Notes of I BCom, ECOMMERCE And WEB DESIGN E COMMERCE AND WEB DESIGNING UNIT II STUDY MATERIAL - Study Material
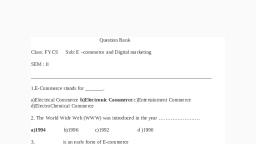
Page 1 :
UNIT-2, E-PAYMENT SYSTEM, Electronic payment system:, E-commerce sites use electronic payment, where electronic payment refers to paperless, monetary transactions. Electronic payment has revolutionized the business processing by, reducing the paperwork, transaction costs, and labor cost. Being user friendly and less timeconsuming than manual processing, it helps business organization to expand its market, reach/expansion. Listed below are some of the modes of electronic payments −, •, •, •, •, •, , Credit Card, Debit Card, Smart Card, E-Money, Electronic Fund Transfer (EFT), , Credit Card, Payment using credit card is one of most common mode of electronic payment. Credit card is, small plastic card with a unique number attached with an account. It has also a magnetic strip, embedded in it which is used to read credit card via card readers. When a customer purchases a, product via credit card, credit card issuer bank pays on behalf of the customer and customer has, a certain time period after which he/she can pay the credit card bill. It is usually credit card, monthly payment cycle. Following are the actors in the credit card system., •, •, •, •, •, , The card holder − Customer, The merchant − seller of product who can accept credit card payments., The card issuer bank − card holder's bank, The acquirer bank − the merchant's bank, The card brand − for example , visa or Mastercard., , Credit Card Payment Process, Step, , Description, , Step 1, , Bank issues and activates a credit card to the customer on his/her, request., , Step 2, , The customer presents the credit card information to the merchant site, or to the merchant from whom he/she wants to purchase a
Page 2 :
product/service., Step 3, , Merchant validates the customer's identity by asking for approval from, the card brand company., , Step 4, , Card brand company authenticates the credit card and pays the, transaction by credit. Merchant keeps the sales slip., , Step 5, , Merchant submits the sales slip to acquirer banks and gets the service, charges paid to him/her., , Step 6, , Acquirer bank requests the card brand company to clear the credit, amount and gets the payment., , Step 6, , Now the card brand company asks to clear the amount from the issuer, bank and the amount gets transferred to the card brand company., , Debit Card, Debit card, like credit card, is a small plastic card with a unique number mapped with the bank, account number. It is required to have a bank account before getting a debit card from the bank., The major difference between a debit card and a credit card is that in case of payment through, debit card, the amount gets deducted from the card's bank account immediately and there should, be sufficient balance in the bank account for the transaction to get completed; whereas in case, of a credit card transaction, there is no such compulsion., Debit cards free the customer to carry cash and cheques. Even merchants accept a debit card, readily. Having a restriction on the amount that can be withdrawn in a day using a debit card, helps the customer to keep a check on his/her spending., Smart Card, Smart card is again similar to a credit card or a debit card in appearance, but it has a small, microprocessor chip embedded in it. It has the capacity to store a customer’s work-related, and/or personal information. Smart cards are also used to store money and the amount gets, deducted after every transaction., Smart cards can only be accessed using a PIN that every customer is assigned with. Smart cards, are secure, as they store information in encrypted format and are less expensive/provides faster, processing. Mondex and Visa Cash cards are examples of smart cards.
Page 3 :
E-Money, E-Money transactions refer to situation where payment is done over the network and the amount, gets transferred from one financial body to another financial body without any involvement of a, middleman. E-money transactions are faster, convenient, and saves a lot of time., Online payments done via credit cards, debit cards, or smart cards are examples of emoney, transactions. Another popular example is e-cash. In case of e-cash, both customer and merchant, have to sign up with the bank or company issuing e-cash., Electronic Fund Transfer, It is a very popular electronic payment method to transfer money from one bank account to, another bank account. Accounts can be in the same bank or different banks. Fund transfer can, be done using ATM (Automated Teller Machine) or using a computer., Nowadays, internet-based EFT is getting popular. In this case, a customer uses the website, provided by the bank, logs in to the bank's website and registers another bank account. He/she, then places a request to transfer certain amount to that account. Customer's bank transfers the, amount to other account if it is in the same bank, otherwise the transfer request is forwarded to, an ACH (Automated Clearing House) to transfer the amount to other account and the amount is, deducted from the customer's account. Once the amount is transferred to other account, the, customer is notified of the fund transfer by the bank., , Digital Signature:, What is a digital signature?, A digital signature—a type of electronic signature—is a mathematical algorithm routinely used, to validate the authenticity and integrity of a message (e.g., an email, a credit card transaction, or, a digital document). Digital signatures create a virtual fingerprint that is unique to a person or, entity and are used to identify users and protect information in digital messages or documents. In, emails, the email content itself becomes part of the digital signature. Digital signatures are, significantly more secure than other forms of electronic signatures., Why would you use a digital signature?, Digital signatures increase the transparency of online interactions and develop trust between, customers, business partners, and vendors., How do digital signatures work?, Familiarize yourself with the following terms to better understand how digital signatures work:, •, , Hash function – A hash function (also called a “hash”) is a fixed-length string of, numbers and letters generated from a mathematical algorithm and an arbitrarily sized file
Page 4 :
•, , •, , •, , •, , •, , such as an email, document, picture, or other type of data. This generated string is unique, to the file being hashed and is a one-way function— a computed hash cannot be reversed, to find other files that may generate the same hash value. Some of the more popular, hashing algorithms in use today are Secure Hash Algorithm-1 (SHA-1), the Secure, Hashing Algorithm-2 family (SHA-2 and SHA-256), and Message Digest 5 (MD5)., Public key cryptography – Public key cryptography (also known as asymmetric, encryption) is a cryptographic method that uses a key pair system. One key, called the, public key, encrypts the data. The other key, called the private key, decrypts the data., Public key cryptography can be used several ways to ensure confidentiality, integrity, and, authenticity. Public key cryptography can, o Ensure integrity by creating a digital signature of the message using the sender’s, private key. This is done by hashing the message and encrypting the hash value, with their private key. By doing this, any changes to the message will result in a, different hash value., o Ensure confidentiality by encrypting the entire message with the recipient’s public, key. This means that only the recipient, who is in possession of the corresponding, private key, can read the message., o Verify the user’s identity using the public key and checking it against a certificate, authority., Public key infrastructure (PKI) – PKI consists of the policies, standards, people, and, systems that support the distribution of public keys and the identity validation of, individuals or entities with digital certificates and a certificate authority., Certificate authority (CA) – A CA is a trusted third party that validates a person’s, identity and either generates a public/private key pair on their behalf or associates an, existing public key provided by the person to that person. Once a CA validates, someone’s identity, they issue a digital certificate that is digitally signed by the CA. The, digital certificate can then be used to verify a person associated with a public key when, requested., Digital certificates – Digital certificates are analogous to driver licenses in that their, purpose is to identify the holder of a certificate. Digital certificates contain the public key, of the individual or organization and are digitally signed by a CA. Other information, about the organization, individual, and CA can be included in the certificate as well., Pretty Good Privacy (PGP)/OpenPGP – PGP/OpenPGP is an alternative to PKI. With, PGP/OpenPGP, users “trust” other users by signing certificates of people with verifiable, identities. The more interconnected these signatures are, the higher the likelihood of, verifying a particular user on the internet. This concept is called the “Web of Trust.”, , Digital signatures work by proving that a digital message or document was not modified—, intentionally or unintentionally—from the time it was signed. Digital signatures do this by, generating a unique hash of the message or document and encrypting it using the sender’s private, key. The hash generated is unique to the message or document, and changing any part of it will, completely change the hash., Once completed, the message or digital document is digitally signed and sent to the recipient., The recipient then generates their own hash of the message or digital document and decrypts the, sender’s hash (included in the original message) using the sender’s public key. The recipient
Page 5 :
compares the hash they generate against the sender’s decrypted hash; if they match, the message, or digital document has not been modified and the sender is authenticated., Why should you use PKI or PGP with digital signatures?, Using digital signatures in conjunction with PKI or PGP strengthens them and reduces the, possible security issues connected to transmitting public keys by validating that the key belongs, to the sender, and verifying the identity of the sender. The security of a digital signature is almost, entirely dependent on how well the private key is protected. Without PGP or PKI, proving, someone’s identity or revoking a compromised key is impossible; this could allow malicious, actors to impersonate someone without any method of confirmation., Through the use of a trusted third party, digital signatures can be used to identify and verify, individuals and ensure the integrity of the message., As paperless, online interactions are used more widely, digital signatures can help you secure, and safeguard the integrity of your data. By understanding and using digital signatures, you can, better protect your information, documents, and transactions., Digital signatures legal position in India:, Digital signatures were given legal status in India, by Information Technology (IT ACT 2000) in, the year 2000. It granted e-signatures on electronic documents, the same legal status as the, handwritten signatures on physical documents. The IT Act 2000 applies to whole of India and it, provides for enabling a person to use digital signature just like the traditional signature. The, basic purpose of digital signature is same as a conventional signature, ie to authenticate the, document, to identify the person and to make the contents of the document binding on person, putting digital signature. Under Indian law, a written signature is not necessarily required for a, valid contract - contracts are generally valid if legally competent parties reach an agreement,, whether they agree verbally, electronically or in a physical paper document. The Information, Technology Act, 2000 (IT Act) specifically confirms that contracts cannot be denied, enforceability merely because they are concluded electronically., Though most electronic documents are allowed to be signed digitally, there are few exceptions, that need to be executed using handwritten signatures. These documents are:, •, •, •, •, •, , a negotiable instrument as defined in section 13 of the Negotiable Instruments Act, 1881, (such as promissory note or bill of exchange);, a power-of-attorney as defined in section 1A of the Powers-of-Attorney Act, 1882;, a trust deed as defined in section 3 of the Indian Trusts Act, 1882;, a will as defined in clause (h) of section 2 of the Indian Succession Act, 1925 including, any other testamentary disposition by whatever name called;, a contract for the sale or conveyance of immovable property or any interest in such, property, , “Digital signature” is defined under section 2(p) of IT Act 2000 as follows: "Digital Signature", means authentication of any electronic record by a subscriber by means of an electronic method, or procedure in accordance with the provisions of section 3;
Page 6 :
Payment Gateway:, , A payment gateway is a technology used by merchants to accept debit or credit card purchases, from customers. The term includes not only the physical card-reading devices found in brickand-mortar retail stores but also the payment processing portals found in online stores. However,, brick-and-mortar payment gateways in recent years have begun accepting phone-based payments, using Near Field Communication (NFC) technology., KEY TAKEAWAYS, •, •, , Payment gateways are the consumer-facing interfaces used to collect payments., In physical stores, payment gateways consist of the point of sale (POS) terminals used to, accept payments by card or by phone., • In online stores, payment gateways are the “checkout” portals used to enter credit card, information or credentials for services such as PayPal., How Payment Gateways Work, The payment gateway is a key component of the electronic payment processing system, as it is, the front-end technology responsible for sending customer information to the merchant acquiring, bank, where the transaction is then processed., Payment gateway technologies are always evolving to reflect new consumer tastes and technical, capacities. In the past, terminals would accept credit cards using magnetic strips, which would, require paper signatures from the customer. With the development of chip technologies, the, signature phase could be removed in favor of a personal identification number (PIN) entered, directly into the payment gateway. Today, contactless purchases are also available, with many, customers now using their phones as a payment device instead of plastic credit cards., Of course, the architecture of a payment gateway will differ depending on whether it is an instore gateway or an online payment portal. Online payment gateways will require application, programming interfaces (APIs) that allow the website in question to communicate with the, underlying payment processing network. In-store payment gateways will utilize a POS terminal, that connects to the payment processing network electronically using either a phone line or an, Internet connection., Example of a Payment Gateway, Merchants can gain access to payment gateway systems through merchant acquiring bank, partnerships, or else they can select their own payment gateway system. Large banks such as, Bank of America (BAC) and JPMorgan Chase (JPM) have sophisticated payment gateway, systems that they offer to customers along with their own merchant acquiring bank services., Ultimately, merchants can choose a variety of payment gateway technologies as long as they are, compatible with the merchant acquiring bank that is being used for payment processing., One recent example of a payment gateway is Square (SQ), which emphasizes flexible mobile, payments for retail businesses. The company’s Square Reader technology allows customers to
Page 7 :
easily accept payments at ad-hoc locations such as conventions or farmer’s markets, or through, roaming storefronts such as food trucks., With the Square Reader payment gateway technology, a merchant can attach a small piece of, hardware to their mobile phone which allows the customer to swipe their payment card for, processing through the mobile phone’s electronic connection. The Square Reader sends the, payment information to a merchant’s acquiring bank which then processes the information for, the merchant momentarily., It is likely that new products will continue to increase the versatility and speed of payment, gateways in the years ahead, as technology and consumer habits continue to evolve., Online banking:, What is online banking?, Online banking, also known as internet banking, describes online systems that provide users, access to their personal bank account information and functions, including but not limited to, account transactions and balances., Deeper definition, Practically every major bank offers its customers the option to sign up for online banking. Online, banking is increasingly popular with customers thanks to its convenience. The service helps, customers keep track of their spending so that they don’t overdraft their accounts or spend too, much money. Customers can sign into online banking anywhere that they have internet access, and a computer. Some of the financial tasks customers can complete using online banking, include:, •, •, •, •, •, •, , Viewing account balances, Researching account transactions, Paying bills, Transferring money between accounts, Obtaining old bank statements, Completing basic account maintenance, , One of the most common services that comes with online banking is an online bill-pay function., With it, account holders have the ability to pay their bills without ever having to write checks. To, pay a bill, the customer only needs a few pieces of information, including the payee’s address, and any account number associated with the payee. Depending on the recipient of the check, the, bank may transfer the funds electronically or mail an actual check. Customers can even set up, recurring payments for their regular monthly bills., Banks advise their customers to keep their login information confidential to protect their, finances. When signing into online banking, customers should use a secure internet connection., Many banks offer a two-step security process that requires customers to verify their identities
Page 8 :
before the online system grants them access to account information; customers are encouraged to, utilize this option if possible to keep their details safe., Online banking example, A customer wishes to use online banking to better monitor her spending trends and pay bills., After signing up, she signs into the online banking portal using her designated username and, password. The customer can now access her bank account information at any time of the day to, check her balances (as long as the system isn’t down for maintenance)., AUTOMATED CLEARING HOUSE, The Automated Clearing House (ACH) is a nationwide batch-oriented electronic funds transfer, system that provides for the distribution and settlement of electronic credits and debits among, financial institutions. The ACH network was initially developed in the early 1970s in response to, the tremendous growth of check payments and the many technological advances in the midtwentieth century. It functions as an efficient, electronic alternative to checks. The ACH system, provides a low cost clearing and settlement system for high volume, non-urgent funds transfers., It is a batch-processing store and forward system. Transactions received by the financial, institution during the day are stored and processed later in a batch mode. Rather than sending, each payment separately, ACH transactions are accumulated and sorted by destination for, transmission during a predetermined time period. Typical ACH settlement is one or two days, after processing, ACH settlement is the actual transfer of the value of funds between financial institutions to, complete the payment instruction of an ACH entry. Initially, the ACH system was used for, recurring funds transfers between known counterparties for payments such as payroll direct, deposit. The ACH system now supports an increasing number of one-time transfers, such as, online debits (Internet Initiated Entries), and has also expanded to international ACH payments., The ACH system supports a wide variety of corporate, individual, and government payment, needs, How Does An Automated Clearing House (ACH) Work To Process Payments?, When funds are being transferred, there is one person, company or entity that makes the payment, and another that is paid. They are called the Originator and the Receiver., Other ACH Process Terminology:, ACH Debit or ACH direct debit – When a customer authorizes the merchant to pull the funds, from their account., ACH Credit – If the funds are deposited or pushed into the Receiver’s account., Originating depository financial institution (ODFI) – the interface between the Originator and the, ACH Operator (the Federal Reserve or The Clearing House) to initiate the transaction.
Page 9 :
Receiving depository financial institution (RDFI) – receives entries from the ACH Operator and, posts them to the receiver’s account., ACH operator – receives the batch of ACH transactions from the originator’s ODFI. The batches, are sorted and the transactions made available to the recipient’s RDFI., The ACH Process Flow, , The organization that is requesting the payment – either to send or receive funds needs the bank, account information of the other party. In the above example, the Receiver initiates the, transaction by granting authorization to the Originators who issue the ACH credit or debit, request., Once the authorization has been received, the Originator creates an ACH entry and sends it to the, originating institution. The entry is distributed to the ACH Operator who continues the process, by distributing the file to the receiving institution. At this stage, the Receiver’s account will be, debited or credited depending on the type of transaction involved., , ACH Payments – What Are The Benefits To Merchants?, Although it may not suit every payment situation, especially if speed is an issue or the payment, is international, ACH can be the ideal choice for many transactions.
Page 10 :
Cost – There are a number of different parties involved in the processing of a credit card, transaction. A large part of the cost is the Interchange fee set by the credit card networks. An, ACH transaction deals directly with the banking network and has a much lower Interchange fee, and costs merchants significantly less than a credit card transaction., Convenience – ACH payments are electronic, so there is less paperwork for the merchant to, manage and the customers can set up payments electronically on a schedule., Customer Experience – There are customers that may not have or may not want to use their, credit card for payment. ACH offers merchants an alternative payment method to offer these, customers and a way of increasing sales that may not have occurred., Chargebacks – Customers have up to 120 days to dispute a credit card payment, this is 90 days, for an ACH payment. There are also only a few instances where a customer can initiate a, chargeback; either the payment was never authorized or the transaction was processed earlier, than authorized, or for a different amount than authorized., , RISKS IN E-PAYMENTS:, Electronic payments allow you to transfer cash from your own bank account to the bank, account of the recipient almost instantaneously. This payment system relies heavily on the, internet and is quite popular due to the convenience it affords the user. It would be hard to, overstate the advantages of electronic payment systems, but what about the risks? Certainly, they exist, both for financial institutions and consumers., The Risk of Fraud, Electronic payment systems are not immune to the risk of fraud. The system uses a particularly, vulnerable protocol to establish the identity of the person authorizing a payment. Passwords, and security questions aren’t foolproof in determining the identity of a person. So long as the, password and the answers to the security questions are correct, the system doesn’t care who’s, on the other side. If someone gains access to your password or the answers to your security, question, they will have gained access to your money and can steal it from you., The Risk of Tax Evasion, The law requires that businesses declare their financial transactions and provide paper records, of them so that tax compliance can be verified. The problem with electronic systems is that, they don’t fit very cleanly into this paradigm and so they can make the process of tax, collection very frustrating for the Internal Revenue Service. It is at the business’s discretion to, disclose payments received or made via electronic payment systems in a fiscal period, and the, IRS has no way of knowing if it’s telling the truth or not. That makes it pretty easy to evade, taxation.
Page 11 :
The Risk of Payment Conflicts, One of the idiosyncrasies of electronic payment systems is that the payments aren’t handled by, humans but by an automated electronic system. The system is prone to errors, particularly, when it has to handle large amounts of payments on a frequent basis with many recipients, involved. It’s important to constantly check your pay slip after every pay period ends in order, to ensure everything makes sense. Failure to do this may result in payment conflicts caused by, technical glitches and anomalies., The Risk of Impulse Buying, Impulse buying is already a risk that you face when you use non-electronic payment systems. It, is magnified, however, when you’re able to buy things online at the click of a mouse. Impulse, buying can become habitual and makes sticking to a budget almost impossible.
 Learn better on this topic
Learn better on this topic