-Time Communication: Examples of Real-Time Communication in Applications, Basic, Concepts, Real-Time Communication in LAN, Soft Real-Time Communication in LAN, Hard, Real-Time Communication in LAN, Bounded Access Protocol, Performance Comparison, Real-Time, Communication over Internet, Routing, Multi-cast Routing, Resource Reservation, Traffic Shaping and, Policing, Scheduling Mechanism, QoS Models., Real-Time Databases: Examples applications of Real-Time Databases, Review of Basic Database, Concepts, Real-Time Databases, Real-Time Databases Application Design Issues, Characteristics of, Temporal Data, Concurrency Control in Real-Time Databases, Commercial Real-Time Databases., Text Books:, 1. Rajib Mall, "Real-Time Systems: Theory and Practice", Pearson Publication, 2008., 2. Jane W. Liu, "Real-Time Systems", Pearson Education, 2001., 3. Krishna and Shin, "Real-TIme Systems", McGraw Hill Publication, 1999., Reference Books:, 1. Alan C. Shaw, Real-Time Systems and Software, Wiley, 2001., 2. Philip Laplante, Real-Time Systems Design and Analysis, 2nd Edition, Prentice Hall of India., , 75
Page 76 :
CE605 Bio-Metrics (Elective 603), Course Objectives And Outcomes:, • [BMCO1] Design and working of a generic biometric system., • [BMCO2] The features used to represent and match individual biometric traits., • [BMCO3] The performance metrics used to evaluate a biometric system., • [BMCO4] To learn and implement some of the biometrics authentication., CO to PO Mapping:, , BMCO1, , PO1, , PO2, , PO3, , x, , x, , x, x, , BMCO2, , PO5, , PO6, , PO7, , PO8, , PO9, , x, , x, , x, , x, , x, , PO10, , x, , BMCO3, BMCO4, , PO4, , x, , x, , Introduction of bio-metric traits and its aim, Image processing/pattern recognition/statistics, Error, types. Image processing basic: what is image, acquisition, type, point operations, Geometric, transformations. Linear interpolation, brightness correction, histogram, Fourier Series, DFT, inverse of, DFT., Basic image operations: Convolution, linear/non-linear filtering, Gaussian, Median, Min, gray level, reduction. Special filters, enhancement filter, Edge detection, derivatives, Laplacian, unsharp masking,, high boot filtering, sharpening special filtering, Edge detection., First and second derivative, steps in edge detection, smoothening, enhancement, threshold, localization,, Robert's method, Sobal's method, Pervitt and sobal, Laplacian of Gaussian, Zero crossing. Canny edge, detection, Fourier Series, DFT, inverse of DFT. Bio-metric system, authentication, physiological and, behavioral properties, properties of bio-metric system, application areas. Identification/verification,, Threshold, Score distribution, FAR/FRR, System design issues., Positive/negative identification, Bio-metric system security, Authentication protocols, Authentication, methods. Matching, null and alternative hypothesis h0, h1, Error type I/II, Matching score distribution,, FM/FNM, ROC curve, DET curve, FAR/FRR curve. Comparing two systems using ROC curve,, Expected overall error, EER, available best error rates, cost function, bio-metric myths and, misrepresentations, negative authentication, trade-offs between security and convenience. Selection of, suitable bio-metric, Bio-metric attributes, Zephyr charts, types of multi bio-metrics., Verification on multi-model system, normalization strategy, Fusion methods, Multi-model, identification, Bio-metric system security. Bio-metric system vulnerabilities, circumvention, covert, acquisition, quality control, template generation, interoperability, data storage. Signature recognition, system, cropping, enhancement, signature parameters, matching and decision, recognition., 76
Page 78 :
CE605 Operating System Design (Elective 603), Course Objectives And Outcomes:, • [ODCO1] To understand key mechanisms in design of operating systems modules., •, •, , [ODCO2] To use modern operating system calls such as Linux process and synchronization, libraries., [ODCO3] Gain some practical experience with systems programming and tools., , •, , [ODCO4] Write systems level programs and scripts., , CO to PO Mapping:, PO1, , PO2, , ODCO1, , x, , x, , ODCO2, , x, , PO3, , PO4, , PO5, , PO6, , PO7, , x, , x, , PO8, , PO9, , PO10, x, x, , ODCO3, , x, , ODCO4, , x, , x, x, , x, , x, , x, , General Overview Of The System: History, System Structure, User Perspective, Operating System, Services, Assumptions About Hardware., Introduction To The Kernel: Architecture Of The Unix Operating System, Introduction To System, Concepts, Kernel Data Structures, System Administration., The Buffer Cache: Buffer Headers, Structure Of The Buffer Pool, Scenarios For Retrieval Of A, Buffer, Reading And Writing Disk Blocks, Advantages And Disadvantages Of The Buffer Cache., Internal Representation Of Files: Inodes, Structure Of A Regular File, Directories, Conversion Of A, Path Name To An Inode, Super Block, Inode Assignment To A New File, Allocation Of Disk Blocks,, Other File Types., System Calls For The File System: Open, Read, Write, File And Record Locking, Adjusting The, Position Of File I/O LSEEK, Close, File Creation, Creation Of Special Files, Change Directory And, Change Root, Change Owner And Change Mode, STAT And FSTAT, Pipes, Dup, Mounting And, Unmounting File Systems, Link, Unlink, File System Abstractions, File System Maintenance., The Structure Of Processes: Process States And Transitions, Layout Of System Memory, The Context, Of A Process, Saving The Context Of A Process, Manipulation Of The Process Address Space, Sleep., Process Control: Process Creation, Signals, Process Termination, Awaiting Process Termination,, Invoking Other Programs, The User Id Of A Process, Changing The Size Of A Process, The Shell,, System Boot And The Init Process., 78
Page 79 :
Process Scheduling And Time: Process Scheduling, System Calls For Time, Clock., Memory Management Policies: Swapping, Demand Paging, A Hybrid System With Swapping And, Demand Paging., The I/0 Subsystem: Driver Interfaces, Disk Drivers, Terminal Drivers, Stream., Interprocess Communication: Process Tracing, System V IPC, Network Communications, Sockets., Reference Books:, 1. The Design of The UNIX Operating System, Maurice J. Bach, PHI Publication., 2. Operating Systems: Design and Implementation, Tanenbaum, Andrew, Prentice Hall, 1997., 3. Thomas W. Doeppner, Operating System in Depth: Design and Programming, Wiley, Publication., 4. William Stalling, “Operating System: Internals and Design Principles”, 4th Edition Prentice, Hall, 2005., , 79
Page 80 :
CE606 Computer Network Laboratory, 1. Study of router and other inter-networking devices., 2. Implementation of UTP cables-cross over, straight through, roll over., 3. Implementation of basic Client Server program using TCP Socket (e.g. Day time server and, client)., 4. Implementation of basic Client Server program using UDP Socket., 5. Implementing a program with TCP Server and UDP Client., 6. Implementation of TCP Client Server program with concurrent connection from clients., 7. Implementing fully concurrent application with a TCP server acting as a directory server and, client programs allowing concurrent connection and message transfer (e.g. Chat system)., 8. Experiments with open source firewall/proxy packages like iptables, squid etc., 9. Experiments with Emulator like Netkit, Emulab etc., 10. Experiments with Simulator like NS2, NCTU NS etc., , CE607 Compiler Construction Laboratory, 1. LEX and YACC – Generation of Intermediate Code for Expression Grammar – Construction, of Predictive Parsing Table – LR Parsing Tables – Parsing Actions., 2. Implement CYK algorithm (from Motwani’s book)., 3. Using LEX/YACC tools generate assembly language code for a block of assignment and, arithmetic statements., 4. Implement elimination of left recursion and left factoring algorithms for any given grammar, and generate predictive parsing table., 5. Write a program for generating a parser program using LEX and YACC for a language with, integer identifiers, binary arithmetic expressions and assignments. (Input is grammar and, output is parser in C language)., 6. Write a program for generating SLR Parsing table and also write a parser., 7. Write a program for generating derivation sequence for a given terminal string using parsing, table., 8. Using back–patching method generate three address code for while, if and Boolean, expressions., , 80
Page 81 :
CE608 System Administration, 1. Installations of various Linux flavors (Optionally using Virtualbox): Centos (with LVM, without, LVM), Ubuntu (with LVM, without LVM), Debian (with LVM, without LVM), 2. SSH Server (CentOS and Ubuntu): enable/disable root login, 3. Telnet server (CentOS and Ubuntu), 4. FTP Server (CentOS and Ubuntu), 5. Using command upload/download files from FTP Server, 6. Samba Server (CentOS and Ubuntu), 7. Http Server (CentOS and Ubuntu), 8. Configuration of Proxy Server, Reference Books:, 1. Tom Adelstein, Bill Lubanovic, Linux System Administration: Solve Real-life Linux Problems, Quickly, O'Reilly Media., 2. Æleen Frisch, Essential System Administration, Third Edition, O'Reilly Media., 3. Terry Collings, Kurt Wall, Red Hat Linux Networking and System Administration, 3rd Edition,, Wiley Publication., , 81
Page 82 :
CE701 Software Engineering, Course Objectives and Outcomes:, • [SECO1] To understand the Software Engineering Practice & Process Models., • [SECO2] To understand Design Engineering, Web applications, and Software Project, Management., • [SECO3] An understanding of some ethical and professional issues that are important for, software engineers., • [SECO4] To develop an ability to look at the Computer Science discipline from Software, Engineering Systems perspective., CO to PO Mapping:, PO1, , PO2, , PO3, , SECO1, , x, , x, , SECO2, , x, , x, , SECO3, , x, , SECO4, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, x, , x, x, , x, , Unit I, Software Engineering and The Software Process: Introduction, Process models., Modeling Part-I: Principles that guide practice, Understanding Requirements, Requirements, modeling: Scenarios, Information, and analysis classes, Requirements modeling: Flow, Behavior,, Patterns, and web applications., Unit II, Modeling Part-II: Design concepts, Architectural design, Component level design, User interface, design, Pattern based design, Web page design., Quality Management: Quality concepts, Review techniques, Software quality assurance, Software, testing strategies, Testing conventional applications., Unit III, Quality Management Part-II: Testing Object-Oriented applications, Testing web applications,, Software configuration management, Product metrics., Unit IV, Managing Software projects: Project management concepts, Process and project Metrics, Estimation, for software projects, Project scheduling, Risk management, Maintenance and re-engineering., , 82
Page 83 :
Text Books:, 1. Roger Pressman, Software Engineering: A Practitioners Approach, 7th Edition, McGraw Hill, Publication., 2. Jalota Pankaj, An Integrated Approach to Software Engineering, 3rd Edition, Narosa, Publication., 3. Rod Stephens, Beginning Software Engineering, Wiley Publication., 4. Shailesh Mehta, Project Management and Tools & Technologies – An overview, SPD, Publication., Reference Books:, 1. Jawadekar, Software Engineering, 5th Edition, McGraw-Hill Publication., 2. Sommerville, Software Engineering, 7th Edition, Pearson Education, 2007., 3. Hans van Vliet, Software Engineering: Principles and Practice, 3rd Edition, Wiley Publication., , 83
Page 84 :
CE702 Artificial Intelligence, Course Objectives and Outcomes:, • [AICO1] To understand the notions of rational behavior and intelligent agents., • [AICO2] To develop a general appreciation of the goals, subareas, achievements and difficulties, of AI., • [AICO3] To provide the knowledge of methods of blind as well as informed search and ability, to practically apply the corresponding techniques., • [AICO4] To develop general understanding of major concepts and approaches in knowledge, representation, planning, learning, robotics and other AI areas., • [AICO5] To developing programming skills for AI applications & exposure to logic, programming with Prolog., CO to PO Mapping:, , AICO1, , PO1, , PO2, , PO3, , x, , x, , x, , PO5, , PO6, , x, , x, , x, , x, , x, , PO7, , PO8, , PO9, , PO10, , x, , AICO2, AICO3, , x, , AICO4, , x, , AICO5, , PO4, , x, x, , x, x, , Unit I, Introduction: Definition of A.I, Foundation of A.I., History, intelligent Agents, Agent Architecture,, A.I. A.I. Representation, Properties of internal representation, Futures of A.I, A.I Techniques,, Importance of A.I – Representation of Knowledge, Knowledge Base Systems, State Space Search –, Production Systems – Problem Characteristics., Unit II, Heuristics Search Techniques: Generate and test – Hill Climbing, Depth First Search, Breadth First, Search, Best First Search, A* and AO* Algorithm, Problem reduction – Constraint satisfaction –, Means-Ends Analysis. Game playing – Minimax and Alpha-Beta Cutoffs, waiting for Quiescence,, Secondary search., Unit III, Predicate Logic: Using predicate logic, Predicate Calculus, Predicate and arguments, ISA Hierarchy,, Frame notation, Resolution, Natural Deduction representing simple facts in Logic – Logic, Programming, computable functions in predicates, resolution – unification, Forward and Backward, reasoning, Forward and Backward chaining rules., Unit IV, 84
Page 85 :
Structured Knowledge Representation: TMS (Truth maintenance system),Statistical and, probabilistic reasoning, Associative Networks, Semantic Nets, Frames Structures, Conceptual, Dependencies and Scripts Learning – Concept of Learning – Learning Automata, Genetic Algorithm,, Learning by induction, Planning: Block world, strips, Implementation using goal stack, Non linear, planning with goal stacks, Hierarchical planning, least commitment strategy., Unit V, Natural Language Processing: Overview of Linguistics, Grammars and Languages, basic Parsing, techniques, Semantic analysis and representation structures. Natural Language generation and Natural, Language Systems. Syntactic Processing, ATN, RTN., Unit VI, Expert Systems: Architecture – Need and Justification of Expert Systems – knowledge representation,, Knowledge acquisition and validation. Utilization and functionality, Perception and Action, real time, search, perception, action, vision, robot architecture, Basics of PROLOG., Text Books:, 1. Eugene, Charniak, Drew Mcdermott, "Introduction to artificial intelligence", Addison Wesley,, 1985., 2. Eiaine Rich and Kerin Knight, "Artificial Intelligence", McGraw-Hill, Second Edition., 3. Anindita Das Bhattacharjee, Artificial Intelligence and Soft Computing for Beginners, 2nd, Edition, SPD Publication., Reference Books:, 1. Stuart Russell and Peter Nerving, "Artificial Intelligence: A Modern Approach", Prentice Hall,, 2nd Edition., 2. Ivan Bratko, "Prolog Programming For Artificial Intelligence", 2nd Edition Addison Wesley,, 1990., 3. Herbert A. Simon, "The Sciences of the Artificial ", MIT Press, 3rd Edition (2nd Printing), 1995., 4. Tim Jones, "Artificial Intelligence Application Programming", Dreamtech Publication., , 85
Page 86 :
CE703 Internetworking Protocol, Course Objectives and Outcomes:, • [IPCO1] To gain comprehensive knowledge about the layered communication architectures., • [IPCO2] To understand the principles, key protocols, design issues, and significance of each, layers in TCP/IP., • [IPCO3] To gain comprehensive knowledge about the layered communication architectures in, TCP/IP and its functionalities., CO to PO Mapping:, PO1, IPCO1, , x, x, , PO3, , PO4, , PO5, , PO6, , PO7, , x, x, , IPCO2, IPCO3, , PO2, , x, , PO8, , PO9, , PO10, x, , x, , x, , x, , x, , x, , x, , Unit I, Review of Networking Technologies and Inter-networking Concepts and Architectural Model:, Application level and network level interconnection, Properties of the Internet, Internet architecture,, Interconnection through IP routers., Unit II, Internet Addresses, Mapping Internet Addresses to Physical Addresses (ARP) & Determining an, Internet Addresses at Startup (RARP): Universal identifiers, Three primary classes of IP addresses,, Network and broadcast addresses, Limited broadcast, Dotted decimal notation, Weakness in Internet, addressing, Loop-back addresses, Address resolution problem, Two types of physical addresses,, Resolution through direct mapping, Resolution through dynamic binding, Address resolution cache,, ARP to other protocols, Reverse address resolution protocol, Timing RARP transaction, Primary and, backup RARP servers., Unit III, Internet Protocol Connectionless Datagram Delivery and Internet Protocol: Routing IP Datagram: The, concepts of unreliable delivery, Connectionless delivery system, Purpose of the Internet protocol, The, Internet datagram, Routing in an Internet, Direct and indirect delivery, Table driven IP routing, Next, hop routing, Default routes, Host specific routes, The IP routing algorithm, Handling incoming, datagrams, Establishing routing tables., Unit IV, Internet Protocol Error and Control Message (ICMP) and Subnet and Supernet Address Extension:, The Internet, Control message protocols, Error reporting versus error detection, ICMP message format,, Detecting and reporting various network problems through ICMP, Transparent router, Proxy ARP,, Subnet addressing, Implementation of subnets with masks representation, Routing in the presence of, 86
Page 87 :
subnets, A unified algorithm., Unit V, User Datagram Protocol (UDP): Format of UDP message, UDP pseudo header, UDP encapsulation, and protocols layering and the UDP checksum computation, UDP multiplexing, De-multiplexing and, ports., Reliable Stream Transport Service (TCP): The transmission control protocol, Ports, Connections and, endpoint, Passive and active opens, The TCP segment format, TCP implementation issues., Unit VI, Application Layer World Wide Web, Real-time Audio and Video, Content Delivery and Peer-To-Peer,, SMTP and HTTP Protocol, Domain name systems (DNS), and DNS server, Electronic mail architecture, and services, Message formats, MIME, message transfer, SMTP, Mail gateways, Relays, Configuration, mail servers, File transfer protocol, General model commands, TFTP., Text Books:, 1. Douglas E. Comer, Inter-networking with TCP/IP: Principles, Protocols and Architecture, PHI, Publication., 2. Behrouz A. Forouzan, TCP-IP Protocol Suite, McGraw Hill Publication., Reference Books:, 1. Unix Network Programming Interprocess Communications, W. Richard Stevens, PHI, Publication., 2. William Stalling, SNMP SNMPv2, SNMPv3, and RMON 1 and 2, Pearson Education., 3. Hunt Craig, TCP-IP Network Administration, O'Reilly Media., 4. D. Comer, Computer Networks and Internet, Pearson education., 5. Natalia Olifer, Victor Olifer, Computer Networks: Principles, Technologies and Protocols for, Network Design, Wiley Publication., , 87
Page 88 :
CE704 Distributed System (Elective 701), Course Objectives and Outcomes:, • [DSCO1] To learn the principles, architectures, algorithms and programming models used in, distributed systems., • [DSCO2] Ability to write distributed programs using sockets, RPC/RMI, etc., • [DSCO3] Appreciation of the differences in the handling of issues like mutual exclusion,, deadlock detection, fault handling, etc. in a centralized system and a distributed system., • [DSCO4] To gain experience in the application of fundamental Computer Science methods and, algorithms in the development of distributed systems and distributed systems applications., CO to PO Mapping:, PO1, , PO2, x, , DSCO2, DSCO4, , PO4, , PO5, , PO6, , PO7, , x, , DSCO1, DSCO3, , PO3, x, x, , PO9, , PO10, x, , x, , x, x, , PO8, , x, , x, , x, , x, , x, , Unit I, Introduction: Introduction to Distributed Computing System, Evolution of Distributed Computing, System, Distributed Computing System models, Distributed Computing System Gaining Popularity,, Distributed Operating System, Introduction to Distributed Computing Environment (DCE), network, Types, LAN Technologies, WAN technologies, Communication Protocols, Inter-networking, ATM, Technology, Desirable Features of a Good Message- Passing System, Issues in IPC by MessagePassing, Synchronization, Buffering, Multi-datagram message, Encoding and Decoding of message, data, Process addressing, Failure Handling, Group Communication, Case Study: BSD UNIX IPC, Mechanism., Unit II, Remote Procedure Calls: Introduction, the RPC model, Transparency of RPC, Implementing RPC, Mechanism, Stub Generation, RPC messages, Marshaling arguments and Results, Server Management,, Parameter Passing Semantics, Call Semantics, Communication Protocols for RPCs, Complicated RPCs,, Client- Server Binding, Exception Handling, Security, Some Special Types of RPCs, RPC in, Heterogeneous Environments, Lightweight RPC, Optimization for Better Performance, Case studies:, Sun RPC, DCE, RPC., Unit III, Distributed Shared Memory: Introduction, general Architecture of DSM Systems, Design and, Implementation Issues of DSM, Granularity, Structure of Shared Memory Space, Consistency Models,, Replacement Strategy, Thrashing, Other Approaches to DSM, Heterogeneous DSM, Advantages of, DSM., 88
Page 89 :
Synchronization: Introduction, Clock Synchronization, Event Ordering, Mutual Exclusion, Deadlock,, Election Algorithms., Unit IV, Resource Management And Process Management: Introduction, Desirable Features of a Good, Global Scheduling Algorithm, Task assignment Approach, Load-Balancing Approach, load Sharing, Approach, Process Migration, Threads., Distributed File System: Introduction, Desirable Features of a Good Distributed File System, File, Models, File Accessing Models, File Sharing Semantics, File Caching Schemes, File Replication, Fault, Tolerance, Atomic Transactions, Design Principles, Case Study: DCE Distributed File Service., Text Books:, 1. P. K. Sinha, Distributed Operating System, PHI Publication., 2. Colorouis, Distributed Systems, Addison Wesley Publication., 3. M. L. Liu. Distributed Computing: Principles and Applications, Addison-Wesley, 2004., Reference Books:, 1. Tanabaum, Distributed Systems, PHI Publication., 2. Arun Kulkarni, Nupur Prasad Giri, Nikhilesh Joshi, Bhushan Jadhav, Parallel and Distributed, Systems, Wiley Publication., 3. Ajay D. Kshemkalyani and Mukesh Singhal, Distributed Computing: Principles, Algorithms,, and Systems, Cambridge University Press, 2008., 4. Joel M. Crichlow, The Essence of Distributed Systems, Pearson Education Limited, 2000., , 89
Page 90 :
CE704 Cloud Computing (Elective 701), Course Objectives and Outcomes:, • [CLCO1] Understand various basic concepts related to cloud computing technologies., • [CLCO2] To demonstrate an understanding of Service models, deployment models,, Virtualization., • [CLCO3] Understand different cloud programming platforms and tools., • [CLCO4] Create application by utilizing cloud platforms such as Google app Engine and, Amazon Web Services (AWS), • [CLCO5] Be familiar with cloud programming using Google’s ‘Go’ programming language., CO to PO Mapping:, PO1, CLCO1, , x, , CLCO2, , x, , CLCO3, , x, , PO3, , x, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , x, , x, , x, x, , CLCO4, CLCO5, , PO2, , x, x, , x, , x, x, , x, , Unit I, Overview of Distributed Computing, Cluster Computing and Grid Computing – Technologies for, Network based systems – Software environments for Distributed Systems and Clouds – Overview of, Services and Service oriented Architecture, Motivation for cloud computing, Cloud Computing, principles., Unit II, Virtual Machines and Virtualization–Implementation levels of Virtualization–Virtualization, structures/tools and Mechanisms–Virtualization of CPU, Memory and I/O Devices–Storage, Virtualization. Cloud system architectures, Delivery models – infrastructure-as-a-service,, platform-as-a-service and software-as-a-service, Types of Clouds – public, private and hybrid clouds,, Infrastructure and Data storage Management, Architecture and design of storage and compute clouds., Unit III, Authentication, Authorization and Accounting, Cloud Security, privacy, policy and compliance, Cloud, reliability, disaster recovery and fault-tolerance, Cloud Economics – Metering, Monitoring and Pricing,, Viability of Cloud., Unit IV, Cloud programming frameworks, cloud interfaces, Interoperability and standards, Case studies such as, Amazon Web Services, Windows Azure and Google AppEngine., 90
Page 91 :
Text Books:, 1. Kai Hwang, Geoffrey C. Fox and Jack J. Dongarra, “Distributed and Cloud Computing from, Parallel Processing to the Internet of Things”, Morgan Kaufmann, Elsevier, 2012., 2. Antohy T Velte, Cloud Computing: A Practical Approach, McGraw Hill., Reference Books:, 1. Tim Mather, Subra Kumaraswamy, and Shahed Latif, “Cloud Security and Privacy An, Enterprise Perspective on Risks and Compliance”, O'Reilly 2009., 2. John W. Rittinghouse, James F. Ransome, Cloud Computing: Implementation, Management,, and Security, CRC Press., 3. Barrie Sosinsky, “Cloud Computing Bible” John Wiley & Sons, 2010., 4. Buyya R., Broberg J., Goscinski A. M., Cloud Computing – Principles and Paradigms, Wiley, Publication., , 91
Page 92 :
CE705 Computer Vision (Elective 702), Course Objectives and Outcomes:, • [CVCO1] Be familiar with both the theoretical and practical aspects of computing with images., • [CVCO2] Understand the geometric relationships between 2D images and the 3D world., • [CVCO3] Developed the practical skills necessary to build computer vision applications., • [CVCO5] Analyze and evaluate critically the building and integration of computer vision, algorithms and systems., CO to PO Mapping:, PO1, CVCO1, , x, , CVCO2, , x, , PO2, , PO3, , PO4, , PO5, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, , CVCO3, , x, , CVCO4, , x, , x, , x, , x, , x, , Unit I, Digital Image Formation and low-level processing: Overview and State-of-the-art, Fundamentals of, Image Formation, Transformation: Orthogonal, Euclidean, Affine, Projective, etc; Fourier Transform,, Convolution and Filtering, Image Enhancement, Restoration, Histogram Processing., Depth estimation and Multi-camera views: Perspective, Binocular Stereopsis: Camera and Epipolar, Geometry; Homography, Rectification, DLT, RANSAC, 3-D reconstruction framework;, Auto-calibration., Unit II, Feature Extraction: Edges – Canny, LOG, DOG; Line detectors (Hough Transform), Corners – Harris, and Hessian Affine, Orientation Histogram, SIFT, SURF, HOG, GLOH, Scale-Space Analysis- Image, Pyramids and Gaussian derivative filters, Gabor Filters and DWT., Unit III, Image Segmentation: Region Growing, Edge Based approaches to segmentation, Graph-Cut,, Mean-Shift, MRFs, Texture Segmentation; Object detection., Pattern Analysis: Clustering: K-Means, K-Medoids, Mixture of Gaussians, Classification:, Discriminant Function, Supervised, Un-supervised, Semi-supervised; Classifiers: Bayes, KNN, ANN, models; Dimensionality Reduction: PCA, LDA, ICA; Non-parametric methods., Unit IV, Motion Analysis: Background Subtraction and Modeling, Optical Flow, KLT, Spatio-Temporal, Analysis, Dynamic Stereo; Motion parameter estimation., , 92
Page 93 :
Shape from X: Light at Surfaces; Phong Model; Reflectance Map; Albedo estimation; Photometric, Stereo; Use of Surface Smoothness Constraint; Shape from Texture, color, motion and edges., Unit V, Miscellaneous: Applications: CBIR, CBVR, Activity Recognition, computational photography,, Biometrics, stitching and document processing; Modern trends – super-resolution; GPU, Augmented, Reality; cognitive models, fusion and SR&CS., Text Books:, 1. Richard Szeliski, Computer Vision: Algorithms and Applications, Springer – Verlag London, Limited 2011., 2. Computer Vision: A Modern Approach, D. A. Forsyth, J. Ponce, Pearson Education, 2003., 3. Kurt Demaagd, Anthony Oliver, Nathan Oostendorp, Katherine Scott, Practical Computer, Vision with SimpleCV: The Simple Way to Make Technology See, O'Reilly Media., Reference Books:, 1. Richard Hartley and Andrew Zisserman, Multiple View Geometry in Computer Vision, Second, Edition, Cambridge University Press, March 2004., 2. K. Fukunaga, Introduction to Statistical Pattern Recognition, Second Edition, Academic Press,, Morgan Kaufmann, 1990., 3. R.C. Gonzalez and R.E. Woods, Digital Image Processing, Addison- Wesley, 1992., , 93
Page 94 :
CE705 Natural Language Processing (Elective 702), Course Objectives and Outcomes:, • [NLCO1] To understand the application of computational methods in linguists., • [NLCO2] To apply statistical and probabilistic methods for parameter estimation and inference., • [NLCO3] Apply various important tasks in natural language processing such as language, modeling, information extraction, named entity recognition, information retrieval, text, classification, word sense disambiguation, automatic question answering and text, summarization., • [NLCO4] Use natural language processing (NLP) tools and libraries (such as python, nltk) and, develop software for various NLP tasks such as tagging, parsing and text classification., CO to PO Mapping:, PO1, NLCO1, , PO2, , x, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , NLCO2, , x, , NLCO3, , x, , NLCO4, , PO3, , x, x, , x, , x, , x, , x, , x, , Unit I, Introduction, Machine Learning and NLP, ArgMax Computation, WSD: WordNet, Wordnet;, Application in Query Expansion, Wiktionary; Semantic relatedness, Measures of WordNet Similarity,, Similarity Measures, Resnick's work on WordNet Similarity, Parsing Algorithms, Evidence for Deeper, Structure., Unit II, Top Down Parsing Algorithms, Noun Structure; Top Down Parsing Algorithms, Non-noun Structure, and Parsing Algorithms, Probabilistic parsing; sequence labeling, PCFG, Training issues; Arguments, and Adjuncts, Probabilistic parsing; inside-outside probabilities, Speech: Phonetics, HMM,, Morphology, Graphical Models for Sequence Labeling in NLP, Phonetics, Consonants (place and, manner of articulation) and Vowels, Forward Backward probability., Unit III, Viterbi Algorithm, Phonology, Sentiment Analysis and Opinions on the Web, Machine Translation and, MT Tools – GIZA++ and Moses, Text Entailment, POS Tagging, Phonology; ASR, Speech Synthesis,, HMM and Viterbi, Precision, Recall, F-score, Map, Semantic Relations; UNL; Towards Dependency, Parsing, Universal Networking Language, Semantic Role Extraction, Baum Welch Algorithm, HMM, training., Text Books:, 1. T. Siddiqui and U.S. Tiwary, Natural Language Processing and Information Retrieval,, 94
Page 95 :
Oxford University Press, 2008., 2. Steven Bird, Ewan Klein, Edward Loper, Natural Language Processing with Python:, Analyzing Text with the Natural Language Toolkit, O'Reilly Media., Reference Books:, 1. James Allen, "Natural Language Understanding", Second Edition, Benjamin/Cumming, 1995., 2. Charniack, Eugene, "Statistical Language Learning", MIT Press, 1993., 3. D. Jurafsky, and J. H. Martin, Speech & Language Processing: An Introduction to Natural, Language Processing, Speech Recognition, & Computational Linguistics, Prentice-Hall, 2000., 4. Manning, Christopher and Heinrich, Schutze, "Foundations of Statistical Natural Language, Processing", MIT Press, 1999., , 95
Page 96 :
CE706 Internetworking Protocol Laboratory, List of Experiments:, 1. Introduction to WireShark and Layered Protocol: Overview, WireShark, Networking Tools,, Layered Protocol, Procedures, Installation, Getting familiar with WireShark, Layered Protocol,, Running WireShark, Networking Tools, Layered Protocol., 2. Ethernet and IEEE 802.11: Objective, Introduction, Ethernet, IEEE 802.1, Procedures and, Discussions, Ethernet, Procedures and Discussions, IEEE 802.11., 3. ARP, IP, and ICMP: Objective, Address Resolution Protocol (ARP), Internet Protocol (IP),, Internet Control Message Protocol (ICMP), Procedures and Discussion: Exploring ARP, Functions, Analyzing IP frames, Exploring ICMP Functions., 4. TCP: Objective, Introduction: TCP Header Format, TCP Connection Setup, TCP Data Flow,, TCP Connection Release, TCP Congestion Control, TCP Flow Control, Re-transmission in TCP,, Procedures and Discussions: TCP Header Format, TCP Connection Setup, TCP Data Flow, TCP, Connection Release, TCP Congestion Control, TCP Flow Control, Re-transmission in TCP, (Optional)., 5. UDP: Capture a Trace, Inspect the Trace, UDP Message Structure, UDP Usage., 6. HTTP: The Basic HTTP GET/response interaction, The HTTP CONDITIONAL GET/response, interaction, Retrieving Long Documents, HTML Documents with Embedded Objects, HTTP, Authentication., 7. DNS: DNS Commands: nslookup, ipconfig, Tracing DNS with Wireshark, Inspect the Trace,, DNS Message Structure, DNS Usage., , CE707 Software Engineering Laboratory, List of experiments:, 1. Give detailed Problem Statement, 2. Perform Software scoping activity, 3. Estimate required Resources, 4. Perform Software Estimation, 5. Perform Risk Analysis and Management, 6. Carry out Project Scheduling and Tracking, 7. Prepare Project Plan, 8. Prepare Software Quality Assurance Plan (SQA plan), 9. Carry out Requirement Analysis Modeling, 10. Carry out Design, 11. Perform Software Testing, , 96
Page 97 :
CE708 Artificial Intelligence Laboratory, State Space Search – Water Jug Problem, Missionaries and cannibals, Tower of HANOI, Eight puzzle,, Implementation of these problems using both uninformed and informed search. – BFS, DFS, Best First, Search, A*., Two-agent Games – Tic-Tac-Toe using Min-Max search and Alpha-Beta pruning, Constraint, Satisfaction Problems – N-Queens using Heuristic repair and constraint propagation., Logic-Unification, Resolution, Answer Extraction Using Resolution., Machine Learning – Decision Tree, Candidate Elimination, Clustering (K-means), Neural net learning, (Perception), Genetic algorithms (2SAT), Expert Systems, Natural Language Processing., , 97
Page 98 :
CE710 Hadoop Platform Development, Course Objectives and Outcomes:, • [HDCO1] To design and develop Hadoop and Map Reduce Framework., • [HDCO2] The basics of Analytics – Concepts, Data preparation – merging, managing missing, numbers sampling, Data visualization, Basic statistics., • [HDCO3] To Developed the skills necessary for utilizing tools (including deploying them on, Hadoop/MapReduce) to handle a variety of big data analytics, and to be able to apply the, analytics techniques on a variety of applications., CO to PO Mapping:, PO1, , PO2, , HDCO1, , x, , x, , x, , HDCO2, , x, , x, , x, , x, , x, , x, , HDCO3, , x, , PO3, , x, , PO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, x, , x, x, , Hadoop Basics: Hadoop Stack Basics, The Apache Framework: Basic Modules, Hadoop Distributed, File System (HDFS), The Hadoop "Zoo", Hadoop Ecosystem Major Components, Apache Hadoop, Ecosystem, Exploring the Cloudera VM., Introduction to the Hadoop Stack: Overview of the Hadoop Stack, The Hadoop Distributed File, System (HDFS) and HDFS2, MapReduce Framework and YARN, The Hadoop Execution, Environment, YARN, Tez, and Spark, Hadoop Resource Scheduling, Hadoop-Based Applications,, Introduction to Apache Pig, Introduction to Apache HIVE, Introduction to Apache HBASE., Introduction to Hadoop Distributed File System (HDFS): Overview of HDFS Architecture, The, HDFS Performance Envelope, Read/Write Processes in HDFS, HDFS Tuning Parameters, HDFS, Performance and Robustness, Overview of HDFS Access, APIs, and Applications, HDFS Commands,, Native Java API for HDFS, REST API for HDFS., Introduction to Map/Reduce: Introduction to Map/Reduce, The Map/Reduce Framework, A, MapReduce Example: Wordcount in detail, debugging map/reduce programs, MapReduce: Intro to, Examples and Principles, MapReduce Example: Trending Wordcount, MapReduce Example: Joining, Data, MapReduce Example: Vector Multiplication, Computational Costs of Vector Multiplication,, MapReduce Summary., Spark: Introduction to Apache Spark, Architecture of Spark, Setup PySpark on the Cloudera VM,, Resilient Distributed Datasets, Spark Transformations, Wide Transformations, Directed Acyclic Graph, (DAG) Scheduler, Actions in Spark, Memory Caching in Spark, Broadcast Variables, Accumulators,, Simple Join in Spark, Advanced Join in Spark., 98
Page 99 :
*Programming assignments are mandatory., Text Books:, 1. The Hadoop – Definitive Guide, Tom White, O’Reilly, 2009., 2. Hadoop for Dummies, Dirk deRoos, Paul C. Zikopoulos, Bruce Brown, Rafael Coss, and, Roman B. Melnyk, Wiley Publication., 3. Eric Sammer, Hadoop Operations A Guide for Developers and Administrators, O'Reilly, Media., Reference Books:, 1. Hadoop in Action, Chuck Lam, Manning Publication., 2. Hadoop in Practice, Alex Holmes, Manning Publication., 3. Learn Spark In A Day, The Ultimate Crash Course to Learning the Basics of Spark In No Time, Authored by Acodemy., 4. Learning Spark, Holden Karau, Andy Konwinski, Patrick Wendell & Matei Zaharia, O’Reilly, Media., , 99
Page 100 :
CE801 Software Quality Assurance (Elective 801), Course Objectives and Outcomes:, • [SQCO1] To understand software quality management process and quality management models., • [SQCO2] To learn software quality metrics, assurance and various software standards., • [SQCO3] To gain the techniques and skills on how to use modern software testing tools to, support software testing projects., • [SQCO4] To train the students to apply quality assurance techniques in different activities of, software development and maintenance., CO to PO Mapping:, PO1, , PO2, , SQCO1, , x, , x, , SQCO2, , x, , x, , SQCO3, , x, , SQCO4, , PO3, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, x, x, , x, , PO4, , x, x, , Principles of Testing: The pesticide paradox, Software Development Life Cycle Model, Phases of, software project, Quality, Quality assurance and quality control, Testing, Verification and validation,, Process models to represent various phases, Life cycle models, Software testing life cycle., White Box Testing (WBT): Static testing: by human, Static Analysis Tool; Structural testing: unit/code, functional testing, Code coverage Testing, code complexity Testing; Challenges in White Box Testing., Black Box Testing: What, Why and When used black box testing How to do Black Box Testing:, Requirement based testing, Positive and negative testing, Boundary value analysis, Decision Tables,, Equivalence Partitioning, State based or graph based testing, Compatibility Testing, Domain Testing., Integration Testing: Integration Testing as a type of testing: Top-down, Bottom-up Integration,, Bi-directional Testing, System Integration, choosing Integration method; As a phase testing; Scenario, testing: System and use case scenario, Defect bash., System and Acceptance Testing: What, Why is system testing done?, Functional Versus Non, Functional testing, Functional system testing: Design/Architecture verification, Business Vertical, Testing, Deployment Testing, Beta Testing, Certification, Standards and Testing for compliance;, Non-functional system testing: setting up the configuration, Coming up with Entry/Exit criteria,, Balance Key Resources, Scalability Testing, Reliability Testing, Stress Testing, Inter-operability, Testing;, Acceptance testing: Acceptance Criteria, Selecting Test Cases, Executing Test cases; Summary of, 100
Page 101 :
Testing Cases., Performance Testing: Introduction, Factor Governing performance Testing, Methodology of, Performance Testing, Tools for Performance Testing, Process for performance Testing., Regression Testing: What and When to do regression Testing, Types, How to do regression testing?, Best Practices in regression testing., Internationalization testing: Introducing, Primer on Internationalization, Test Phases, Enabling, Testing, Local Testing, Internationalization Validation, Fake Language Testing, Language Testing,, Localization Testing, Tools., Ad-hoc Testing: Overview, Buddy Testing, Pair Testing, Exploratory Testing, Iterative Testing, Agile, and Extreme Testing, Defect Seeding., Testing Object Oriented Software: Introduction, Comparison of OO and Procedural software, System, testing example, Unit testing of classes, Tools for testing OO software. Testing Web Application., Text Books:, 1. Paul C. Jorgensen, Software Testing: A Craftsman’s Approach, Fourth Edition, CRC Press., 2. Shriniwasan Desikan, Gopalswamy Ramesh, "Software Testing – Principles and Practices",, Pearson Education., 3. Loise Tamres, "Introducing Software Testing", Pearson Education., 4. Aditya P. Mathur, “Foundations of Software Testing”, Pearson Education, 2008., 5. Cem Kaner, Jack Falk, Hung Quoc Nguyen, Testing Computer Software, 2nd Edition, Wiley, Publication., Reference Books:, 1. Boris Beizer, "Software Testing Techniques", Dream Tech. Publication., 2. Ross Patton, "Software Testing", Pearson Education., 3. Elfriede Dustin, “Effective Software Testing”, First Edition, Pearson Education, 2003., 4. Renu Rajani, Pradeep Oak, “Software Testing – Effective Methods, Tools and Techniques”,, McGraw Hill, 2004., 5. Kshirasagar Naik, Priyadarshi Tripathy, Software Testing and Quality Assurance: Theory and, Practice, Wiley Publication., , 101
Page 102 :
CE801 Software Architecture (Elective 801), Course Objectives and Outcomes:, • [SACO1] To appreciate relationships between system qualities and software architectures., • [SACO2] To understand the software architectural patterns and tactics, and their relationship to, system qualities., • [SACO3] To write software architecture documentation., • [SACO4] To understand architectural reuse via software product lines., CO to PO Mapping:, , SACO1, SACO2, , PO1, , PO2, , x, , x, x, , PO3, , PO4, , PO5, , x, , PO7, , PO8, , PO9, , PO10, , x, x, , SACO3, SACO4, , PO6, , x, , x, , Introduction to Software Architecture, The 4+1 View of Software Architecture, Examples of Software, Architecture, Architecture Design: Quality attributes., Attribute Driven Design; Architecture Centric Software Development Methodology, Design Patterns,, Software Design Function Oriented versus Object Oriented, Documenting Software Architecture, Stakeholders, Views, View-sets, View-based documentation, IEEE 1471, ISO 42010., Architecture Description Languages, Architecture Evaluation, Product line architectures, Enterprise, Architecture, Architecture Knowledge Management., Reference Books:, 1. "Software Architecture in Practice", Len Bass, Paul Clements, Rick Kazman., 2. "Documenting Software Architectures: Views and Beyond", Paul Clements, Felix Bachmann,, Len Bass, David Garlen, James Ivers, Reed Little, Robert Nord and Judith Stafford., 3. Jan Bosch, “Design and Use of Software Architectures”, Addision-Wesley-Pearson Education., 4. Frank Buschmann, Regine Meunier, Hans Rohnert, Peter Sommerlad, MiachelStal, Douglas, Schmidt, “Pattern oriented software architecture”, Volumes 1 &2, Wiley Publication., , 102
Page 103 :
CE802 Data Science with R (Elective 802), Course Objectives and Outcomes:, • [DRCO1] Explain the key differences between the tasks of classification, clustering, regression,, and dimensionality reduction., • [DRCO2] To appreciate supervised and unsupervised learning and their applications., • [DRCO3] Understand concepts around Business Intelligence and Business Analytics., • [DRCO4] Work on a real-life project, implementing supervised and unsupervised machine, learning techniques to derive business insights., • [DRCO5] Propose a suitable visualization design for a particular combination of data, characteristics and application tasks., CO to PO Mapping:, , DRCO1, , PO1, , PO2, , x, , x, , DRCO2, DRCO3, , x, , PO3, , PO4, , PO5, , x, , x, , x, , x, , x, , DRCO4, , x, , x, , x, , x, , DRCO5, , x, , x, , x, , x, , PO6, , PO7, , PO8, , PO9, , PO10, , Data Mining Patterns: Cluster Analysis: K-means Clustering, K-medoids Clustering, Hierarchical, Clustering, Expectation Maximization, Density estimation; Anomaly Detection: Show outliers,, Calculating Anamolies; Association Rules: Mine for Association; Data Mining Sequences: Eclat,, arulesNBMiner, Apriori, Determining Sequences using TraMineR, Similarity in sequences., Text Mining: Text mining, Text Clusters., Data Analysis: Regression Analysis – Simple regression, Multiple Regression, Multivariate Regression, Analysis, Robust Regression, Correlation, Clustering: K-means Clustering, medoids cluster, The, CascadeKM function, selecting cluster based on Bayesian information, Affinity propagation clustering,, Gap Statistic to estimate the number of clusters, Hierarchical clustering., Data Visualization: R graphics – Interactive graphics, The latticist package, The ggplot2 package;, Plotting -Scatter Plots, Bar Charts and Plots; 3D graphics – Lattice Cloud- 3D scatterplot, Big Data,, Research Areas., Machine Learning: Data Partitioning Model, The Train Model, Predicting events with machine, learning – automatic forecasting package; Supervised and Unsupervised learning., , 103
Page 104 :
Reference Books:, 1. Dan Toomey, "R for Data Science", PACKT Publication, First Edition, 2014., 2. Data Science from Scratch: First Principles with Python, O'Reilly Media., 3. Hadley Wickham, Garrett Grolemund, R for Data Science Import, Tidy, Transform, Visualize,, and Model Data, O'Reilly Media., 4. Data Science & Big Data Analytics: Discovering, Analyzing, Visualizing and Presenting Data,, Wiley Publication., 5. Julia Silge, David Robinson, Text Mining with R: A Tidy Approach, O'Reilly Media., , 104
Page 105 :
CE802 Cryptography and Network Security (Elective 802), Course Objectives and Outcomes:, • [NSCO1] To understand the network security, services, attacks, mechanisms, types of attacks., • [NSCO2] To understand cryptographic techniques for encryption, hashing, signature., • [NSCO3] Develop an understanding of security policies (authentication, integrity and, confidentiality), as well as protocols to implement such policies in the form of message, exchanges., • [NSCO4] Deploy the cryptographic techniques to detect and prevent basic security threats., CO to PO Mapping:, PO1, NSCO1, , NSCO4, , PO3, , PO4, , PO5, , x, x, , NSCO2, NSCO3, , PO2, , x, x, , x, , PO6, , PO7, , PO8, , PO9, , x, , x, , x, , x, , x, , x, , x, , x, , x, , x, , PO10, , Introduction and Mathematical Foundations: Introduction, Overview on Modern Cryptography,, Number Theory, Probability and Information Theory., Classical Cryptosystems: Classical Cryptosystems, Crypt-analysis of Classical Cryptosystems,, Shannon’s Theory., Symmetric Key Ciphers: Symmetric Key Ciphers, Modern Block Ciphers (DES), Modern Block, Cipher (AES)., Crypt-analysis of Symmetric Key Ciphers: Linear Crypt-analysis, Differential Crypt-analysis, Other, Crypt-analytic Techniques, Overview on S-Box Design Principles, Modes of operation of Block, Ciphers., Stream Ciphers and Pseudo-randomness: Stream Ciphers, Pseudo-random functions., Hash Functions and MACs: Hash functions: The Merkle Damgard Construction, Message, Authentication Codes (MACs)., Asymmetric Key Ciphers: Construction and Crypt-analysis: More Number Theoretic Results, The RSA, Cryptosystem, Primality Testing, Factoring Algorithms, Other attacks on RSA and Semantic Security of, RSA, The Discrete Logarithm Problem (DLP) and the Diffie Hellman Key Exchange algorithm, The, ElGamal Encryption Algorithm, Crypt-analysis of DLP., , 105
Page 106 :
Digital Signatures: Signature schemes: I, Signature schemes: II., Modern Trends in Asymmetric Key Cryptography: Elliptic curve based cryptography: I, Elliptic curve, based cryptography: II., Network Security: Secret Sharing Schemes, A Tutorial on Network Protocols, Kerberos, Pretty Good, Privacy (PGP), Secure Socket Layer (SSL), Intruders and Viruses, Firewalls., Text Books:, 1. Douglas Stinson, "Cryptography Theory and Practice", 2nd Edition, Chapman & Hall/CRC., 2. B. A. Forouzan, "Cryptography & Network Security", McGraw Hill Publication., 3. William Stallings, "Cryptography and Network Security", Pearson Education., 4. Dr. B. B. Meshram, TCP/IP & Network Security, SPD Publication., Reference Books:, 1. Wenbo Mao, "Modern Cryptography, Theory & Practice", Pearson Education., 2. Hoffstein, Pipher, Silvermman, "An Introduction to Mathematical Cryptography", Springer., 3. Alang.Konheim, Computer Security and Cryptography, Wiley Publication., 4. A. Joux, "Algorithmic Crypt-analysis", CRC Press., 5. S. G. Telang, "Number Theory", McGraw Hill., 6. Matt Bishop, "Computer Security", Pearson Education., , 106
Page 107 :
CE803 Bio-Informatics (Elective 803), Course Objectives and Outcomes:, • [BICO1] To Understand the theoretical basis behind bioinformatics., • [BICO2] To know algorithms and programming techniques like dynamic programming,, hashing, and suffix trees., • [BICO3] To help in developing multidisciplinary approach to the systematic analysis and, modeling of complex biological phenomena., • [BICO4] Serving as an introduction to computational and systems biology, this course, emphasizes the fundamentals of nucleic acid and protein sequence analysis, structural analysis,, and the analysis of complex biological systems., CO to PO Mapping:, PO1, , PO2, , PO3, , PO4, , BICO2, , x, , x, , x, , BICO3, , x, , BICO1, , BICO4, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , x, , x, , x, , x, , x, , x, , Introduction to Bioinformatics: What is a Data Base, Types of Databases, Biological Databases,, Pitfalls of Biological Databases, Information Retrieval from Biological Databases., Pair wise Sequence Alignment: Evolutionary Basics, Sequence homology versus similarity, Sequence, similarity versus Identity, Scoring Matrices, Statistical Significance of Sequence alignment., Database similarity searching: Unique requirement of Database searching, Heuristic Database, searching, Basic alignment search tool: Comparison of FASTA and BLAST, Multiple Sequence, Alignment, Scoring Function, Exhaustive Algorithms, Heuristic Algorithms, Gene Prediction,, Categories of gene prediction programs, Gene prediction in prokaryotes and Eukaryotes, Phylogenetics, Basics Molecular phylogenetics and molecular basics Gene phylogeny versus species phylogeny,, Forms of tree representation, Why finding a true tree is difficult, Phylogenetic tree construction, methods and programs., Protein structure basics: Amino acid, peptide formation, Dihedral Angles, Hierarchy, Secondary, structures, Tertiary structure, Determination of protein 3-D structure, Protein structure data base,, Genome mapping, assembly and comparison, Genome mapping, Genome sequencing, Genome, sequence assembly, Genome Annotation, Comparative genomics, Functional Genomics, Sequence, based approaches, Microarray based approaches, Comparisons of SAGE and DNA micro-array., , 107
Page 108 :
Reference Books:, 1. Jin Xiong, Essential Bioinformatics, 1st Edition, Cambridge University Press, 2011., 2. Arthur M Lesk, Introduction to Bioinformatics, 2nd Edition, Oxford University Press, 2007., 3. "An Introduction to Bioinformatics Algorithms", Jones, Pevzner, MIT Press., 4. Cynthia Gibas, Per Jambeck, Developing Bioinformatics Computer Skills: An Introduction to, Software Tools for Biological Applications, O'Reilly Media., 5. Andreas D. Baxevanis, Bioinformatics A Practical Guide to the Analysis of Genes and, Proteins, Second Edition, Wiley Publication., , 108
Page 110 :
Text Books:, 1. Vijay Madisetti and Arshdeep Bahga, “Internet of Things (A Hands-on-Approach)”, 1st, Edition, VPT, 2014, 2. Honbo Zhou, "The Internet of Things in the Cloud: A Middleware Perspective”, CRC, Press-2012., 3. Dieter Uckelmann, Mark Harrison, “Architecting the Internet of Things”, Springer-2011., 4. Olivier Hersent, David Boswarthick, Omar Elloumi, “The Internet of Things–Key, applications and Protocols”, Wiley, 2012., 5. Dirk Slama, Frank Puhlmann, Jim Morrish, Rishi M Bhatnagar, Enterprise IoT: Strategies, and Best Practices for Connected Products and Services, O'Reilly Media., Reference Books:, 1. Luigi Atzori, Antonio Lera, Giacomo Morabito, “The Internet of Things: A Survey”, Journal, on Networks, Elsevier Publications, October, 2010., 2. Francis daCosta, “Rethinking the Internet of Things: A Scalable Approach to Connecting, Everything”, 1st Edition, Apress Publications, 2013., 3. Cuno Pfister, Getting Started with the Internet of Things, O‟Reilly Media., 4. Nitesh Dhanjani, Abusing the Internet of Things: Blackouts, Freakouts, and Stakeouts,, O'Reilly Media., 5. Simon Monk, Raspberry Pi Cookbook, 2nd Edition, Software and Hardware Problems and, Solutions, O'Reilly Media., , 110
Page 111 :
CE803 Cyber Law, Course Objectives and Outcomes:, • [CLCO1] Critically evaluate ongoing developments in law relating to Information, Technologies., • [CLCO2] Display an understanding of how these developments relate to one another., • [CLCO3] Examine areas of doctrinal and political debate surrounding rules and theories., • [CLCO4] Evaluate those rules and theories in terms of internal coherence and practical, outcomes., • [CLCO5] Draw on the analysis and evaluation contained in primary and secondary sources., CO to PO Mapping:, PO1, , PO2, x, , CLCO1, CLCO2, , x, , CLCO3, , x, , PO3, , PO4, , PO5, , x, , PO6, , PO7, , PO8, , PO9, , x, , x, , PO10, , x, , x, , CLCO4, , x, , x, , x, , CLCO5, , x, , x, , x, , Unit I, Internet, E-Commerce And E-Governance With Reference To Free Market Economy, Understanding Computers, Internet and Cyber Laws, Conceptual Framework of E-commerce:, E-governance, The Role of Electronic Signatures in E-commerce with Reference to Free Market, Economy in India., Unit II, Law Relating To Electronic Records And Intellectual Property Rights In India, Legal Aspects of Electronic Records/Digital Signatures, The Rules and Regulations of Certifying, Authorities in India, Protection of Intellectual Property Rights in Cyberspace in India., Unit III, International Efforts Relating To Cyberspace Laws And Cyber Crimes, International Efforts Related to Cyberspace Laws, Council of Europe (COE) Convention on Cyber, Crimes., Unit IV, Penalties, Compensation And Offenses Under The Cyberspace And Internet In India, Penalties, Compensation and Adjudication of Violations of Provisions of IT Act and Judicial Review,, Some Important Offenses under the Cyberspace Law and the Internet in India, Other Offenses under, 111
Page 112 :
the Information Technology Act in India., Unit V, Miscellaneous Provisions Of It Act And Conclusions, The Role of Electronic Evidence and the Miscellaneous Provisions of the IT Act, Information, Technology Act as Amended up to 2008, The Information Technology (Certifying Authorities) Rules,, 2000, The Information Technology (Certifying Authorities) Rules, 2000, Ministerial Order on Blocking, of Websites., Reference Books:, 1. Harish Chander, Cyber Laws and It Protection, PHI Publication., 2. Faiyaz Ahamad, KLSI, Cyber Law and Information Security, Dreamtech Press., 3. Murray, Information Technology Law: Law and Society, 3rd Edition, Oxford University Press,, Oxford 2016., 4. Sunit Belapure Nina Godbole, Cyber Security, Wiley India Pvt. Ltd., 5. Vivek Sood, Cyber Law Simplified, McGraw-Hill Publication., , 112
Page 113 :
CE804 Principles of Management (Elective 804), Introduction to management theory, Characteristics of management, Management as an art –, profession, Systems approach to management, Task and responsibilities of a professional manager,, Levels of managers and skill required. Management process – planning – mission – objectives – goals, – strategy – policies – programmes – procedures., Organizing – principles of organizing – organization structures, Directing – delegation – span of, control – leadership – motivation – communication, Controlling., Decision making process – decision making under certainty – risk – uncertainty – models of decision, making, Project management – critical path method – programme evaluation and review technique –, crashing., Introduction to functional areas of management, Operations management, Human resources, management, Marketing management, Financial management., Text Books:, 1. Koontz H., and Weihrich H., Essentials of Management: An International Perspective, 8th, Edition, McGraw Hill Publication, 2009., 2. Hicks, Management: Concepts and Applications, Cengage Learning, 2007., 3. Mahadevan B., Operations Management: Theory and Practice, Pearson Education Asia,, 2009., 4. Kotler P., Keller K. L, Koshy A., and Jha M., Marketing Management, 13th Edition, 2009., 5. Khan M.Y., and Jain P.K., Financial Management, McGraw-Hill Publication, 2008., , 113
Page 114 :
CE604 Business Intelligence, Business Intelligence Introduction: Definition, Leveraging Data and Knowledge for BI, BI, Components, BI Dimensions, Information Hierarchy, Business Intelligence and Business Analytics. BI, Life Cycle. Data for BI – Data Issues and Data Quality for BI., BI Implementation: Key Drivers, Key Performance Indicators and operational metrics, BI, Architecture/Framework, Best Practices, Business Decision Making., Business Analytics: Objective Curve, Web Analytics and Web Intelligence, Customer Relationship, Management., Business/Corporate Performance Management: Dash Boards and Scorecards, Business Activity, Monitoring, Six Sigma., Advanced BI: Big Data and BI, Social Networks, Mobile BI, emerging trends., Working with BI Tools: Pentaho etc., Overview of managerial, strategic and technical issues associated with Business Intelligence and Data, Warehouse design, implementation, and utilization. Critical issues in planning, physical design process,, deployment and ongoing maintenance., Data Warehousing (DW): Introduction & Overview; Data Marts, DW architecture – DW components,, Implementation options; Meta Data, Information delivery., ETL: Data Extraction, Data Transformation – Conditioning, Scrubbing, Merging, etc., Data Loading,, Data Staging, Data Quality., Dimensional Modeling: Facts, dimensions, measures, examples; Schema Design – Star and, Snowflake, Fact constellation, Slow changing Dimensions., OLAP: OLAP Vs OLTP, Multi-Dimensional Databases (MDD); OLAP – ROLAP, MOLAP, HOLAP;, Data Warehouse Project Management: Critical issues in planning, physical design process,, deployment and ongoing maintenance., Reference Books:, 1. Efraim Turban, Ramesh Sharda, Jay Aronson, David King, Decision Support and Business, Intelligence Systems, 9th Edition, Pearson Education, 2009., 2. David Loshin, Business Intelligence – The Savy Manager's Guide Getting Onboard with, Emerging IT, Morgan Kaufmann Publishers, 2009., , 114
Page 115 :
CE804 National Service Scheme (NSS-II) (Elective 804), Unit 1, Citizenship, Basic Features of Constitution of India, Fundamental Rights and Duties, Human Rights, Consumer, awareness and the legal rights of the consumer, RTI., Unit 2, Health, Hygiene & Sanitation, Definition, Needs and scope of health education, Food and Nutrition, Safe drinking water, Water borne, diseases and sanitation, National Health Programme, Reproductive health, Healthy Lifestyles, HIV, AIDS, Drugs and Substance abuse, Home Nursing, First Aid., Unit 3, Youth and Yoga, History, Philosophy and concept of Yoga, Myths and misconceptions about yoga, Different Yoga, traditions and their Impacts Yoga as a preventive, pro-motive, and curative method, Yoga as a tool for, healthy lifestyle., Unit 4, Environment Issues, Environment conservation, Enrichment and Sustainability, Climate change, Waste management,, Natural resource management, Rain water harvesting, Energy conservation, Waste land development,, Soil conversations and forestation., Unit 5, Disaster a Management, Introduction to Disaster Management, Classification disaster, Role of youth in Disaster Management., Unit 6, Youth and crime, Sociological and psychological factors influencing youth crime, Peer mentoring in preventing crime,, Awareness about anti-ragging, Cybercrime and its prevention, Juvenile justice., Reference Books:, 1. National Service Scheme Manual (Revised) 2006, Government of India, Ministry of Youth, Affairs and Sports, New Delhi., 2. University of Mumbai National Service Scheme Manual, 2009., 3. Avhan Chancellor’s Brigade – NSS Wing, Training camp on Disaster Preparedness Guidelines,, March 2012., 4. Rashtriya Seva Yojana Sankalpana – Prof. Dr. Sankay Chakane, Dr. Pramod Pabrekar, Diamond, Publication, Pune., 5. National Service Scheme Manual for NSS District Coordinators, National Service Scheme Cell,, Dept. of Higher and Technical Education, Mantralaya., 115
Page 117 :
CE807 Continuous Integration, Course Objectives And Outcomes:, • [CICO1] Set up and navigate a CI environment that enables automated testing & automated, builds., • [CICO2] Execute releases in test environments prior to product delivery., • [CICO3] Identify the most efficient CI tools for quick release & reliable maintenance of, products., • [CICO4] Integrate Continuous Integration methods & techniques into current workflow for a, SCM environment, CO to PO Mapping:, , CICO1, CICO2, , PO1, , PO2, , x, , x, x, , CICO3, CICO4, , x, , PO3, , PO4, , x, , x, , x, , x, , x, , x, , PO5, , PO6, , PO7, , PO8, , PO9, , PO10, , Unit I, Build Software at Every Change, Features of CI: Source Code Compilation, Database Integration,, Testing, Inspection, Deployment, Documentation and Feedback., What Is the Value of CI?, What Prevents Teams from Using CI?, How Do I Get to “Continuous”, Integration?, When and How Should a Project Implement CI?, The Evolution of Integration, How Does, CI Complement Other Development Practices?, How Long Does CI Take to Set Up?, CI and You,, Commit Code Frequently, Don’t Commit Broken Code, Fix Broken Builds Immediately, Write, Automated Developer Tests, All Tests and Inspections Must Pass, Run Private Builds, Avoid Getting, Broken Code., Unit II, Risk: Lack of Deployable Software, Risk: Late Discovery of Defects, Risk: Lack of Project Visibility,, Risk: Low-Quality Software., Automate Builds, Perform Single Command Builds, Separate Build Scripts from Your IDE, Centralize, Software Assets, Create a Consistent Directory Structure, Fail Builds Fast, Build for Any Environment,, Build Types and Mechanisms, Use a Dedicated Integration Build Machine, Use a CI Server, Run, Manual Integration Builds, Run Fast Builds, Stage Builds, How Will This Work for You?., Unit III, Automate Database Integration, Use a Local Database Sandbox, Use a Version Control Repository to, 117
Page 118 :
Share Database Assets, Continuous Database Integration, Give Developers the Capability to Modify the, Database, The Team Focuses Together on Fixing Broken Builds, Make the DBA Part of the, Development Team, Database Integration and the Integrate Button., Automate Unit Tests, Automate Component Tests, Automate System Tests, Automate Functional Tests,, Categorize Developer Tests, Run Faster Tests First, Write Tests for Defects, Make Component Tests, Repeatable, Limit Test Cases to One Assert., Unit IV, Release Working Software Any Time, Any Place, Label a Repository’s Assets, Produce a Clean, Environment, Label Each Build, Run All Tests, Create Build Feedback Reports, Possess Capability to, Roll Back Release., All the Right Stuff: The Right Information, The Right People, The Right Time, The Right Way; Use, Continuous Feedback Mechanisms: E-mail, SMS (Text Messages), Ambient Orb and X10 Devices,, Windows Taskbar, Sounds, Wide-Screen Monitors., Unit V, CI Resources: Continuous Integration Web Sites/Articles, CI Tools/Product Resources, Build Scripting, Resources, Version Control Resources, Database Resources, Testing Resources, Automated Inspection, Resources, Deployment Resources, Feedback Resources, Documentation Resources., Evaluating CI Tools: Considerations When Evaluating Tools, Functionality, Compatibility with Your, Environment, Reliability, Longevity, Usability, Automated Build Tools, Build Scheduler Tools., Unit VI, Tools for Continuous Integration: Lab sessions with Devops or Jenkin, Reference Books:, 1. Paul M. Duvall, Steve Matyas and Andrew Glover, Continuous Integration: Improving Software, Quality and Reducing Risk, Addison-Wesley., 2. John Ferguson Smart, Jenkins: The Definitive Guide: Continuous Integration for the Masses,, O'Reilly Media., 3. Len Bass, Ingo Weber, Liming Zhu, DevOps: A Software Architect's Perspective, Pearson, Education., , 118
Page 119 :
Lesson Plans, SEMESTER – III, Course: Digital Circuits, Week, , 1, , 2, , 3, , 4, , 5, , 6, , Lecture No., , Topic, , 1, , Binary number system, Signed binary numbers, Binary arithmetic,, Decimal number system, , 2, , Hexadecimal number system, Octal number system, Arithmetic, operations using 1’s complement, 2’s complement, , 3, , Arithmetic operations using 9’s complement, 10’s complement, , 4, , Codes: Numeric codes, Weighted and non-weighted codes, , 5, , Codes: Sequential codes, Self complimenting codes, , 6, , Codes: Cyclic codes, Reflective codes, BCD code, , 7, , Codes: Excess-3 code, Gray code, Error detecting and correcting codes, , 8, , Numericals On Above Topics, , 9, , Introduction to analog and digital signal, Logic gates and switching, functions: AND, OR, NOT, , 10, , EX-OR, EX-NOR, NAND, NOR. Implementation of universal gates, using logic gates, , 11, , De Morgan’s theorem, Boolean algebra, , 12, , Representation of logic functions using POS form, , 13, , Representation of logic functions using SOP form, , 14, , Minimization of completely and incompletely specified switching, functions Karnaugh map (2,3,4,5,6 variable), , 15, , Minimization of completely and incompletely specified switching, functions Karnaugh map (2,3,4,5,6 variable), , 16, , Numerical On Above Topics, , 17, , Quine – McCluskey method, TTL and CMOS logic families, , 18, , Half and full adder, Half and full subtractor, , 19, , Binary parallel adder, Binary parallel subtractor, , 20, , Look ahead carry header, BCD to 7-segment decoder, , 21, , Binary to Gray code converter, Gray to Binary code converter, , 22, , Numericals On Above Topics, , 23, , Multiplexer, Demultiplexer, , 24, , BCD arithmetic: BCD adder, BCD subtractor, 119
Page 120 :
7, , 8, , 9, , 10, , 25, , Arithmetic logic unit, Digital comparators, , 26, , Parity generators. Design of PAL, , 27, , Design of PLA, Design of PROM, , 28, , Numericals On Above Topics, , 29, , Comparison between sequential and combinational circuit,, Synchronous sequential circuits and asynchronous sequential circuits, , 30, , Registers, Shift registers, Counters: asynchronous counters and, synchronous counters, , 31, , Sequential circuit’s implementation. Flip flops: Edge triggered, flip-flops, S-R flip flop, , 32, , Flip flops: -K flip flop, T flip flop, D flip flop., , 33, , Flip flops Conversions, , 34, , Flip flops Conversions, , 35, , Regular expressions using FSM, Optimization using FSM, , 36, , Reduction of states, Mealy Machines, , 37, , Moore Machines, Representation of sequential circuits using ASM, charts, , 38, , Synthesis of output and next state functions, , 39, , Data path and control path, , 40, , Partition-based design, Course: Digital Circuits, , Week, , 1, , 2, , Lecture No., , Topic, , 1, , Fundamental Structures and Basic Logic: Introduction to set, and various basic definition, , 2, , Venn Diagram and examples on Venn diagram, Algebra of set, operation and numerical, , 3, , Cartesian product, Power sets, Cardinality and countability, Numerical, on Cardinality, , 4, , Propositional logic, Logical connectives, Truth tables, Normal Forms, , 5, , Validity, Predicate logic, Universal and existential quantification, , 6, , Numerical On Above Topics, , 7, , Numerical On Above Topics, , 8, , Functions and Relations: Subjective, Injective, Bijective and inverse, functions., , 9, , Composition of function, Reflexivity, Symmetry, Transitivity and, 120
Page 121 :
equivalence relations, 3, , 4, , 5, , 6, , 7, , 8, , 9, , 10, , 10, , Numerical on Function and Relations, , 11, , Numerical on Function and Relations, , 12, , Numerical on Function and Relations, , 13, , Combinatorics: Counting, , 14, , Recurrence relations, , 15, , generating functions, , 16, , Numerical On Above Topics, , 17, , Numerical On Above Topics, , 18, , Graph Theory: Basic terminology, Multi graphs and weighted graphs, , 19, , Paths and circuits, Shortest path problems, , 20, , Euler and Hamiltonian paths, Representation of graph, , 21, , Isomorphic graphs, Planar graphs, , 22, , Numerical On Above Topics, , 23, , Numerical On Above Topics, , 24, , Numerical On Above Topics, , 25, , Trees: Rooted trees, Path length in rooted tree, Basic Terminology in, Tree, , 26, , Binary search trees, , 27, , Spanning trees and cut set, , 28, , Minimal spanning trees, , 29, , Kruskal's algorithms for minimal spanning tree, , 30, , Prim's algorithms for minimal spanning tree, , 31, , Matching Coloring, , 32, , Numerical On Above Topics, , 33, , Numerical On Above Topics, , 34, , Algebraic Systems: Algebraic systems, , 35, , Groups, Semi group, Monoid, Subgroup, , 36, , Isomorphism and homomorphism, Rings and fields, Lattices, , 37, , Boolean lattices, Boolean algebra, , 38, , Numerical On Above Topics, , 39, , Numerical On Above Topics, , 40, , Numerical On Above Topics, , 121
Page 122 :
Course: Computer Architecture and Organization, Week, , 1, , 2, , 3, , 4, , 5, , 6, , Lecture No., , Topic, , 1, , Concept of computer organization and architecture, Fundamental unit, , 2, , Computer function and interconnection, CPU structure and function, , 3, , Instruction Sets: Characteristics, Types of operands, Types of, operations, , 4, , Assembly language, Addressing modes,, , 5, , Instruction format, Types of instruction, Instruction execution, , 6, , Machine state and processor status, Structure of program, , 7, , Introduction to RISC and CISC architecture, , 8, , The arithmetic and logic Unit, , 9, , Integer representation, , 10, , Integer arithmetic, , 11, , Floating-point representation, , 12, , Floating-point arithmetic, , 13, , Introduction of arithmetic co-processor, , 14, , Internal Memory: Semiconductor main memory, , 15, , Error correction, , 16, , Advanced DRAM organization, , 17, , Virtual memory systems and cache memory systems, , 18, , External Memory: Organization and characteristics of magnetic disk,, Magnetic tape, , 19, , Optical memory, RAID, , 20, , Memory controllers, , 21, , Control unit operation: Micro-operations, , 22, , Control of the processor, , 23, , Hardwired implementation, , 24, , Micro – programmed Control Unit: Basic concepts, , 25, , Micro-instruction sequencing, , 26, , Micro-instruction execution, , 27, , Applications of micro-programming, , 122
Page 123 :
7, , 8, , 9, , 10, , 28, , External devices, I/O module, , 29, , Programmed I/O, , 30, , Interrupt driven I/O, , 31, , Direct memory access, , 32, , I/O channels and processors, , 33, , External interface, , 34, , Instruction pipelining: Concepts, , 35, , Parallel processing: Multiple processor organization, , 36, , Symmetric multiprocessor, , 37, , Cache coherence, , 38, , MESI protocol, Course: Numerical Methods, , Week, , 1, , 2, , 3, , 4, , Lecture No., , Topic, , 1, , Bisection method, , 2, , Iterative method, , 3, , Condition of convergence and order of convergence, , 4, , Regula Fasli method, , 5, , Newton Raphson method, , 6, , Horner's method, , 7, , Solution of simultaneous linear algebraic equations, , 8, , Gauss elimination method, , 9, , Gauss elimination method, , 10, , Condition of convergence of iteration method, , 11, , Gauss Jacobi method, , 12, , Gauss Seidel method, , 13, , Simple problem, , 14, , Interpolation with equal intervals, , 15, , Newton forward interpolation formula, , 16, , Newtons backward interpolation formula, , 17, , Stirling's formula central interpolation, , 18, , Bessels formula central interpolation, , 19, , Interpolation with unequal intervals, 123
Page 124 :
5, , 6, , 7, , 8, , 9, , 10, , 20, , Divided difference, , 21, , Newton's divided difference method, , 22, , Lagrange's interpolation formula, , 23, , Lagrange's formula for inverse interpolation, , 24, , Numerical integration, , 25, , Numerical integration, , 26, , Trapezoidal rule, , 27, , Simposon's 1/3 rule, , 28, , Simposon's 3/8 rule, , 29, , Weddle's rule, , 30, , Solution to ordinary differential first order equations, , 31, , Solution to ordinary differential first order equations, , 32, , Taylor's series, , 33, , Taylor's series, , 34, , Euler's method, , 35, , Improved Euler's method, , 36, , Runge kutta 2 and 4 th order, , 37, , Runge kutta 2 and 4 th order, , 38, , Simple problem, , Course: Probability, Statistics And Queueing Theory, Week, , 1, , 2, , Lecture No., , Topic, , 1, , General Discussion on Syllabus, , 2, , Definition of probability: classical, empirical and axiomatic approach, of probability, , 3, , Permutation and combination theorems, , 4, , Problems based on Permutation and Combination, , 5, , Classical and empirical probability and solved problems from solved, examples, , 6, , Axiomatic probability, addition theorem of probability, theorem of, compound probability, , 7, , Numerical on axiomatic probability and on compound probability, , 8, , Inverse Probability and solved numerical on it, , 9, , Random variables, probability distribution of discrete random variable,, 124
Page 125 :
examples on random variable, 3, , 4, , 5, , 6, , 7, , 8, , 10, , Numerical on random variable, , 11, , Mathematical Expectation, theorems on Expectation, variance of x in, term of Expectation, , 12, , Covariance and numerical on expectation, variance and Covariance., , 13, , Numerical on expectation, variance and Covariance, , 14, , Binomial probability distribution, mean and variance, numerical on, binomial probability distribution., , 15, , Numerical on binomial distribution, , 16, , Mode of binomial distribution, Fitting of binomial distribution,, Numerical on binomial distribution and fitting of binomial distribution, , 17, , Derivation of Poisson distribution from binomial distribution, mean, and variance in Poisson distribution, , 18, , Mode in Poisson Distribution, numerical on Poisson Distribution, , 19, , Numerical on Poisson distribution, , 20, , Fitting of Poisson distribution, numerical on Poisson distribution, , 21, , Normal probability, standard normal variate, properties of normal, probability curve, , 22, , Area under normal probability curve, How to compute area under, normal probability curve, computation of area to right and left of, ordinates at X=a, , 23, , Numerical on Normal distribution, , 24, , Correlation analysis, types of correlation, Karl Pearson's coefficient, correlation., , 25, , Numerical on Karl Pearson's Coefficient of correlation, , 26, , Numerical on Karl Pearson's Coefficient of correlation, properties of, Karl Pearson's Coefficient of correlation., , 27, , Numerical on properties of Karl Pearson's Coefficient of correlation., , 28, , Properties of Karl Pearson's Coefficient of correlation. Numerical on, properties of Karl Pearson's Coefficient of correlation., , 29, , Probable error, numerical on it, rank correlation method, computation, of rank correlation methods, numerical on when rank is given., , 30, , Numerical on when rank is not given and on repeated ranks., , 31, , Introduction, Linear and non-linear regression, Lines of regression, , 32, , Derivation of line of regression of y on x and x on y, Angle between, the regression lines, , 33, , Linear regression analysis, line of regression, 125
Page 126 :
9, , 10, , 34, , Numerical on linear regression analysis, line of regression, , 35, , Numerical on linear regression analysis, line of regression, , 36, , Coefficients of regression, Theorems on regression coefficient,, Properties of regression coefficient, , 37, , Introduction, Queuing systems, The input or arrival pattern, The, service pattern and service discipline, Notation, Performance measures, , 38, , Relation between the probabilities of states, M/M/1/∞ systems, , 39, , Numerical on Queueing Theory, , 40, , Numerical on Queueing Theory, Course: Object Oriented Programming in C++, , Week, , 1, , 2, , 3, , 4, , 5, , Lecture No., , Topic, , 1, , Introduction to Object Oriented Programming: Need of object oriented, programming, The object oriented approach, , 2, , Differentiate between OOPs and POP, Bottom up and Top down, , 3, , Characteristics of object oriented languages, , 4, , CLASS, , 5, , Objects as data types, , 6, , Constructors, , 7, , Destructor, , 8, , Objects as function arguments, , 9, , Returning objects, , 10, , Overloading unary operators, , 11, , Overloading binary operators, , 12, , Data conversion, , 13, , Derived and base class, , 14, , Public and private inheritance, , 15, , Levels of inheritance, Single Inheritance Examples, , 16, , Multilevel Inheritance Examples, , 17, , Multiple Inheritance Examples, , 18, , Hierarchical Inheritance Examples, Hybrid Inheritance Examples, , 19, , Constructors in derived class, , 20, , Virtual Function, , 21, , Dynamic binding, 126
Page 127 :
6, , 7, , 8, , 9, , 10, , 22, , Operator Overriding, , 23, , Abstract classes and pure virtual functions, , 24, , Friend functions, this pointer, , 25, , Streams and File, , 26, , Stream output and input, Stream manipulators, , 27, , Stream manipulators, , 28, , Creating, Reading sequential and random files, , 29, , Updating sequential and random files, , 30, , File Position Pointer, , 31, , Function templates, Overloading function templates, , 32, , Class template, , 33, , Exception handling overview, Need of exceptions, , 34, , An exception example, Multiple Exception, Exception specifications., , 35, , Introduction to STL-Containers, , 36, , Iterators, , 37, , Algorithms, Sequence containers, , 38, , Associative containers, Course: Operating System, , Week, , 1, , 2, , 3, , Lecture No., , Topic, , 1, , Introduction and Operating system, Definition, General Discussion on, Operating system, , 2, , Types of Operating system, , 3, , Real-Time operating system, , 4, , System Components- System Services, , 5, , Systems Calls, , 6, , System Programs, , 7, , System structure, , 8, , Virtual Machines, System Design and Implementation, , 9, , System Generations, , 10, , Process Concept, , 11, , Process Scheduling, , 12, , Operation on a process, 127
Page 128 :
4, , 5, , 6, , 7, , 8, , 9, , 10, , 13, , Cooperating processes, , 14, , Threads, Inter-process Communication, , 15, , Scheduling criteria, , 16, , Scheduling Algorithms (FCFS), , 17, , Scheduling Algorithms (SJF), , 18, , Scheduling Algorithms (RR), , 19, , Multiple-Processor Scheduling, , 20, , Real-Time Scheduling, , 21, , Scheduling Algorithms and performance evaluation, , 22, , The critical-section problem, , 23, , Critical regions, , 24, , Synchronization Hardware, , 25, , Semaphores, , 26, , Classical Problems of synchronization, , 27, , Monitors Synchronizations in Solaris, , 28, , Systems Model, , 29, , Deadlock Characterization, Methods for handling Deadlocks, , 30, , Deadlock Prevention, Deadlock Avoidance, , 31, , Deadlock Detection, Recovery from Deadlock, Combined approach to, deadlock Handling, , 32, , Introduction, Basic concepts of Memory, Logical versus Physical, address space, Swapping, , 33, , Contiguous allocation, Paging, Segmentation with Paging, Demand, Paging, , 34, , Page Replacement Algorithms, , 35, , Page Replacement Algorithms, Thrashing, , 36, , File System, Secondary storage devices, , 37, , Secondary storage devices, Real-Time Operating Systems, , 38, , Real-time Linux, , 39, , Case Studies: MS-DOS, , 40, , Case Studies: UNIX, , 128
Page 129 :
SEMESTER – V, Course: Database Management System, Week, , 1, , 2, , 3, , 4, , 5, , 6, , Lecture No., , Topic, , 1, , Introduction to DBMS: Historical perspective, File Versus a DBMS, , 2, , Advantages of DBMS, Describing and storing data in DBMS, , 3, , Architecture of a DBMS, Different Data Models, , 4, , Introduction to the Relational Model: Structure of Relational, Databases, Database Schema, Keys, , 5, , Schema Diagrams, Relational Query Languages, Relational Operations, , 6, , Database Design and the E-R Model: features of ER model, conceptual, design using ER model, , 7, , Design for large enterprises, Relational model-structure and, operations, Integrity constraints over relations, Extended E-R Features, , 8, , Examples on ER Diagrams, , 9, , Query Language: Overview, SQL Data Definition, Basic Structure of, SQL Queries, , 10, , Additional Basic Operations, Set Operations, Null Values, Aggregate, Functions, , 11, , Nested Subqueries, Modification of the Database, Join Expressions,, Views, Integrity Constraints, , 12, , SQL Data Types and Schemas, Authorization, Functions and, Procedures, Triggers, , 13, , Examples on SQL, , 14, , Relational Algebra, , 15, , Tuple Relational Calculus, , 16, , Domain Relational Calculus, , 17, , Closer of functional dependencies, closer of attributes, , 18, , Canonical cover and Properties of Decomposition, , 19, , Normalization: 1NF, 2NF, , 20, , Normalization: 3NF and BCNF, , 21, , Multivalued dependency:, dependency and 4NF, , 22, , Database Application Development: Accessing Databases from, Applications, An Introduction to JDBC, , 23, , JDBC Classes and Interfaces, Statement,, 129, , Closer, , properties, , of, , Multi-valued
Page 130 :
7, , 8, , 9, , 10, , 24, , prepared Statement, , 25, , callable Statement, , 26, , SQLJ, Stored Procedures, , 27, , Overview of Physical Storage Media, Magnetic Disk and Flash, Storage, , 28, , RAID, Tertiary Storage, , 29, , File Organization, Organization of Records in Files, , 30, , Data-Dictionary Storage, Database Buffer, , 31, , Intuition For Tree Indexes, Indexed Sequential Access Method (ISAM), , 32, , B+ Trees: A Dynamic Index Structure, Search, Insert, , 33, , B+ Trees: Delete, Duplication, B+ Trees in Practice, , 34, , Static Hashing, Extendable Hashing, Linear Hashing, Extendable vs., Linear Hashing, , 35, , Examples on B+ Trees, , 36, , Overview of Query Evaluation, operator evaluation, Algorithms for, relational operations: Selection operation, , 37, , Algorithms for relational operations: General selection condition,, Projection operation, Join operation, set operation and aggregate, operation, Evaluation of relational operations, , 38, , Alternative plans, functions of query optimizer, , 39, , Translating SQL queries into relational algebra, , 40, , estimating the cost of a plan, relational algebra equivalences, and other, approaches to query optimization, Course: Design and Analysis of Algorithm, , Week, , 1, , 2, , Lecture No., , Topic, , 1, , Algorithm Design, Specifications, Analysis Need and Introduction, , 2, , Complexity, Asymptotic Notations (Big O Notation, Theta and, Omega), , 3, , Time Complexity calculation examples, , 4, , Recurrences, Homogeneous Recurrences Examples, , 5, , Non-Homogeneous Recurrences Examples and problems, , 6, , Recursion tree and examples, , 7, , Master theorem, recursion tree and Proof, , 8, , Heap Sort, 130
Page 131 :
3, , 4, , 5, , 6, , 7, , 8, , 9, , 9, , Divide and Conquer strategy, Definition, Introduction, general, examples, , 10, , Binary search analysis, Minimum and Maximum Analysis, , 11, , Merge Sort, , 12, , Quick Sort, , 13, , Strassen's matrix multiplication algorithm, , 14, , Introduction to Greedy Technique, Greedy Method, , 15, , Optimal Merge Patterns, , 16, , Huffman Coding, , 17, , Knapsack Problem, , 18, , Activity Selection Problem, , 19, , Job Sequencing with Deadline, , 20, , Minimum Spanning Tree, , 21, , Single-Source Shortest Path Algorithm, , 22, , Introduction to dynamic programming, steps, elements in dynamic, programming, Comparison of Divide-and-Conquer and Dynamic, Programming Techniques, , 23, , Longest Common Sub-sequence, , 24, , Matrix chain multiplication problem, , 25, , Bellman Ford shortest path algorithm, , 26, , Floyd Warshall shortest path algorithm, Application of Dynamic, Programming, , 27, , Backtracking Concept, N–Queens Problem, , 28, , Four–Queens Problem, , 29, , Eight-Queens Problem, , 30, , Hamiltonian Cycle, Sum of Subsets Problem, Graph Coloring Problem, , 31, , Introduction to Branch and Bound, Traveling Salesperson Problem, , 32, , Traveling Salesperson Problem, , 33, , 15-Puzzle Problem, Comparisons between Backtracking and Branch, and Bound, , 34, , Introduction to Tree, B-Tree: Insertion, , 35, , B-Tree: Deletion, , 36, , Red-Black Tree: Insertion, , 37, , Red-Black Tree: Deletion, , 38, , Introduction to NP completeness, P- class problem, NP-problem, 131
Page 132 :
10, , 39, , Reduction, optimization, NP complete, , 40, , NP hard problems, NP hard graph problems, Course: Theory of Computation, , Week, , 1, , 2, , 3, , 4, , 5, , 6, , Lecture No., , Topic, , 1, , Definition of deterministic finite automata, Non deterministic finite, automata, , 2, , Examples on DFA, , 3, , Mealy Machine and examples on Mealy Machine, , 4, , Moore Machine and examples on Moore Machine, , 5, , Conversion between Moore to Mealy Machine, , 6, , Conversion between Mealy to Moore Machine, , 7, , Regular expressions, Recursive definition, , 8, , NFA with e-moves, Inter-conversion between NFA and DFA, , 9, , Regular expression and FA, , 10, , Pumping lemma and numeric based on Pumping Lemma, , 11, , Definition of Production rules, Ambiguous grammar, , 12, , Removal of ambiguity and its numeric, , 13, , Chomsky hierarchy, , 14, , Context Free Grammar (CFG) – definition, Simplification of CFG, , 15, , Numeric based on simplification of CFG, , 16, , Removal of Unit Productions, Chomsky Normal Form for CFG and, numeric based on it, , 17, , Definition of context free languages, Regular grammar definition, , 18, , Left linear, Right linear grammar, Inter-conversion between left linear, and right linear regular grammar, , 19, , Inter conversion between left linear and right linear regular grammar, , 20, , Regular grammar and finite automata, , 21, , Inter-conversion between Type 0 and Type 1 grammars, , 22, , Derivation graphs, , 23, , CNF, GNF, , 24, , DFSA TO Regular Expressions, , 25, , Formal definition, Pushdown automata (PDA), definition of NPDA, and DPDA, 132
Page 133 :
26, , Equivalence between acceptance by empty store and Acceptance by, final state, , 27, , Equivalence between Pushdown automata and context-free grammars, , 28, , Relative powers of DPDA and NPDA, , 29, , The definition of a Turing machine, Computing with Turing machine, , 30, , Techniques of TM construction, , 31, , TM as acceptor and i/o device, , 32, , Church-Turing hypothesis and its foundation implications, , 33, , Halting problems – Universal TM-recursive and recursively, enumerable sets, , 34, , Problems on TM, , 35, , Problems on TM, , 36, , Applications of RE and FA – Lexical analyzer Text editor and, searching using RE, , 37, , Applications of PDA – Expression conversion, , 38, , Applications of CFG–syntax analysis, Language definition, , 7, , 8, , 9, , 10, , Course: Object Oriented Analysis and Design, Week, , 1, , 2, , 3, , Lecture No., , Topic, , 1, , An Overview of Object Oriented Systems development, , 2, , Object Basics: Objects are grouped in classes, Attributes, Object, behavior and methods, Object respond to messages, , 3, , Encapsulation and information hiding, Class hierarchy, polymorphism, , 4, , Object relationships and association, Aggregation and object, containment, Advanced topics, , 5, , Object Oriented Systems development life cycle, , 6, , Software development process, Building high quality Software, , 7, , Object Oriented Systems development: a use case driven approach,, reusability, , 8, , Methodology, Modeling and Unified Modeling Language: Rambaugh, et al.'s Modelling Technique, Booch Methodology, , 9, , Jacobson et al. Methodologies, , 10, , Patterns: Generative and nongenerative, Pattern Template, Anti, patterns, Capturing Patterns, , 11, , Frameworks, A Unified approach, , 12, , UML, Static and dynamic models, UML class diagram, 133
Page 134 :
4, , 5, , 6, , 7, , 8, , 9, , 10, , 13, , Use Case diagram, UML dynamic modeling, , 14, , Model management, UML Extensibility, UML meta model, , 15, , OOA process: Why analysis is difficult activity, Business object, Analysis, Use case Driven OOA, , 16, , Use case model, Developing effective documentation, , 17, , Case Study, , 18, , Object analysis classification, Noun Phrase approach, , 19, , Common class pattern approach, Use case driven approach, , 20, , Classes, responsibilities and collaborators, Naming classes, , 21, , Identifying object relationships, Identifying attributes, , 22, , Identifying methods, , 23, , Object Oriented design process and axioms, , 24, , Object Oriented design process and axioms, Design patterns, , 25, , Design classes, , 26, , Design attributes, Design methods, , 27, , Access layer object storage and object interoperability, , 28, , Access layer object storage and object interoperability, , 29, , Database Management Systems, , 30, , Logical and physical database organization and access control, , 31, , Logical and physical database organization and access control, , 32, , Distributed databases and client server computing, , 33, , OODBMS, Object Relational Systems, , 34, , Multidatabase systems, , 35, , Design access layer classes, , 36, , Case Study, , 37, , View layer: Designing interface objects, , 38, , The purpose of view layer interface, , 39, , Prototyping and user interface, , 40, , Case Study, , 134
Page 135 :
SEMESTER – VI, Course: Database Implementation Techniques, Week, , 1, , 2, , 3, , 4, , 5, , 6, , 7, , 8, , 9, 10, , Lecture No., , Topic, , 1, , Introduction to DBMS: Advantages of DBMS, File Processing System, and Data Abstraction, , 2, , Database Languages, Data Independence, , 3, , Component and overall structure of DBMS, , 4, , Multi-user DBMS Architecture, , 5, , Transaction management: Basic Concept of Transaction Management, , 6, , Properties of Transaction, Concept of Schedule, , 7, , Serial Schedule, , 8, , Stabilizability: Conflict and view serializability, , 9, , Cascaded aborts and recoverability, , 10, , Recoverable and non-recoverable schedule, , 11, , Concurrency control: Needs and locking method, , 12, , Deadlocks and time-stamping method, , 13, , Optimistic techniques, , 14, , Multi version concurrency control, , 15, , Different crash recovery method such as shadow paging and lock, based, , 16, , Recovery: Deferred and immediate, , 17, , Checkpoints and its implementation, , 18, , Introduction to File System and Query processing, , 19, , File System: File organization, , 20, , Organization of records in file, indices, , 21, , Static and dynamic hashing, , 22, , B Tree and B+ tree, , 23, , Introduction to query processing: overview and measure of query cost, , 24, , Selection and join operation, , 25, , Introduction to query optimization, , 26, , Transformation of relational expression, , 27, , Object oriented database and database architecture: need of OODBMS, , 28, , Storing object in relational database, Introduction to OO data model, 135
Page 136 :
11, , 29, , Persistent programming language, Pointers swizzling techniques, , 30, , Centralized and client-server architecture, 2-tier architecture, 3-tier, architecture, , 31, , Distributed Database System, Data Mining Using Association Rule, , 32, , data warehousing, Data Warehousing and it's component, , 33, , Real Time Example Of Data Mining And Data, Warehouse, , 136
Page 137 :
SEMESTER – VIII, Week, , 1, , 2, , 3, , 4, , 5, , 6, , 7, , 8, , 9, , Lecture No., , Course: Internetworking Protocol, Topic, , 1, , Review of Network, , 2, , Introduction to Internetworking technologies, , 3, , Architectural model for Internetworking, , 4, , Internet properties, , 5, , Internetworking through IP router, , 6, , Internet Addresses, Mapping Internet addresses to Physical addresses,, Universal identifiers, , 7, , IP address classes, , 8, , Resolution through direct mapping, dynamic binding, , 9, , ARP packet format, , 10, , RARP packet format, , 11, , Internet datagram: connection-less delivery, , 12, , Routing of IP datagram, , 13, , Direct and Indirect packet delivery, , 14, , Next hop, default, host specific routing, , 15, , Need of ICMP in TCP/IP, , 16, , Subnet and Supernet Addresses, , 17, , Error reporting vs error detection, , 18, , ICMP message format, , 19, , Detecting and reporting various network problems through ICMP, , 20, , Transparent router, ARP proxy, , 21, , Different error reporting messages in ICMP, , 22, , Introduction to UDP, UDP message format, , 23, , UDP pseudo header, encapsulation, , 24, , UDP check-sum computation, , 25, , UDP multiplexing and demultiplexing, , 26, , Need of reliable stream delivery, Ports, , 27, , Connections and end points, passive and active open, , 28, , TCP segment format, , 29, , TCP segment format, 137
Page 138 :
10, , 30, , Week, , Lecture No., , 1, , 2, , 3, , 4, , 5, , 6, , 7, , 8, , 9, , 10, , TCP state transition diagram, TCP implementation issues, Course: Software Architecture, Topic, , 1, , Definitions of Software Architecture, , 2, , Software Architecture Examples, , 3, , Describing Software Architectures, Architecture Viewpoints, , 4, , IEEE Standard, , 5, , Architecture Description Languages, Rapide, ACME, UML, , 6, , Architectural Abstractions, , 7, , Architectural Patterns, , 8, , Architectural Patterns, , 9, , Quality Attributes and Architectures, , 10, , Architecture Design Engineering Methods, , 11, , Deriving Architecture From Requirements, , 12, , Deriving OO Designs from Architectures, , 13, , Architecture and Implementation, , 14, , Executable Architecture Languages, , 15, , Recovering Architecture From Programs, , 16, , Module View, , 17, , OO View, , 18, , Architecture Evaluation, , 19, , Processes and Methods, , 20, , Processes and Methods, , 21, , Architecture Decisions, , 22, , Architecture Decisions, , 23, , Architecture Knowledge Management, , 24, , Architecture Knowledge Management, , 25, , Technology Architecture CORBA, , 26, , J2EE/.NET, , 27, , GAE/Struts, , 28, , Formal languages for Architecture Description, , 29, , Formal languages for Architecture Description, , 30, , Model Driven Architecture, 138
Page 139 :
11, , 31, , Service Oriented Architecture, , 32, , Software Architecture and Enterprise Architecture, , 33, , Architecture-Centric SE Processes/ Risk, Management/ Cost Estimation/ Software Testing, , 34, , Product Line Architecture, , 35, , Domain Specific Architecture, , 36, , Event-Driven Architecture, , 139, , Analysis/, , Project
Page 140 :
Week, , 1, , 2, , 3, , 4, , 5, , 6, , 7, , Lecture No., , Topic, , 1, , Introduction and History of Internet, Discussion on syllabus, , 2, , Client-Server Models, DNS, , 3, , Telnet, FTP, , 4, , HTTP and working of HTTP with respect to browser and web server, , 5, , HTTP Commands, WWW Architecture, , 6, , Introduction to HTML and its basic tags (table, anchor, image), , 7, , Building a form, Text fields and value, size, maxlength, html buttons,, radio, check boxes, prechecked, Selection lists, , 8, , HTML Embedded Multimedia tags, , 9, , Introduction to CGI Script, Action and Method-GET and POST, , 10, , HTML form interface with CGI scripts, , 11, , Introduction to Java, jdk, jre, Classes and Object, , 12, , Examples on Classes and Objects, , 13, , Introduction to Apache Tomcat and its directory structure, add tomcat, in Eclipse, , 14, , Introduction to JDBC, Different JDBC API and its syntax, , 15, , Statement API and its program in JAVA, , 16, , Prepared Statement API and its program in JAVA, , 17, , Callable Statement API and its program in JAVA, procedure and, function., , 18, , Web server and Application server, , 19, , ArrayList and its different methods with programs, compare ArrayList, and Array, , 20, , Package in JAVA and programs based on it., , 21, , Introduction to python and its History, interpreter and compiler, types, of errors, , 22, , Variables, expressions, and statements: Values and types, Variables,, Variable names and keywords, Statements, Operators and operand,, Expressions, Order of operations, Asking the user for input, , 23, , Conditional execution: Boolean expressions, Logical operators,, Conditional execution, Alternative execution, Nested conditionals,, Chained conditionals, Catching exceptions using try and except., , 24, , Functions: Function calls, Built-in functions, Type conversion, functions, Random numbers, Math functions, Adding new functions,, , 8, , 140
Page 141 :
Parameters and arguments., , 9, , 25, , Iteration: Updating variables, The while statement, Infinite loops,, “Infinite loops” and break, Definite loops using for, Finishing, iterations with continue, , 26, , Strings: len method, Traversal through a string with a loop, string, slice, Strings are immutable, Looping and counting, The in operator,, String comparison, string methods, Parsing strings, Format operator., , 27, , Files: Opening files, Text files and lines, Reading files, Searching, through a file, Letting the user choose the file name, Using try, except,, and open, Writing files., , 28, , Lists: Lists are mutable, Traversing a list, List operations, List slices,, List methods, Deleting elements, Lists and functions, Lists and string,, Parsing lines, List arguments., , 29, , Dictionaries: Dictionaries and files, Looping and dictionaries,, Advanced text parsing., , 30, , Tuples: Tuples are immutable, Comparing tuples, Tuple assignment,, Dictionaries and tuples, Multiple assignment with dictionaries,, Sequences: strings, lists, and tuples., , 10, , 141
 Learn better on this topic
Learn better on this topic